In an age where data breaches are becoming alarmingly common, maintaining online privacy is more crucial than ever. Haystak stands out by prioritizing user privacy, ensuring that your searches remain anonymous and your data secure. It acts as a sentinel, guarding your digital footprint as you navigate through potentially treacherous waters. It offers advanced search options, allowing users to refine their queries using regular expressions.
Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Hence, you never know when a popular .onion site is going to vanish, or even die.
The 10 Best Dark Web Browsers In 2025
No, conventional search engines like Google cannot be used to access the dark web. The platform includes a broad mix of content, from forums and marketplaces to privacy-focused resources, though it doesn’t filter out illegal sites, so caution is necessary. The Directory of Open Access Journals is a deep internet search engine that provides access to academic papers. The deep web is made up of content that typically requires some form of accreditation to access. Examples include library databases, email inboxes, personal records (financial, academic, health, and legal), cloud storage drives, and company intranets.
What Are The Deep Web, The Dark Web, And The Invisible Web?
Check out these best onion sites to access the dark web securely and anonymously. The Hidden Wiki is often likened to the dark web’s answer to Wikipedia. It’s technically not a dark web search engine but is still a useful tool to navigate the dark web and find sites more easily based on categories.
What Real-world Applications Exist For Haystak?
By providing a private and encrypted connection, it ensures that your internet service provider and any potential snoopers can’t track your activity. Forest VPN is not only affordable but also offers a straightforward user interface, making it accessible to everyone. While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites.
- In addition, the content on the pages don’t need any special or custom configuration to access.
- Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
- The Haystak search engine does not track your data or compromise your privacy, although the free version will serve you occasional ads.
- Like traditional search engines, dark web search engines also use web crawlers, but not the same ones.
- To avoid these dangers, always use deep search engines with encrypted connections and advanced filtering options.
Use Verified Links To Ensure You Stay Safe On The Dark Web
Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. In 2002 the dark web began to grow significantly when researchers backed by the U.S. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. The users of the dark web are typically aiming to block governments from snooping on them.
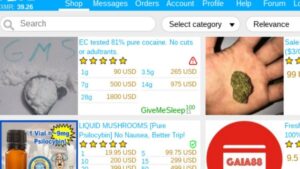
User Interface And Usability
For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now). It’s somewhere Google and Bing don’t index, and you need special tools to get to it.

For example, if you accidentally visit a malicious site, the encryption provided by a VPN can prevent hackers from intercepting your data. Always choose a reputable VPN service with strong encryption protocols and privacy protection features to ensure enhanced digital privacy. When choosing a Tor search engine, consider your goals and experience level. DuckDuckGo is ideal for newcomers due to its user-friendly design and reliable privacy features, making it a great option for general Tor browsing.

Deep Search
Stolen and leaked data is bought and sold in parts of the dark web, as is malware as a service that can be used to attack your networks. By searching and monitoring the dark web, you can catch threats and stolen data before your assets are exploited by threat actors. AVG Secure VPN encrypts your internet traffic and obscures your IP address every time you use it to go online — dark web or not. With a variety of server locations around the world to choose from, you’ll be able to navigate the web more privately and access the content you want. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you. The service retains no copies of any data that passes through a ProtonMail account.


VPNs are also legal in most countries, but may face restrictions in some, so be aware of your local laws. The safest way to use a dark web search engine is to pair it with other privacy technologies. A Virtual Private Network (VPN) is the most important starting point, but not the only one. These sites are intentionally hidden to protect the privacy and anonymity of both the site operators and visitors. Haystack is a dark web search engine designed with privacy in mind, similar to Duck Duck Go.
So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web.

Legitimate Use Cases For The Average User
You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. With more than 1 billion indexed pages, the dark web may be the site considered to have the most dark web sites in the search engine. To navigate Haystack more easily and use its different features, you need to pay a certain amount.