Now, places like ASAP are talking decentralized setups, spreading the load across nodes so they’re harder to shut down. I’ve seen some beta versions popping up on forums, and they’re rough but promising. These findings illustrate that ransomware sold on the darknet is both affordable and user-friendly. One approach to help address this would involve the identification of products that are found to be offered on darknet markets before their official release on the surface web. Knowing that plans were shared would help companies narrow down which processes would have to be reviewed and where measures should be put in place to ensure adequate guardianship. Stay informed about the latest darknet marketplaces, secure browsing practices, and privacy tools.
Agentic AI In Cybersecurity: Transforming Threat Detection And Defense
- Darknets and dark markets have propelled the growth of cybercrime by offering a platform for the sale and exchange of malicious tools and services.
- User reviews and vendor ratings play a critical role in maintaining trust within these markets.
- Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search.
- Google considers the majority of the content on the entire web highly irrelevant and useless to its users.
This ongoing cat-and-mouse game poses a significant technical challenge in combating the activities within darknets. In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. Once the buyer confirms satisfaction, the funds are released to the seller. The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience. Like other marketplaces, ASAP Market also requires you to register for an account.
What Is Cyber Threat Intelligence?
DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Open up Tor, and you won’t suddenly see the dark web staring back at you.

– Silk Road Launch
This multi-layered redirection ensures your actions leave no trace, offering a high level of anonymity. Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny.
Stolen Data Ecosystem
This malware-as-a-service model allows less tech-savvy criminals to launch malware-driven cyberattacks without building the tools themselves. Malicious vendors often infect buyers with spyware, ransomware, or infostealer malware hidden in downloadable files. Some listings are nothing more than scams designed to trick people into sending cryptocurrency without delivering anything in return. While technological innovation remains a force for progress, its use within the criminal underworld signals a need for more coordinated global responses. In 2025, the dark web no longer exists in isolation—it interacts with mainstream platforms, influences real-world crime, and exploits cutting-edge financial systems.
Why We The North Marketplace Stands Out

In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. While this is good advice for any type of web browsing, be particularly careful not to offer up any personal details, such as your credit card info or email address. Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web.
Method II – VPN Over Tor
KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Always use a fake name and a temporary email address when you buy something from dark net shops.

Are IndusInd Bank Derivatives Struggles Exposing Broader Market Risks?
In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web.
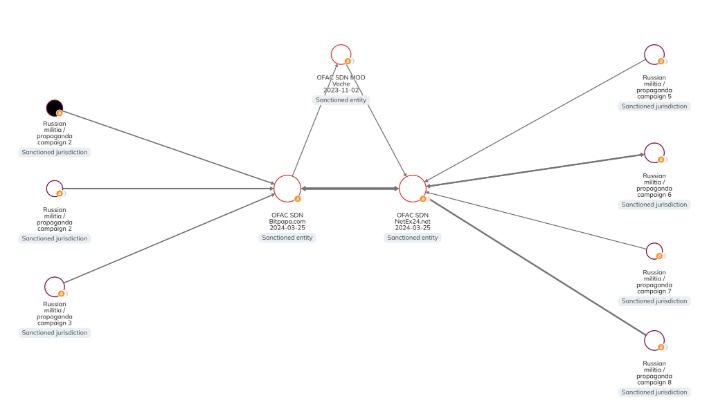
Another key distinction is that access to darknet markets requires the use of special software such as the Onion Router, or TOR, which provides security and anonymity. Alphabay Market leads with 60,000+ listings and $20 million in monthly trades via BTC and XMR, dominating 20% of darknet marketplaces. With 25,000+ users and 3,000+ vendors, it’s the gold standard for escrow security and scale. These darknet markets are difficult to disrupt directly, but efforts to thwart customers of stolen data from using it offers some hope. We believe that advances in artificial intelligence can provide law enforcement agencies, financial institutions, and others with information needed to prevent stolen data from being used to commit fraud. This could stop the flow of stolen data through the supply chain and disrupt the underground economy that profits from your personal data.
The homepage includes options like browsing products, searching, mixer, and coin exchange. Mega Market is a new yet popular shop on the dark web that reached a skyrocketing reputation after the closure of the Hydra market. It allows you to buy and sell a wide range of products and services with a good user experience. This site supports PGP encryption and two-factor authentication features.
More On Tor Onions
In addition to counterfeit merchandise, MGM Grand Market offers access to stolen credit card information, compromised bank accounts, and other financial fraud-related services. The market is also known for its listings related to financial fraud, such as phishing tools and stolen credit card information. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. WeTheNorth is a Canadian market established in 2021 that also serves international users.
What Is Tails Software Used For?

Its intuitive interface and advanced search features make it easy to find local and global products. The marketplace extensively vets vendors listed within its deep web environment that offer a wide range of product portfolios, including security solutions, digital services, and specialized equipment. It stands as a reliable alternative to the defunct Alphabay Market as it continues to position itself as the premier source for advanced privacy-focused digital commerce. The demand for pharmaceuticals on darknet markets remains high, with a focus on prescription medications, nootropics, and performance-enhancing drugs.



