This setup is easy to configure, and you don’t need any special settings or features. Just turn on your VPN, wait for the connection to stabilize, and launch Tor. Your internet activity is still subject to exit node risks, so always use HTTPS and avoid entering any personal information on unencrypted sites. Additionally, law enforcement agencies and journalists often monitor the dark web to track illegal activities and gather news stories. The dark web intelligence market experiences a dynamic increase in cybercriminal operations.
It won’t guard you against all of the many threats that exist on the dark web, from phishing scams to malware and malicious sites. It offers some protection, but you still have to be wary and sensible when browsing the dark web. These sites aren’t indexed by search engines like Google, so you can’t find them via traditional means.
- On the software end, the use of Tor and other anonymized browsers is not strictly illegal.
- Tor shares similarities with VPNs and proxy servers — all of these tools allow anonymous browsing.
- Purchases through links on our pages may yield affiliate revenue for us.
- If you choose to pursue exploring any sites on the dark web, you put yourself at risk of being singled out and targeted for hacks and more.
- Finding these can prove a challenge, as searching on the dark web can be irritation – visually and operationally.
Dark Web Tools And Services
The most prevalent dark web content is child pornography, about 80% of its web traffic, despite being challenging to find. Other porn-related content found on the dark web includes revenge porn and sexualized torture, and the killing of animals. The Dark Web has a social media platform called the Dark Web Social Network (DWSN), which is similar to regular social networking sites. Users can create customizable profiles, have friends, and participate in forum discussions. On the dark web, you’re expected to find illegal and prescription drugs (including Marijuana). Also, some toxic chemicals are peddled on the dark web that may cause severe damage to the targets.
Don’t Download Files Or Click Ads
Carding refers to the theft and illegal use of credit card information, and the dark web offers a platform for criminals to sell and buy such information. Traditional social media platforms such as Facebook have also created versions that work with the dark web to provide services across all dimensions of the World Wide Web. However, unlike Facebook, the DWSN requires users to remain anonymous and not reveal personal information to protect their privacy. As stated earlier, neither of these connected content repository networks are illegal to access. Indeed, they must frequently be accessed by cybersecurity organizations conducting threat hunts or defending their networks or those of their clients.
How To Get On The Dark Web Safely?
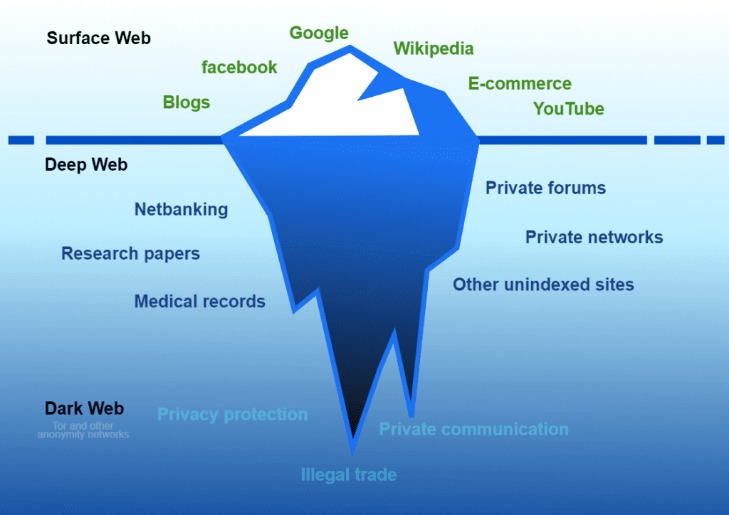
It anonymizes your traffic by routing it through multiple volunteer-run servers around the world (known as onion routing), encrypting it at each step of the way. Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity. Information on the dark web is not meant for public consumption, and the dark web protects personal data intended to be private. You’ll find the more dangerous content and activity at the dark end of the deep web.
Keep Your Data Off The Dark Web
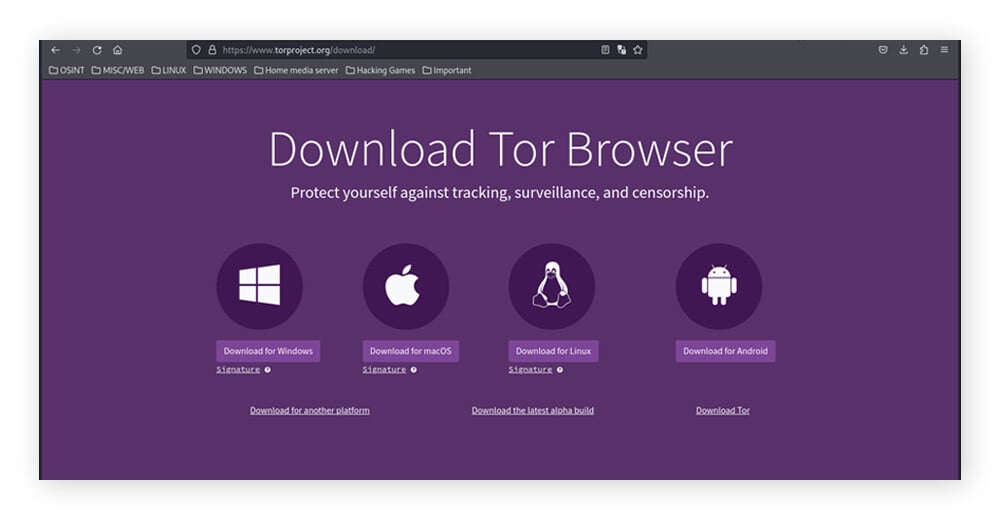
Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. You need special tools to access the dark web, and the Tor Browser is the safest and most popular one. Make sure you download the Browser from the official website (torproject.org). Downloading and installing the Tor Browser should only take you 2–3 minutes. Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network. However, its network is still small, and there aren’t many hidden services available yet.
However, Tor over VPN does not protect your device from dangerous Tor exit nodes. Hackers can introduce malicious code or take advantage of your personal data because the exit node decodes your traffic before it reaches its final destination. The privacy and security it offers ensure anyone who gets access to your device has no means of exploiting it. A hack attack can be a waste as there would be no personal information on your device for data breaches.
Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. It’s a precaution to protect yourself before diving into the dark web.
Many internet service providers (ISPs) and governments are suspicious of Tor use, but a VPN will hide your internet activity and help prevent anyone from knowing that you’re using Tor. The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people). Most dark web websites are in English; according to one estimate, a staggering 78% of information on the dark web is in English.
Plan Ahead Before Connecting
The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search. Using the Tor browser is simple, but knowing when to fire it up is more complicated. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual. The dark web is infamous as a dangerous place, where drugs are bought and hitmen hired, but it can be a safe way to browse the internet if your privacy is serious concern.
Don’t Use Your Main Device
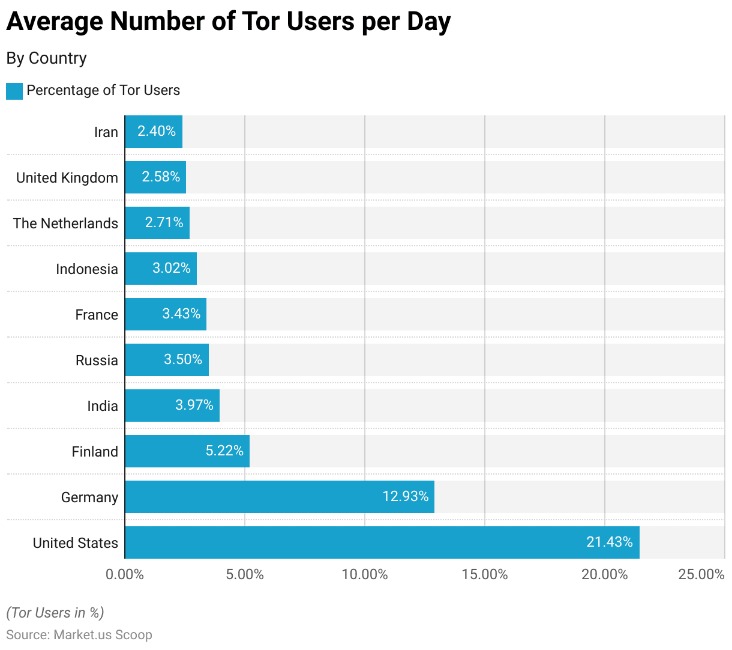
Visitors to the dark web should exercise extreme caution when downloading files, as they may infect your devices with viruses, malware, trojans, ransomware, or other malicious files. At a minimum, users should ensure that their cybersecurity defenses are activated and up to date. It’s challenging to quantify exactly how many people use the dark web, as it operates on anonymity. The Tor network, which provides access to both the deep and dark web, has millions of daily users globally, but not all are using it to access dark websites. In 2023, however, it was estimated that the dark web had more than 2.5 million daily visitors.
Can A VPN And Tor Make The Dark Web Completely Private And Secure?
Your Internet service provider, or ISP, is your gateway to the Internet. As much as the Darknet contains even the “good” stuff, it’s not a place you need to stumble about blindly without proper dark web safety. Cybercriminal groups like DDOS have carried out over 140 cyberattacks on companies since Bitcoin’s emergence in 2014. The attacks have led to the formation of other cybercriminal groups and Cyber Extortion. According to recent research, Bitcoin tumblers are increasingly used for money laundering. The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group.
Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website. On top of that, the installation process of Freenet is rather easy.
While the dark web is often portrayed as a haven for illegal activity, this is only part of the story. There are legitimate uses for the dark web as well, particularly for those seeking privacy in countries ruled by oppressive regimes or for individuals who want to maintain anonymity online. It’s also worth noting that the dark web is not synonymous with the deep web — another layer of the internet we’ll explain later. The deep web refers to the parts of the internet that you can’t reach through search engines like Google Search. While this includes the dark web, the deep web also includes pages that you can only find if you register or sign in, like most content provided by Gmail and Facebook. As long as you are vigilant about your online activity, there aren’t any issues.