You can access DuckDuckGo on the surface web, but a Tor version is also available. You’ll get...
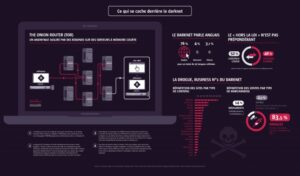
These websites use complex addresses ending in “.onion” instead of familiar “.com” endings. The surface you see...
The BBC news website has a special .onion site, which you need to access via the dark...
Benzodiazepines are medications that have anti-anxiety-producing properties. It’s always best to start with a low dose and...
The majority of the users on the dark web use the Tor (The Onion Router) browser. A...
Due to the concerted law enforcement action (and successive sanctions) against Hydra, cryptocurrency cash-out services are often...
Most PCP has a light brown or grey color due to the presence of impurities. Here, we...
Another market is the Bitbazaar market which is very popular and renowned for its solid reputation and...
Looking ahead, the future of dark web markets is uncertain but far from over. The fall of...
It’s important that you choose reliable options, such as Binance, if you value your security. Zcash’s shielded...