Adding to this layer of security and anonymity is the use of cryptocurrency to make transactions on the darknet. Silk Road, which emerged in 2011, combined TOR and bitcoin to become the first known darknet market. The market was eventually seized in 2013, and the founder, Ross Ulbricht, was sentenced to two life sentences plus 40 years without the possibility of parole. Ulbricht’s hefty prison sentence did not appear to have the intended deterrent effect.

Frequently Asked Questions (FAQs) About Dark Web Marketplaces
Fill out the form to speak with our team about investigative professional services. Never log in with your real name or reuse passwords from other accounts. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Ransomware and cryptocurrency-based crimes saw a significant increase in 2023, with a nearly $176 million rise compared to 2022. Further market diversification occurred in 2015, as did further developments around escrow and decentralization.
DNM vendors take their first dip into the vendor pool through a step-by-step process. It begins with building trust within the darknet community, gaining reputation through smaller transactions, and gradually expanding their offerings. Vendors utilize secure communication channels, employ stealth techniques, and establish a solid customer base. They prioritize quality, reliability, and discretion to thrive in the competitive darknet market. By carefully navigating this path, vendors establish themselves as trusted players and become an integral part of the darknet ecosystem. Interestingly, the rise of social media as an emerging drug market has also impacted purchasing trends.
Join us on a captivating journey as we explore the clandestine nature of Darknet Market Operations, revealing the challenges, risks, and motivations driving this shadowy realm. To do this, we first identified 30 darknet markets advertising stolen data products. We found several thousand vendors selling tens of thousands of stolen data products on 30 darknet markets. These vendors had more than $140 million in revenue over an eight-month period.
- Steven Chase was caught by the FBI after inadvertently revealing the real internet address of the site.
- This made it a legitimate address where they could be reasonably sure that kids didn’t live.
- We found several thousand vendors selling tens of thousands of stolen data products on 30 darknet markets.
- A look with the Tor browser at a darknet directory such as the uncensored Hidden Wiki reveals that seemingly anything goes on the darknet.
Prioritize Escrow
Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor. The VPN’s encryption will hide from your ISP the fact that you’re using Tor. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites. VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes.
What Is The Darknet And What Does It Have To Do With Bitcoin?
Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences. If all the evidence from the arrest and search warrant is dismissed, there is no case. It’s like playing chess with someone who has all their pawns turned into queens. Thus, in most cases, the United States Attorney refuses to go to the hearing. If they feds cut open the package and spot the contents within, they put the suspected vendor on surveillance.
Cypher Marketplace
Multiple markets emerged to fill the void and, in doing so, created a thriving ecosystem profiting from stolen personal data. Policing involves targeting specific activities of the private web deemed illegal or subject to internet censorship. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers.
How To Access The Dark Web Safely Step-by-Step In 2024
These sex offenders are called “chomos” in federal prison and “pedos” on the darknet and elsewhere. Darknet vendors understand the importance of building a strong online presence and positive reputation. They leverage customer reviews, forums, and word-of-mouth marketing to attract more buyers. Positive feedback and a reliable reputation increase customer trust, driving sales and profitability.
Can I Use Tor To Browse The Surface Web?
It advised people to be cautious as there was a dangerous batch of drugs, specifically fentanyl, circulating. “Do not drink and type” is one of the best mottos in the darknet market operations. The darknet vendors consider this to be even more dangerous than drinking and driving. Complacency happens when you become comfortable with someone, like when two people know each other for a few years on IRC. Then, one gets drunk one night and the other calls him by their username. It’s like that situation, but on the darknet, where the other could potentially be an undercover agent.
What Are The Scams Done By Some Vendors On The Darknet Markets
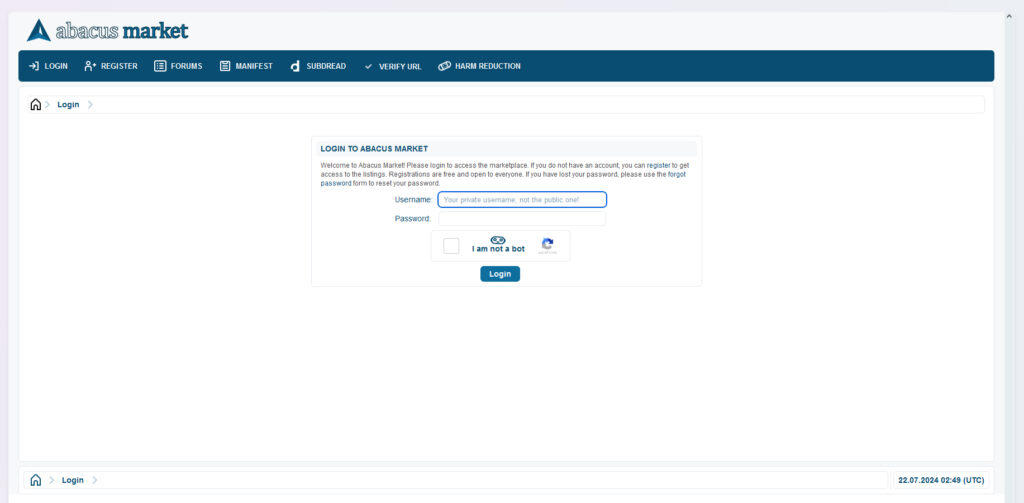
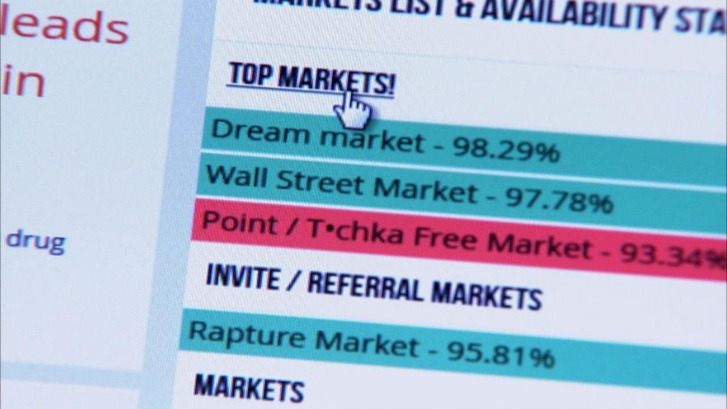
Over the years, dozens of large DNMs have been established and eventually shut down by law enforcement, including AlphaBay, Dream Market, Wall Street, and, most recently, Hydra. DNMs are located on the “darknet,” which is unreachable on standard internet browsers like Chrome, Firefox, or Safari because the darknet is unindexed. There are certain sites on the darknet (and on clearnet) which attempt to manually track and publish sites on the darknet, but common browsers do not link directly to darknet. An example of dark pool stock trading can be quoted when an executive of a large company decides to sell 50% of his shares. He knows that this would directly impact the company he’s working for because this is a large number of shares, and his position would attract media attention to the trade.
In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information. Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication. The significance here is the preservation of civil liberties and the right to information. Businesses operating in such regions may need to adapt to the technical challenges and risks posed by using darknets for legitimate purposes. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases.
However, it has always been the security plan for the dark web vendors in the darknet market operations from the beginning. They make the maze so complex that the law enforcement would have to jump over a wall to catch them. It’s like what you see on Law & Order, where they break the law and everything they found is considered invalid. The drug vendors find it interesting how criminals avoid certain things for ethical reasons. The vendors could never run a darknet marketplace because it would stress them out and have negative effects on their health.
The criminal groups that developed the malware gets a cut of the affiliates’ earnings, typically between 20% and 30%. IBM estimates that REvil’s profits in the past year were $81 million. The affiliates distribute the ransomware packages through the dark web. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid. We’re back with another video in our Webz Insider video series on everything web data. What most of us think of as the World Wide Web is in fact only the ‘surface’ (also known as the ‘open’ or ‘clear’) web and is quite literally just the tip of the web ‘iceberg’.


