
The Onion Router (Tor) also made the technology available in 2002. On top of that, the provider offers perfect forward secrecy (PFS). A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. Also, use an effective antivirus program to check threats if you decide to download files.
Dark Web Links: The Best onion And Tor Sites In 2025
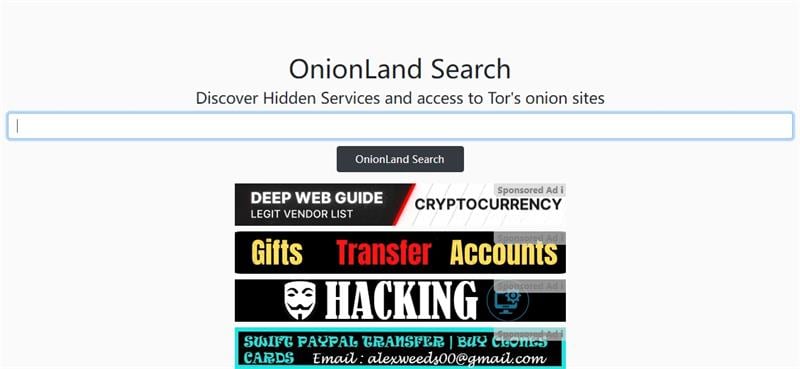
The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software.
Browse Privately
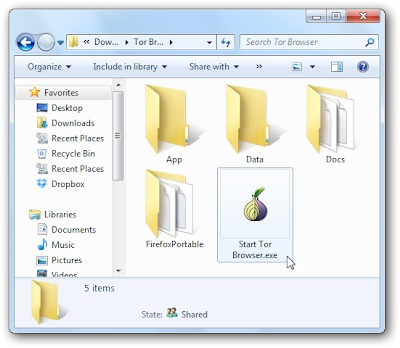
Tor Browser is a web browser designed to enable anonymous communication and browsing on the internet. It’s a great choice to protect your online identity and activities from tracking, digital threats, and online surveillance. Better still, in those cases, is an entire Tor-based operating system called Tails, an acronym for The Amnesiac Incognito Live System. But as an added bonus, it also routes all data over Tor, adding an extra layer of anonymity. The system is secure enough that it’s been listed as a trouble spot for the NSA in documents leaked by Edward Snowden—and Snowden has also said that he uses it himself to avoid surveillance by his former employer. Fifteen years have passed since a couple of MIT grads and a Navy-funded researcher first built The Onion Router, or Tor, a wild experiment in granting anonymity to anyone online.
Tor Layers
It has a bidding feature, with new batches of stolen data being frequently added. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. The second category consists of data stores, which specialize in stolen information.

What Are Dark Web Websites?
Three years later, a not-for-profit research education organization, The Tor Project, was established to manage the network. The enhanced security and anonymity provided by Tor does come at a cost to the end user. Browsing via Tor is significantly slower than navigating the Web with a standard browser. This can make it difficult to view certain kinds of content, particularly streaming audio and video.
How To Stay Safe On The Dark Web
Dozens of news organizations now use it to solicit tips and leaked documents from whistleblowers, including The New York Times, The Washington Post, The Guardian, and of course WIRED. The tool can of course also be used to surf the internet anonymously without criminal intent. The darknet is primarily used to communicate unrecognized on the internet.
By 2011, Silk Road emerged as the leading darknet marketplace for drug sales, though proprietor Dread Pirate Roberts described the enterprise as an online expression of libertarian principles. At its peak, the site listed 15,000 offers from sellers and collected transaction fees of 2.5 to four percent on sales. Buyers paid in bitcoins, held by a Silk Road escrow service until confirmation of delivery. Authorities seized 174,000 bitcoins when the site was shut down in October 2013.
This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too. For example, you can find information unavailable to the public and share data privately while protecting your online identity.
Which Is The Best Laptop For Cyber Security Course?
The value of a bitcoin is subjected to extreme fluctuation and fell from $145 to $109 that month. The deep web is every part of the internet that is not indexed by search engines, like private messages from your social media or your online banking portal. The dark web is a small section of the deep web that is hidden on purpose, requiring specific software to access. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for.
The Tor routing innovations created for US intelligence agents are now used by a variety of everyday users who value their online privacy and data security. The “S” in HTTPS stands for secure, and signifies that a website has an SSL Certificate and encrypts data traveling between your device and a website. As Tor is encrypted by default, most dark web websites don’t use this same certification.

So, do yourself a favor and rescale that Tor window as much as you can before proceeding. In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web. For instance, if you want to buy a laptop or a smartphone, you can try your luck in one of these shops. Sure, you can use other cryptocurrencies if Bitcoin’s not your cup of tea. At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows.
Can I Use A Free VPN To Access The Dark Web?
In Grand Theft Auto Online, players who purchase warehouses and garages for illicit cargo and stolen cars can buy/steal and sell them through trade on the “SecuroServ” syndicate website. Clicking on random onion links is quite risky and isn’t recommended. A random dark web link can lead you to malicious software, phishing sites, and illegal content. Yes, governments can still monitor onion sites if they really want to. Local offices frequently monitor suspicious activities that involve their jurisdictions, so authorities might be closer to your anonymous communication than you know. Since most Tor websites are non-indexed and unregulated, the probability of scams is much greater on the dark web.
- Accessing the Dark Web using the Tor Browser is not just about exploring hidden parts of the internet—it’s about understanding privacy and cybersecurity in the modern world.
- By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet.
- If you want to communicate confidentially with other people via Tor, you should therefore always use encryption.
- All you need to do is click connect and you are officially connected to the Tor network and can now access dark web websites.
- The Darknet is a portion of the internet not indexed by traditional search engines.
- The only difference is that it passes your traffic through random nodes before reaching the destination.
It doesn’t track browsing habits or personal data and won’t expose a user’s identity or location. This makes it safer for those who can’t freely access certain content. A pivotal moment in the history of the dark web came in 2002 with the introduction of Tor (The Onion Router). Naval Research Laboratory, Tor utilized layered encryption to shield sources and destinations of internet traffic. As Tor gained traction, users flocked to it, enabling them to navigate the internet outside the boundaries of traditional scrutiny.
How To Protect Your Identity While Browsing The Dark Web
The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL.
The onion site is especially beneficial for people in regions with heavy censorship or restricted access to media. One of the main advantages of using Tor browser is the high level of privacy provided by the onion network. To understand how Tor can protect a user’s identity as they browse the internet, we need to discuss the internet. At its most basic, it’s a series of connections between computers across great distances. Some PCs house the data stored on the internet, including webpages like Google, which are known as servers.


