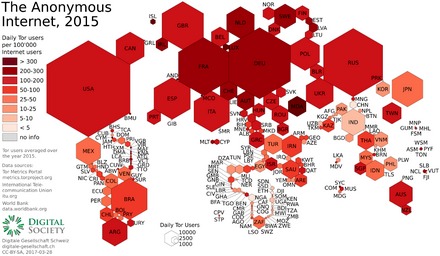
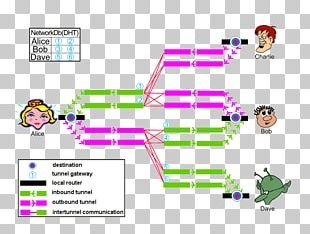
Using I2P means you need to be able to connect to other peers, and other peers need to be able to connect to you – so you want your seed ratio to be higher than your download ratio. You can check the number of peer connections on the I2P router console page – the higher the number of peers, the more services you will be able to visit (and the faster they will load). I2P is not as popular as Tor and this is likely due to the time it takes for ‘tunnels’ to be created in order to use this dark net. While I2P offers anonymous access to the dark web, a VPN focuses on providing security and privacy on the internet.
Once you have configured your browser (we used Firefox), and started I2P, you can access the I2P router console and other I2P services. Firstly, let’s get definitions out of the way, dark web versus dark net. We define dark nets as an encrypted network infrastructure on the internet, and the dark web refers to the sites hosted on the dark net. I2P offers various services, including email, file sharing, and instant messaging. While Tor remains the go-to for general anonymity, I2P’s design is better suited for darknet markets due to its resistance to global adversaries.
Red Dog Security Report
Another feature of this design is the ability to support streaming apps. Shop for exclusive products in our marketplace, where privacy, security, and anonymity are always a top priority. I2P is currently used to create an anonymous website using a standard web server and linking it with the I2P Tunnel Server.
Command Line (headless) Install:
You’re likely not to get any eepsites in the router’s address book due to technical issues that are nothing to worry about. If this happens, you can use a jump service link, as they work as address helpers. You’ll find options for the jump service links at the bottom of the page, and sometimes, you may need to try more than one jump service link.

Stay Updated And Secure
There are a few messaging services on I2P, with the two big ones being I2P’s built in email application and I2P Bote. Another vital precaution is to ensure that your .onion URLs are correct. However, always a niche project within an obscure area of interest (the dark web), the I2P user base is clearly in serious decline. This is demonstrated by the sheer number of dead links found on any I2P search engine or eepsite directory and by the low level of traffic found on once-popular I2P forums.
Files / Sharing
The deep web is a vast and mysterious place, filled with all sorts of hidden content that can’t be found through traditional search engines. One of the most intriguing parts of the deep web is the I2P darknet, a network of websites that can only be accessed through specialized software. In this article, we’ll take a closer look at I2P darknet sites and what makes them so unique. I2P, which stands for Invisible Internet Project, is designed to protect users’ privacy and anonymity online. Unlike traditional internet browsing, i2p encrypts data and routes it through multiple nodes across the network, making tracing exceedingly difficult.
Privacy In America Now Starts With A VPN A Brief Note On Threat Modelling And Lesser Evils
We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. However, like any technology, it can be used for legitimate and illegitimate purposes.
- These guides can be found on the Oxen Docs website – note, the Linux VM install is straightforward if you are using a Trace Labs VM.
- What both these technologies have in common is that they are primarily concerned with accessing the publicly indexed ‘visible’ (or ‘surface’) web.
- Firstly, the I2P welcome page will suggest configuration changes to your browser (Firefox is recommended).
- I2P is defined as a privacy-focused peer-to-peer (P2P) communications system.
- In short, if you can access the dark web resource you’re looking for with I2P, you should use I2P.
- When data is sent over I2P, it is encrypted within layers end-to-end between the source and destination and is transferred via various tunnels.
Can I Use I2P To Browse The Regular Internet?
Explore a diverse selection of goods and services, with a focus on privacy and security. If you’re seeing this message, access is restricted for regular browsers. Judging by other hacker resources, it’s hard to tell whether they’re run by masters of disguise or just random people with no real connection to hacking. For example, Project Mayhem appears to offer some services, but outwardly it looks more like a Mayan calendar. The French hacker forum BumpTeam feels like a freshman’s lab assignment.
While i2p primarily focuses on its own services, there are configurations available to access the standard internet, although with limitations. On 7th August 2021 DeSnake re-opened AlphaBay for business after having his identity verified by PGP, forum admins, ex-AlphaBay staff members (those not caught) and multiple security researchers. This dataset contains user behavior traffic in Tor, I2P, ZeroNet and Freenet. For example, the Armada site advertises DDoS attacks, hacking, and similar services. However, the operators themselves claim it’s all bluff, fiction, and a joke—and we didn’t attempt to verify that. For example, XMPP (Jabber) servers like Echelon and anonymous, decentralized email systems like I2P Bote won’t impress anyone but complete newcomers these days.
The dark web isn’t one single website, and it’s not typically accessible to users via the surface web. Instead, the dark web consists of a network of underground marketplaces, forums, and encrypted chat channels. Websites on the Dark Web use “.onion” or “.i2p” top-level domains and are not indexed by standard search engines, providing an environment of increased privacy and anonymity. The purpose of onion routing was to help people use the internet with the maximum amount of privacy by sending traffic through a number of different servers, encrypting it along the path. It is very easy to dosomething that would deanonymize a user, such as use an older browser or tool that is not configured to proxy alltraffic via Tor network services.
If you’re looking for a way to obscure your network traffic, chances are you’ve heard of Tor and possibly I2P. Although they’re both decentralized peer-to-peer networks, there are significant differences between I2P vs Tor. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor….
Today, we see multiple darknet markets and illicit services hosting their sites on both the TOR network and I2P, and we were likely see this trend continue. The Tor network, also known as The Onion Router, is an open-source software that allows users to browse the internet anonymously. Navigating the Tor network may seem daunting at first, but with a little guidance, you can reap the benefits of enhanced online anonymity. When it comes to accessing the dark web, using a regular browser such as Google Chrome or Mozilla Firefox might not be enough to protect your privacy. Tor Browser is a tool designed to protect users’ privacy by encrypting their online activity and routing it through a network of anonymous servers.
Just be patient and let it warm up because once it connects, you can use the network’s features and browse websites within it. In conclusion, the i2p darknet is an anonymous network that allows users to communicate and exchange information securely. While it offers several advantages regarding privacy and information freedom, users should always navigate with caution and remain aware of potential risks. This network is often referred to as a “darknet” due to its hidden nature. That being said, it does automatic encryption, and allows you to create multiple ’email identities’ (accounts) with one click. I2P-Bote is decentralized and stores messages encrypted on the network, meaning that your trust is in strong mathematics rather than an anonymous person.