With the advent of “I2P Purple Routing,” users can now utilize I2P via their Android devices, and the VPN service InVizible Pro incorporates both Tor and I2P into their service. You personally may not be comfortable using I2P, but there certainly is no shortage of bad actors and those looking for contraband who do. In an exclusive September 2021 interview with Wired magazine, “DeSnake” was praised in almost a messianic fashion after the return of Alphabay in August 2021 (see tinyurl.com/97kfhmk3). However, this time around, Alphabay was exclusive to I2P, and “DeSnake” explained why everyone needed to become accustomed to I2P.
Difference Between AlphaBay Market And Other Darknet Markets
When it comes to accessing the dark web, using a regular browser such as Google Chrome or Mozilla Firefox might not be enough to protect your privacy. Tor Browser is a tool designed to protect users’ privacy by encrypting their online activity and routing it through a network of anonymous servers. While regular browsers may be sufficient for most everyday online activities, they may not be secure enough for accessing the dark web, where anonymity and privacy are of the utmost importance. The dark web is the part of the internet that’s not indexed by public search engines like Google. It’s made up of forums, marketplaces, and websites you can’t find with a Google search and requires specialized software to access, such as the Tor Browser.
How To Use I2P (The Invisible Internet Project)
This is perhaps due to the fact that service nodes routing traffic are paid in cryptocurrency to provide a reliable service. There could be a shift in dark web activity towards Lokinet particularly if there are major outages across Tor and I2P. Forums (message boards and/or imageboards) appear to have relatively low engagement and activity, in comparison to Tor and I2P. Reddit can be a great indicator of topical interest in a subject, especially if related to privacy or the dark web, and there is very limited discussion regarding the content of Lokinet.
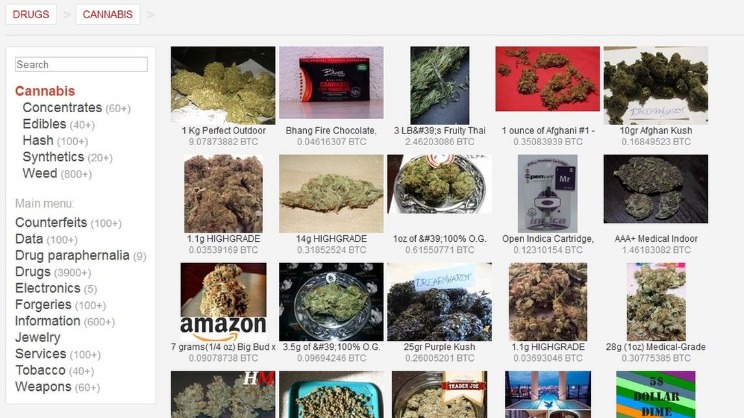
If you access illegal content or participate in criminal transactions, you face legal consequences. The legality depends on your activities and your country’s specific laws regarding darknet use. Dark markets provide a one-stop-shop for cybercriminals, offering a wide range of services such as hacking tools, stolen data, ransomware, and Distributed-Denial-of-Service (DDoS) attacks for hire. This increases the accessibility and sophistication of cyber threats, with far-reaching consequences for businesses.
In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. Darknet Markets 2025 are online cyber criminal platforms exclusively accessible via the Tor network, used to promote advertising, buying and selling illegal goods including a variety amount of cybersecurity-related tools. The Darknet Market can be an unregulated market where people can buy just about anythingalmost anything. This includes firearms, illegal drugs, horrific videos, fake passports, Netflix accounts, credit cards, or even the rental of the hitman. Additionally, the i2p darknet provides a decentralized and censorship-resistant platform for communication and collaboration. Unlike traditional internet services, which are often subject to government censorship and corporate surveillance, the i2p darknet allows users to freely express themselves and exchange information without fear of reprisal.
The Full List Of Trusted Darknet Markets:
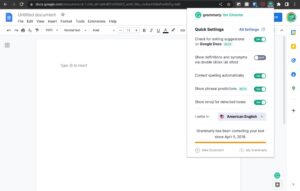
An important way to stay protected against some of the most common risks posed by information on the Darknet is to utilize a monitoring service, and to create unique and complex passwords for every account. Password managers, such as LastPass, make it simple for users to create complex and unique passwords for every site that they use without the need to memorize each password. As concerns about online privacy continue to grow, tools like the i2p darknet offer a glimmer of hope for those seeking to reclaim control over their digital lives. Whether you’re a journalist, activist, or everyday internet user, the i2p darknet provides a safe haven for exploring the web without compromising your personal information. However, using a “high security” browser configuration can help to manage this risk.
Using the Tor Browser, navigate to the FoxyProxy page on Mozilla’s website and install the add-on. After doing so, you will be prompted to restart the browser to complete the installation. There are a few messaging services on I2P, with the two big ones being I2P’s built in email application and I2P Bote. Another reason of vital importance of why AlphaBay is returning is how everything ended with alpha02. Our searches for the truth have led us to believe that he was Epstein’d (or should we say Mcafee’d more recently?) in a way which shocked everyone. He did not deserve that, I knew him and he really was a nice, bright guy who was genuine about the community and people regardless of what he did.
What Are Dark Markets?
While the I2P network is optimized for .i2p sites, you can technically access regular websites, but the experience might be slower compared to traditional browsing. I2P, like Tor, is an excellent tool for anonymous browsing, so install and enjoy the benefits of privacy! It is thereby an entirely separate network, but does provide a much needed alternative that addresses some of the shortcomings of the Tor network. We hope in the future that installation and day to day usage will be as smooth as the Tor network however. According to their major features and design, at least five archetypes of marketplaces can be distinguished. On 7th August 2021 DeSnake re-opened AlphaBay for business after having his identity verified by PGP, forum admins, ex-AlphaBay staff members (those not caught) and multiple security researchers.
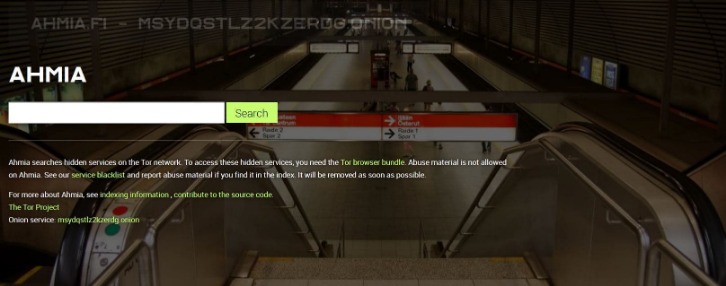
When conducting an investigation, professionals have a vested interest in finding all information and context available. Where we look can be crucial to the success of an investigation, including in online sources. Using I2P data aggregators instead of the network itself can be a viable alternative. It is estimated that there are around 50,000 users active on I2P and this number may be growing. While smaller than Tor, I2P contains mirrors of forums, discussion pages, and markets, some of which focus on, or promise to deliver, illegal goods and services. With I2P, you won’t connect to everything right away – the longer you’re connected, the more tunnels are established to peers, and therefore the more places you can explore.
- Tor is the most popular instance of a darknet,19 and it is often mistakenly thought to be the only online tool that facilitates access to darknets.
- The Tor network service is run by a worldwide community of volunteers and are not controlled by anycorporate or government agencies.
- Eventually, the message arrives at the endpoint where the messages are split out again and forwarded on as requested.
- In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information.
- Eepsites take much longer to load, and because of this, sites on I2P are often “dated-looking,” with not much script or graphics.
Can I Access I2p Sites Using Regular Browsers?
For instance, let’s say you are incredibly unlucky and he has Tor and I2P mitigations against this. Complete the captcha to get your Alphabay Link, this is a Anti-DDoS measure. While i2p provides enhanced privacy, it doesn’t guarantee complete security.
I2P Peer Hardening:
- While there are a few similar efforts worth reviewing, both for technical and functional comparisons, two in particular are pulled out here – Tor and Freenet.
- No Freenet node knows whether the node it is forwarding data to is the final destination or just another node along the way.
- Websites on the Dark Web use “.onion” or “.i2p” top-level domains and are not indexed by standard search engines, providing an environment of increased privacy and anonymity.
- Store your passwords in a secure location that only you have access to; this could be the same place where you keep important documents or a password manager.
- In fact, torrenting just provides more cover-traffic, improving overall anonymity.
- “On March 26, customers and vendors logged into their Dream Market accounts and found themselves unable to use the marketplace’s most basic functions.
This is where I2P sets itself apart from Tor, in that it has absolutely no issue with users torrenting. In fact, torrenting just provides more cover-traffic, improving overall anonymity. This kind of content isn’t indexed because the computers that host the data block automated programs, known as bots, from trawling through the sites, as part of the indexing process. It doesn’t necessarily mean the computers contain anything illegal or are being used for anything nefarious (they are, after all, perfectly visible on the Internet) – it’s simply a matter of improved security and privacy. A multitude of machines seamlessly handle this process for you – connecting you to the appropriate server, transferring the files your browser requests, and so on. Explore a diverse selection of goods and services, with a focus on privacy and security.

Law Enforcement Responds To Tragic Texas Flooding
Our conclusion is that AB is currently very well trusted and can be used without any fear of being scammed. Please keep in mind that this is our own review, we do not endorse use of this market. In conclusion, the i2p darknet is an anonymous network that allows users to communicate and exchange information securely. While it offers several advantages regarding privacy and information freedom, users should always navigate with caution and remain aware of potential risks.
Misc Links
Just like eCommerce stores on the regular web, darknet marketplaces come and go and rise in fall in popularity. Currently, and from my perspective, Empire is the most popular darknet market but is frequently offline for periods, making it hard to access. White House Market is another popular market but requires you to use Monero instead of Bitcoin. To find out which darknet markets are currently popular, see Darknetlive.com or dark.fail. I2P, or Invisible Internet Project, is a project aiming to provide secure and anonymous communication over the Internet. Unlike Tor, which is designed mainly for browsing and accessing hidden services, I2P focuses on peer-to-peer communication and supports a range of applications.
Companies must implement strong data security measures, employ encryption, and monitor for data breaches to protect customer and employee information. Here, anyone can obtain a seller account and put listings for the community. Transactions are made throughour secure Escrow system to ensure safety for our buyers.