This is because Tor traffic is usually unencrypted when it passes through the exit node. The Tor network’s principal benefit is that it routes your traffic through numerous servers, wrapping it in several layers of encryption. This makes it difficult for interlopers to monitor the traffic or trace any legal or criminal activity back to you. The hidden web (also known as the deep web or deep net) is the largest part of the internet. It comprises websites that aren’t easily accessible mainly because they are non-indexed, password-protected or paywalled. The dark web is a small subset of the deep web comprising purely non-indexed websites and services.
Malware And Viruses
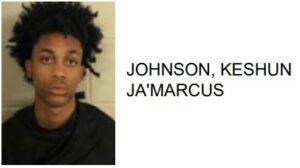
There are reports of illegal services on the dark web, ranging from paid assassinations to the trafficking of sex and weapons. However, some of these alleged services, such as professional ‘hitmen,’ may be scams designed to defraud willing customers. Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity.
How Do I Find onion Websites Safely?
If you get a malware attack, it will remain on the virtual machine and won’t harm your whole device. Use encrypted communication platforms instead of the standard ones with less robust security features. For example, you can use Signal as your daily messaging app– it has end-to-end encryption and collects minimal data unlike many other messaging apps.
- (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top.
- A VPN encrypts your internet traffic before entering the Tor network, making tracking your online activities tougher.
- Trust your instincts and always verify the legitimacy of a seller or marketplace before proceeding with any transactions.
- Tor2web is a web proxy service that allows users to access .onion websites directly from a regular web browser without the need for the Tor browser.
- And because there’s very little use of HTTPS on the dark net, verifying whether or not a website is genuine using an SSL certificate is not feasible.
Once you have those, there are several ways to tunnel through the dark web. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences. The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily. When you search for something on Google or Bing, you’re using the clear web.
One such marketplace that gained popularity is “Empire Market.” It offers a wide range of products, including drugs, digital goods, counterfeit items, and more. Empire Market is known for its user-friendly interface, reliable vendors, and escrow system that ensures secure transactions. However, due to the nature of the Dark Web, marketplaces may come and go, facing periodic shutdowns and rebranding efforts, requiring users to stay updated on the current landscape. Welcome to the dark side of the internet— the intriguing and mysterious realm known as the Dark Web. This hidden layer of the internet has become infamous for its illicit activities, but it’s important to distinguish fact from fiction.
Dark Web Tools And Services
Trustworthy vendors often use escrow services for secure transactions. Escrow services act as a trusted third party that holds the funds until the buyer confirms the satisfactory receipt of the goods or services. This assures both parties that the transaction will be fair and protects against fraud. If a vendor refuses to use escrow services or insists on alternative payment methods, exercise caution and consider finding a more reliable alternative.

How Do I Verify An Onion Link Is Safe?
In addition, due to the notorious nature of the dark web, ISPs tend to track, monitor, and throttle the traffic of anyone who tries to access it. Amidst this, a VPN is exceedingly helpful since it helps bypass ISP throttling and prevents online snooping. A traffic correlation attack takes serious resources, but it’s doable for advanced actors with sufficient motivation. The performance of entry, middle, and exit nodes can vary, and some are slower than others. Several seconds of delay, compared to using a standard browser, isn’t out of the ordinary on Tor.
Regularly Update Your Software
Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web. Estimates place the size of the deep web at between 96% and 99% of the internet. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details.
How To Access The Dark Web On Your Device

Unlike traditional websites, .onion addresses aren’t indexed by mainstream search engines, requiring specialized methods to find them safely and reliably. The most common tool for accessing the Dark Web is Tor (The Onion Router). Tor provides anonymity through a process known as “onion routing,” where internet traffic is encrypted and passed through multiple network nodes. Each node decrypts just enough data to know the next destination but not the origin, making tracing the connection back to the user exceptionally difficult. Tor greatly enhances anonymity, but if an attacker controls both the entry and exit nodes, they could attempt traffic correlation to link your identity to your activity. You can also be tracked by logging into personal accounts, downloading unsafe files, or modifying browser settings that expose your digital fingerprint.

Statistically, it’s impossible not to end up with at least some of those nodes being run by volunteers who take advantage of the system to steal personal information. Many have .onion sites as well, which they’ll mention and provide the correct Onion link to. The best way to find dark web websites is to use an aggregator site. Reporting any illegal content you come across is a small but important way for you to help combat the negative stereotype that privacy is only for criminals. Wait until after you finish browsing the dark web and shut everything down again before opening any research papers you downloaded.
Connecting To A VPN Server
- Secure communication for journalists, accessing privacy-focused forums, and whistleblower submissions.
- During this process, your ISP can still see that you’re using Tor because the entry node is now fully visible.
- Its strongest appeal is that it has strong privacy defaults, making it usable for daily use that can be expanded upon.
- It is worth noting that while the Dark Web offers anonymity, it also harbors illegal activities and potentially harmful content.
- Data theft, cloud breaches, and malware-free attacks are on the rise.
Disabling JavaScript and avoiding personal logins or revealing identifying details can further reduce the risk of being tracked. However, remember that nothing is foolproof, so always exercise caution when exploring the dark web. To find what you’re looking for, you may need to try multiple search engines or visit directories of trusted .onion links.
When using this method, Tor will encrypt your request, which will pass through your ISP unhindered. From there, it will go through a VPN server that conceals your IP and wipes geo-locations tags and other elements your Government or ISP might use to track the request. Choosing Tor over standard browsers is crucial for dark web navigation due to its unique privacy features.
Minimize Or Rescale Your Tor Browsing Window
Most dark web sites are unregulated, which means that there are fewer mechanisms in place to prevent you from accidentally downloading malware. It’s a good idea to connect to a trusted VPN before you even open the Tor Browser to access the dark web. You can download the VPN app from the provider’s official website or your device’s app store. Run the setup file and then simply follow the on-screen instructions.