In this blog, we’ll explore the intricacies of dark web monitoring and its implementation strategies. Let’s explore how artificial intelligence (AI) and machine learning (ML) technologies are changing threat detection capabilities in this hidden digital ecosystem. This allows it to uncover leaked credentials, stolen intellectual property, or planned attacks targeting specific organizations. This is then transformed into alerts when exposed data or vulnerabilities are identified. It helps you shine a light within your own perimeter, and spot things that don’t belong.
Easy Integration With Your CTI Toolset
Dark web monitoring tools can alert you if we find that your information is exposed on the dark web, allowing you to take swift action following a data breach to help protect your identity before it’s too late. In a constantly evolving digital landscape, staying informed and prepared is key. Used thoughtfully, dark web monitoring empowers you to detect potential leaks early, respond to threats promptly, and reduce the overall risk to your data. But it should be viewed as one layer of a broader cybersecurity strategy to ensure realistic expectations and encourage a more resilient approach to digital safety. ExpressVPN’s dark web monitoring service is included at no additional cost for eligible U.S. customers on select plans. Dark web monitoring gives you early visibility into leaked data and emerging threats.
Onion Search Engine
IDStrong alerts you immediately if any part of your identity has been compromised. Dashlane saves password and secure information for autofill and even generates secure passwords for users. These selectors allow Intelligence X to gather open-source intelligence from places like the darknet, document sharing data, whois data, public data leaks, and more. Based in the Czech Republic, its mission is to develop and maintain a massive search engine and data archive.
CTM360 CyberBlindspot And ThreatCover
Dark web monitoring helps shine a light into this hidden world, alerting you when your information is at risk and giving you a chance to act before criminals do. While dark web monitoring tools generally work in the same way, each tool uses a different combination of technologies, which impacts its overall accuracy and effectiveness. Complete with a password manager, Dark Web monitoring, Safe Browsing features, and advanced threat monitoring, Identity Guard has the tools you need to keep your whole family safe. IdentityWorks offers a free one-time Dark Web scan, and paid plans include monthly privacy scans — although these only check for potential threats to your phone number, address, and email.
What Is A CISO? The Top IT Security Leader Role Explained
All Norton 360 plans come with a steep introductory discount for first-time users. In addition to tracking data leaks and online marketplaces, Norton 360 monitors your phone and social media for signs of account takeovers. Originally developed as a password manager, LastPass has expanded its product to include Dark Web monitoring. It prompts you to change weak and reused passwords, and provides an overall security score based on the strength of those passwords. When hackers break into company databases, they strip away as much user information as possible and sell it on the Dark Web.

Cyber Incident Response Retainer Services
Here, everything from credit card numbers to private health records can be traded. The vast majority of hacking-related security breaches occur when cyber criminals gain access to employee accounts in enterprise applications by using stolen or weak passwords that are often exposed on the Dark Web. If a victim’s personal information and sensitive data are exploited on the dark web, it can have significant financial and social consequences and take years to recover. One compromised account can cripple the most sophisticated company with high-end security platforms. Automated threat intelligence uses AI to analyze cyber risks, detect threats, and provide actionable insights in real-time.

Why You Should Use Dark Web Monitoring
- People might find themselves victims of identity theft, or companies might face unforeseen problems, like losing their customers’ trust.
- Digital Risk Protection continually monitors and indexes hundreds of millions of dark web pages, pastes, criminal forums, Telegram, IRC, and I2P pages and is programmed to look for specific risks to your organization.
- As a search engine, Intelligence X is unique because it works with “selectors”—specific search terms such as email addresses, domains, URLs, IPs, CIDRs, BTC addresses, IPFS hashes, and more.
- The best Dark Web scans spot protected accounts as soon as their details appear on a Dark Web forum, enabling users and account administrators to change login credentials immediately.
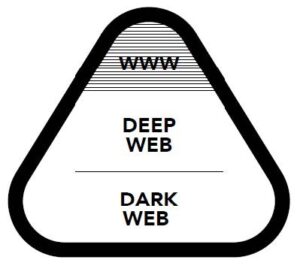
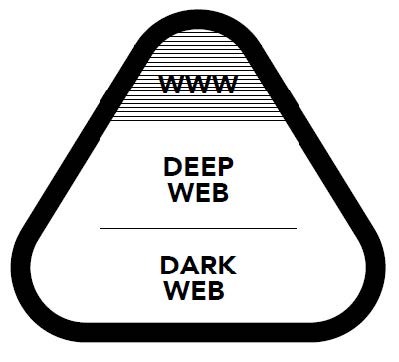
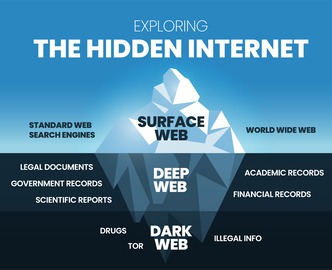
- It consists of websites and resources that are openly available to users without any special access requirements or encryption protocols.
This part of the internet, notorious for its anonymity, is often a hotbed for illegal activities, including the trading of stolen personal data. As cyberthreats become increasingly sophisticated, understanding and implementing dark web monitoring is crucial for safeguarding your personal and financial information. This guide will delve into what dark web monitoring entails, its importance, and how you can use it effectively to protect yourself. Webz aids in preventing cyberattacks by offering Dark Web Data Feeds, bolstering your cybersecurity intelligence capabilities. Webz Dark Web Data API encompasses an extensive range of sources, including millions of deep, dark, and open web sites, forums, marketplaces, paste sites, and more.
- This is what happened when Dread disappeared from the darknet in 2022, much to the shock of its administrators and users, only to reappear a few months later.
- Once they have their hands on personal data, cybercriminals usually attempt to quickly monetize it by anonymously listing it for sale on the dark web.
- An uninterrupted flow of data ensures you can maintain a strong cybersecurity posture without worrying about gaps in monitoring.
- This dark web monitoring tool enables seamless analysis of publicly available data resources available on the darknet.
- For any organization looking for a solution that searches and monitors the dark web across various sources, then DarkOwl is the best option.
Cybersecurity Info You Can’t Live Without
Recorded Future is an AI-powered cyber threat intelligence platform that collects real-time data from various sources, including the dark web, to provide actionable insights. Flare generates real-time alerts if your company or assets are mentioned on the dark, deep, or clear web. DarkOwl is a leading darknet company that provides the largest commercially available database of darknet content worldwide.

AI helps law enforcement agencies track cybercriminals, identify illegal activities, and analyze evidence from dark web marketplaces. These notifications serve as your first line of defense against potential cybercrime resulting from leaked credentials. Data breach monitoring is a security service that continuously scans databases, websites, and the dark web for your personal information.
Password Combo List
Their approach combines recaptured data with automated remediation, resulting in robust security measures. These advanced tools are designed to delve deep into the dark web, unearthing information that traditional web crawlers cannot reach. Dark web monitoring software can makes monitoring easier as individuals do not have to manually search through each dark web source. Therefore, using this tool can enable organizations and security operations teams to act quicker with mitigating potential risks.

Enterprise Security Teams
This blog explores how AI is revolutionizing dark web monitoring, its applications, challenges, and the future of AI-driven cybersecurity. A data breach occurs when cybercriminals successfully infiltrate a database and steal large volumes of sensitive or personal information. In simple terms dark web scanners are services that identify and scour websites that buy, sell, and share stolen data. By establishing connections between dark web sites and other threat sources, Cyble provides actionable intelligence that enables organizations to recognize, assess, and respond to cyber threats swiftly.
They are the guardians of their customers’ data and if they expose those customers to risk, they have failed. Litigation, lost brand reputation, regulatory penalties and auditing costs may be at stake. The risk of future attacks also increases as stolen logins are used in credential stuffing or other attacks.
The dark web is a marketplace for illegal activities, where cybercriminals sell stolen data, malevolent software programs, and hacking tools. The best identity theft protection services include dark web monitoring and alerts about stolen records. With timely notification you can change your passwords, freeze your credit, and/or take other steps to avoid serious consequences of ID theft. Unlike traditional cybersecurity measures, which focus on defending against external threats, dark web monitoring takes a proactive approach by identifying breaches that have already occurred.