This app connects to the Tor network, allowing you to visit .onion sites. Accessing the dark web on a mobile device requires the Tor Browser, which lets you visit .onion sites only accessible through its network. But there are a few things you need to know — especially on iOS, where the Tor Browser isn’t available.
BUSINESS BROADBAND GUIDES
Its foundation is the Onion Router (Tor) project, developed in the 1990s with funding from the U.S. Naval Research Laboratory to protect sensitive government communications. Later released as open-source, Tor became accessible to the public, enabling anonymous browsing for activists, journalists, and everyday users—while also giving rise to today’s dark web.
What Is The Dark Web? How To Access It And What You’ll Find
The developer, Versatile Apps, indicated that the app’s privacy practices may include handling of data as described below. With VPN, you can enjoy increased privacy and security whenever you go online. Using a VPN (Virtual Private Network) can add an extra layer of security. This helps protect your identity and data while using the dark web. I like testing new software for work, but I’m less “plugged in” to the internet than I used to be.
Dark Web Tools & Services

It’s designed for secure, decentralized storage and is often used for file sharing and accessing information anonymously. You can enter .onion URLs directly into the Tor Browser’s address bar or visit directories like The Hidden Wiki to find popular sites on the dark web. Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network. However, its network is still small, and there aren’t many hidden services available yet. Tor is the most popular way to access the dark web, but it’s not the only option.
Can I Go On The Dark Web On My IPhone?
The certified Tor Project advises against this method, making it less common. BolehVPN and AirVPN are the only VPN providers known to provide this service. In this scenario, internet traffic is routed via the Tor Network and VPN. Freenet is easy to set up because you simply need to download, install, and run it. When you launch your usual browser, Freenet runs via its web-based interface.
Tor supports a few systems only – Windows, macOS, Linux, and Android. IOS is the only exception, leaving iPhone and iPad users without the option to go to this part of the internet. This, joined by incredible value and the price of around $2/mo, makes PIA very attractive. Unfortunately, it’s slower than NordVPN and ExpressVPN but overall, its performance is admirable in practice.
When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network.
While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network. The dark web is only accessible through unique dark web browsers like Tor. Tor is a special browser and the most popular choice because of its security features. These anonymous browsers provide safe and secure access to users on the dark web. A browser like Tor offers various features, including data security through layers of encryption, hiding your IP address, preventing online tracking, and much more.
Internet traffic first passes through the Tor Network, and then through the VPN. This means the VPN provider doesn’t see your real IP address and the VPN protects you from those bad exit nodes. Even when using security measures and your common sense, accessing deep web content still poses a risk.
Why Do The Darknet And Deep Web Exist? Legitimate Uses

These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Services like Random Chat connects you with random people using the same service. All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running.
Examples Of Legal And Useful Dark Web Content
Later in our guide, we’ll see why this isn’t ideal for browsing the dark web safely. In today’s climate, where data breaches and invasive surveillance have become commonplace, understanding how to access the Dark Web and its underlying technologies is becoming increasingly relevant. Whether you’re exploring it out of curiosity or for legitimate personal reasons, it’s essential to approach this hidden realm with the right knowledge, tools, and security measures.
Connections made while a VPN is active will also be encrypted, helping you stay protected from eavesdropping and man-in-the-middle attacks. You can usually select the location you want to appear to originate from and VPNs will use a collection of servers and relays to make tracing your IP difficult. To access a dark web address, you must use a VPN and a suitable browser (it should be Tor).
Tor for Android is developed by the Tor Project itself, while the Onion Browser is the recommended option for iOS users. These browsers offer the best security and privacy for browsing the dark web on mobile devices. You’ll actually have to find the dark websites that you want to search on your own. When you envision the dark web, it may conjure up images of hackers trading stolen Social Security numbers or drug dealers advertising their products online—and that’s not completely wrong. While the dark web can be a helpful tool for sourcing legitimate products or ensuring private communication, it’s also a hotspot for illegal internet activity. If your personal information has been leaked on the dark web, your risk of identity theft and financial fraud significantly increases.
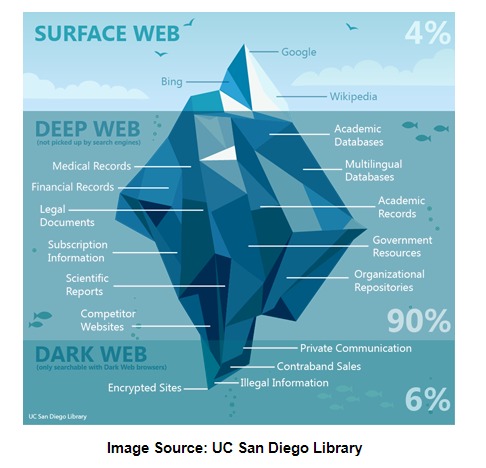
It comprises websites that aren’t easily accessible mainly because they are non-indexed, password-protected or paywalled. The dark web is a small subset of the deep web comprising purely non-indexed websites and services. A VPN (Virtual Private Network) encrypts your internet traffic and hides your IP address before you access the Tor network.
Using Tor Browser: The Final Step To Get On The Dark Web
- Deep web content includes anything behind a paywall or requires sign-in credentials.
- You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”.
- Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation.
- Though most volunteers mean well, others are malicious actors and surveillance agencies.
- A lot of the user data that gets stolen or leaked from big platforms ends up on the dark web, where users buy, sell, and exchange it among themselves.
- I2P is an anonymous overlay network designed primarily for peer-to-peer applications.
Unlike the Dark Web, which requires a special web browser called Tor, you can use any browser to get to the Deep Web. Because of this reason, it is quite easy to encounter fraudulent or malicious websites and you need to take a cautious approach to manually avoid them. That is why you should always check the URLs you visit carefully and avoid entering any personal information on a website unless you’re sure it is trustworthy. Remember, the dark web can be a treacherous place, and caution should always be exercised.

Can You Be Tracked While Using Tor?
Sites on the dark web don’t come with easy-to-remember URLs, and many disappear suddenly. A dark web search engine can help you surf sites on the Tor browser. The Tor browser differs from others such as Chrome or Firefox because it does not take the most direct route from your device to the web. Instead, Tor uses a random set of encrypted servers known as nodes to keep users and sites anonymous. If you decide to venture into the dark web, be sure to educate yourself on the potential risks and dangers.