Our expert industry analysis and practical solutions help you make better buying decisions and get more from technology. For totally hiding all of your online antics, you’ll want to also use a VPN. Just remember, both the Tor Browser and VPNs will slow things down, so you’ll likely not be happy with streaming through the Tor Browser. Live OS options that can be run on nearly any computer by simply popping a USB stick in and booting from it include Subgraph OS, Freepto, and Tails. Other options are the Freenet and I2P (Invisible Internet Project) peer-to-peer networks, both of which provide censorship-free communications.
What Is The Dark Web And How Do You Access It?
Searching on the Dark Web differs significantly from searching on the traditional Surface Web. While search engines like Google rely on indexing web pages and displaying results based on keywords and relevance, the Dark Web operates on a different infrastructure entirely. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. Then, simply click the operating system that you are using and download the file.
The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN.
Configure Tor For Privacy

For added protection, it’s best to use a VPN like ExpressVPN to encrypt your internet traffic and mask your IP address while establishing the initial Tor connection. Once connected to Tor, you’re ready to begin exploring the dark web. However, keep in mind that the dark web is not organized like the regular internet. Instead of search engines, you’ll need to rely on directories or specific .onion links. Once you’re in, continue to use caution to protect your anonymity and safety. Don’t click on random links from strangers while browsing the dark web, and never give away any personal information.
How Do I Make Duckduckgo My Default Browser
With over 1M indexed pages, it’s reliable and offers a Google-like feel. DuckDuckGo offers a .onion version with privacy-first results from both surface and dark web. Pushing your hardware to its full potential — such as by enabling XMP — ensures that you get the best performance which is crucial for all sorts of heavy tasks including gaming. Memory is one of the key components that can bring a noticeable improvement in video quality and speed. While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution. Using Tor is especially helpful in countries where authoritarian governments censor the internet, preventing citizens from accessing news outside their country.
The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service. Lastly, should you confirm you’re a victim of identity theft, report the matter to your local law enforcement and the Federal Trade Commission. They can guide you through the process of restoring your identity and securing your digital presence. This is a proactive step that alerts you when there are changes to your credit report. It helps to quickly detect any suspicious activities linked to your identity, enabling you to act before significant damage is done.
Happy Chick Software: A Complete Overview Of The All-in-One Retro Gaming Emulator

Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. With this setup, you connect to your VPN first, then open Tor Browser. That means your ISP only sees encrypted VPN traffic and can’t tell you’re using Tor. It also hides your real IP address from Tor’s entry node, which is the first hop in the Tor circuit. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails.
The Hidden Wiki & Co
However, this feature is only available on iOS, Android, and Windows. It is a relatively new provider but offers better features than most established VPNs. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. Also, use an effective antivirus program to check threats if you decide to download files. You can check out this guide on the best antivirus software applications today.
- We’ll also dig into common questions like how to access the dark web and whether or not it’s safe.
- Free Dark Web scanners can tell you if your data is at risk — but 24/7 monitoring is the best way to take action if your information has been leaked.
- Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains.
- While we don’t endorse or encourage illegal activities, it is important to understand how to navigate through the Dark Web and conduct searches effectively.
- For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.
- But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web.
Be prepared for potential risks and irregularities, which could indicate identity theft or data breaches. Detailed steps and further safety measures are available for a thorough understanding of how to search your name on the dark web. To access the dark web safely, it’s necessary to use a dark web browser like Tor in combination with trusted dark web directories and search engines to help you find reliable sites.

Step 4: Start Searching onion Websites
The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. Naval Research Laboratory mathematicians and computer scientists in the mid-1990s. The U.S. Army developed “onion routing” to protect intelligence communications online. The users of the dark web are typically aiming to block governments from snooping on them. This can often be for political reasons, but also because they may be involved in illegal activities, such as the ones listed above.
Dark Web Monitoring And Identity Theft Protection At Your Fingertips
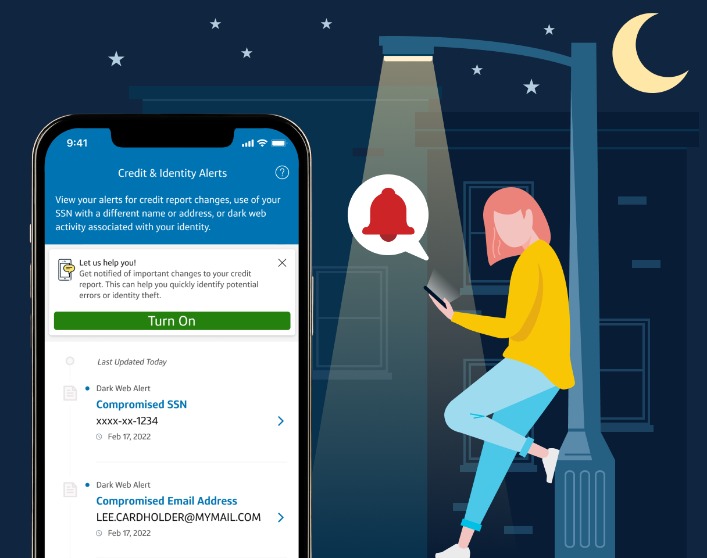
They are designed to decode encrypted pages, making the otherwise inaccessible information available for review. For example, Aura monitors over 130 unique pieces of personal information on the Dark Web and alerts you in near real-time if anything is found. Two-factor authentication (2FA) is an additional layer of cybersecurity that prevents someone from accessing your online accounts even if they have your password or username. As of 2025, Google offers residents of eligible countries with a consumer Google account a “Dark Web Report” feature.
Report It To The Authorities (if It’s Safe To Do So)
It’s advised to run a comprehensive scan on your devices for malware. Removing sensitive personal info from the Dark Web is just about impossible. Therefore, it’s better to minimize your digital footprint as much as possible to make yourself a less vulnerable target.
The Best Dark Web Search Engines For Anonymous Browsing
Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL. In this article, we have explored what the dark web is and how Tor Browser provides the necessary anonymity and encryption to access it. We discussed the importance of setting up Tor Browser correctly, ensuring security and anonymity, and navigating the dark web safely.