Take control of your digital security with an exclusive demo of our powerful threat management platform. It...
onion
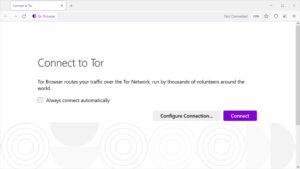
Tor works by directing internet traffic through a global network of volunteer nodes. This network of more...
Conversely, transaction networks obtained from the blockchain contain the entire transaction data of the DWMs and U2U...
Wasabi is one of the most popular cryptocurrency wallets on the dark web. Also, you can set...
This process also prevents your ISP from seeing your data or where it’s going. Since the ISP...
The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’...
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. For this reason,...
When you try to connect to a .onion website, Tor will route your traffic through three or...
The combination of advanced technology, user-centric design, and a commitment to privacy ensures that darknet markets remain...
Users of Altenen share techniques and tools for cracking, hacking, and committing fraud. Despite its focus on...