Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor. The VPN’s encryption will hide from your ISP the fact that you’re using Tor. Then there’s the less popular VPN over Tor, which is advised against by the official Tor Project. Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds. Internet traffic first passes through the Tor Network, and then through the VPN.
Remain Careful Of Your Browsing Habits
Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki.
Either way, some sites take up to a minute or more to load, so don’t fret. If you’re prompted to connect, click the purple “Connect” button and wait for a few seconds. On top of that, Tor’s nodes can also malfunction because they’re owned by volunteers, which will expose your traffic and sensitive information. This is where a VPN comes in, and a reliable VPN like NordVPN (read our NordVPN review here) can do wonders for you. We already know of one necessary component needed for this – Tor. However, while Tor is great, safe, and whatever you think, it’s not as great as another component – a VPN.
If you’re lucky enough, you can find it on clearnet privacy forums. You can also use it within the dark web, as it has .onion links. It will offer you an additional layer of encryption to access the deep parts of the internet. You can choose the best darknet (.onion) website that suits you and start surfing.
Dark Web Search: The Best Dark Web Search Engines In 2025
While some reports of dark web murder-to-order are overblown, it is possible to commission acts of cybercrime on the dark web. These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. Anyone can access the dark web, and it’s not that complicated to do so.
Protecting Against Malware And Untrusted Files

This is a superb resource where people can anonymously and privately ask questions. Think of it as a dark web version of Reddit and you are on the right track! It is a good place to get help and ask questions about the dark web when you are a total noob. The dark web accounts for around 6% of the internet, and it is the secretive portion of the web where drug dealers, black hat hackers, hitmen, and human traffickers sell their wares or services. The deep web is generally a safe place, particularly when compared directly to the Dark Web. However, it is a huge target for cybercrime because it is the area of the internet where private data resides.
You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions. If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity. Remember only to make purchases using digital currencies and never provide any online banking login details. The dark web, an even more puzzling sublayer, exists within this hidden world. It’s designed as an environment to elude detection, where site owners and visitors hide their identities. And while the dark web isn’t synonymous with illicit activities, it’s undeniably the breeding ground for the internet’s black markets, hacker forums, malware vendors, and other illegal activity.
Step 4: Adjust Security Settings
From encrypted communication channels and hacking forums to illicit marketplaces, the dark web is a destination for millions of daily users. Read on to learn more about the five main types of darknet websites and what they contain. The first step is to download and configure the Tor browser from its official website.

How To Access The Dark Web On Android
There are numerous directories that host .onion links and websites, but you should always exercise caution. There are numerous phishing sites, too, as explained earlier, designed to fool users into giving up their personal data. Many cybersecurity and tech experts recommend using a VPN whenever you want to access the dark web via the Tor Browser or any other specialist browser. A quality VPN like ExpressVPN will encrypt your internet traffic and mask your IP address, providing an extra layer of anonymity when establishing the initial Tor connection. As such, it’s important to be extremely careful when accessing the dark web, as you could inadvertently access a site containing, displaying, or linking to illicit content in some form.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
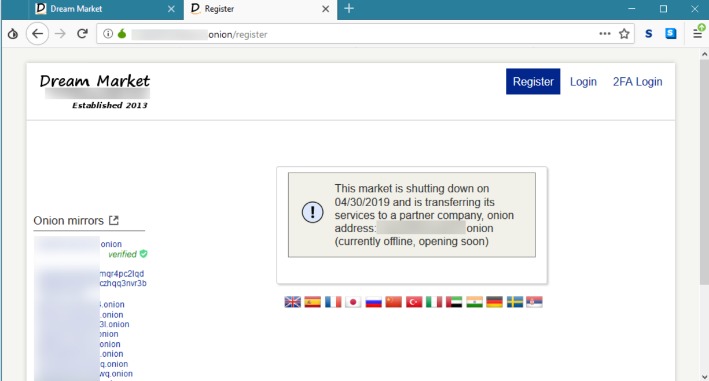
However, some surface web platforms like ProtonMail offer encrypted email services in addition to dark web versions that enable people residing in more repressive areas to communicate freely. There are currently several online darknet markets, but they tend to be incredibly volatile due to government intervention. If you do need to access a dark web website for legitimate reasons, you can check directories like The Hidden Wiki to help find options. By using Tor and a reputable VPN, along with being careful and having the right tools, you can browse the dark web legally and safely.

In other words, these markets ensure anonymous delivery and pickup. The other coins aren’t always accepted, and even when they are, they aren’t the most privacy-friendly. These are markets where any individual is allowed to list and sell products.
The former protects traffic using AES-256-GCM encryption and 4096-bit RSA certificates with SHA512 for server authentication. The latter uses ChaCha20 for symmetric encryption, which is authenticated with Poly1305. Nevertheless, Proton VPN says that the situation is different for VPNs. “Within the current Swiss legal framework,” it says, “Proton VPN does not have forced logging obligations.” It goes on to recommend the use of a VPN or Tor connection when using its email client. In any case, it can be used for any dark web activity thanks to various privacy features. Internet traffic is protected using 256-bit AES encryption, together with a SHA384 hash and 4096-bit RSA keys for OpenVPN and IKEv2.
- It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.
- You risk being targeted for attacks if you explore the dark web without protection.
- Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser.
- We also prefer this method because of VPN’s all-encompassing security.
- Tor routes your traffic through a chain of relays to obscure your IP address.
- People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web.
In-Depth Tutorial On Surfing The Dark Web Safely From Any Device
While in theory you can buy legitimate products and services on the dark web, remember that anonymity works both ways. If you pay for something and it never arrives, you may well not be able to track down the seller to get your money back. There are also millions of servers which only store data which can’t be accessed via a public web page. Data brokers such as LocalBlox for instance crawl the web and store information about business and consumers to sell for marketing purposes.
Instead, the Tor Project has a separate overlay network for iOS users. Although there’s a Google Play Store entry for the Tor Browser’s Android app, you’re always safer going the slightly longer way around. But just in case you prefer Freenet, I’ll show you how to set up both overlay networks in the following sections.