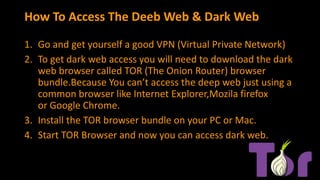
The download process is essentially the same if you use Linux, though you can also download and install your VPN using terminal commands. It’s entirely possible to access the dark web without using a VPN. For that, vpnAlert provides you with objective VPN reviews, as well as comprehensive guides and tutorials.
While the Tor Browser and the Onion Network are an excellent way to protect your online privacy and anonymity, it is by no means a perfect solution, and it has a few weaknesses. Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node destination. When the final layer of the “onion” is reached and decrypted, the message arrives at its destination.
Such people can be opposition figures from dictatorship-led countries, politically oppressed individuals, whistleblowers, or journalists. Due to its hidden nature, the dark web is also famous for the names underground internet and black web. However, don’t fret yourself about this frightening concept, than the actual meaning of the dark web. It’s also good practice to clear browsing history and any related data.
By default, Tor uses the Standard security level, but you can upgrade it to Safer or Safest. To connect manually for the first time, click on the Connect button on the homepage and wait for Tor to establish a connection. To enable it, check the Always connect automatically button on the homepage. Initially created to protect U.S. intelligence communications, Tor was released for public use in 2003. In 2004, the Naval Research Laboratory then released the code and made it open-source. Since then, volunteers and sponsors around the globe have maintained Tor and the Tor Browser.
Words Of Caution When Using Dark Web Sites
Copy your desired onion URL and paste it into the address bar at the top of the screen to begin searching on the dark web. Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website. When the Tor Browser is launched, you will be brought to a purple homepage with a search field for the DuckDuckGo search engine in the center of the screen.
Hacking Services And Groups
Sometimes, you can access a website but won’t be able to login on your Tor browser. Likewise, some websites allow Tor, but with frequent Captchas that can be annoying. The performance of entry, middle, and exit nodes can vary, and some are slower than others. Several seconds of delay, compared to using a standard browser, isn’t out of the ordinary on Tor.
Pegasus Spyware – The Greatest Threat To Smartphone Security
- This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to.
- As the thesis project of Ian Clarke, a student at the University of Edinburgh in Scotland, the Freenet was built to help people anonymously communicate, exchange files, and interact online.
- And once you’re inside, one wrong click on a fake .onion site can expose your identity or infect your device with malware.
- You can also use the Ahmia.fi website to get onion URLs from a normal browser and use those URLs to access websites on the Tor browser.
Tor encrypts your traffic and routes it through the secured Tor network, but it doesn’t protect your data when it passes between the exit node and the server. That is why you should always use the HTTPS version of websites that provide end-to-end encryption for your data. The Dark Web or Dark Net is essentially a collection of websites that are not indexed or not able to be indexed by regular search engines, like Google or Bing. That means you cannot find the Dark Web websites by googling them.
What Is The Hidden Wiki?
In this setup, the VPN connection acts as a middle layer between your device and Tor, routing your internet traffic through the VPN before it reaches the Tor network. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays. Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content.
Let’s summarize the most important points from this guide on how to access the dark web. We understand that because of the reputation looming over the dark web as being so dangerous, mysterious, and whatnot. Some sites are safe to use, especially those where you don’t need to provide sensitive information to use. Tor supports a few systems only – Windows, macOS, Linux, and Android. IOS is the only exception, leaving iPhone and iPad users without the option to go to this part of the internet.
Use Strong Anti-malware Software
This means that the identities and locations of darknet users are hidden from public view and remain anonymous, even when interacting with other users or engaging in any online activity. As such, you should exercise caution when accessing any unofficial dark websites. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing. A VPN, in combination with Tor, further enhances the user’s security and anonymity. Tor is a network of volunteer relays through which the user’s internet connection is routed.
VPN Chrome Extension: Enhance Your Online Security Today
- Every communication is encrypted, so even the simplest transaction requires a PGP key.
- In opennet mode, the network will automatically assign you to other users on Freenet’s network.
- Check out our article on the dark side of the dark web for more information about the dangers of the darknet.
- Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims.
- Tor protects your identity inside its network, but it doesn’t hide everything.
In any case, it can be used for any dark web activity thanks to various privacy features. Proton VPN is part of the Proton family of services provided by Proton Technologies AG. While ProtonMail has a solid commitment to privacy, its location has caused problems for users in the past. In 2021, it was forced by the Swiss courts to begin logging the IP addresses and browser fingerprint information of one of its customers. Let’s take a closer look at the best VPNs you can use to safely access the dark web.
Why Do The Darknet And Deep Web Exist? Legitimate Uses
Some services will try to entice you with unrealistic deals and prices. The dark web is home to plenty of unlawful activity, so you must ensure you never get involved in something illegal. More seriously, free VPNs – particularly those offered as standalone services – sometimes make money by selling your data to third parties. Others have dangerous permission requirements and invasive logs.
The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. Those who access the dark web do so via the Tor (The Onion Router) browser. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. In 2002 the dark web began to grow significantly when researchers backed by the U.S.
While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network. Tor still works the same way, though enterprising individuals have taken advantage of the anonymity to buy and sell all manner of vices. Still, people have reasons to stay anonymous without engaging in crime. Tor is useful in countries where internet access is monitored or restricted. By using Tor over VPN, the VPN encrypts your data and hides your IP address.

Originally used by the United States Department of Defense for anonymous communication, the dark web is now a place for those wishing to stay anonymous themselves. To say the least, DOT Security does not recommend going to the dark web unless absolutely necessary. However, if you’re going to venture into the dark web, you’ll need to be well–prepared, so keep reading to keep safe. Practice safe, smart digital habits if you must use Tor to log into personal accounts.



