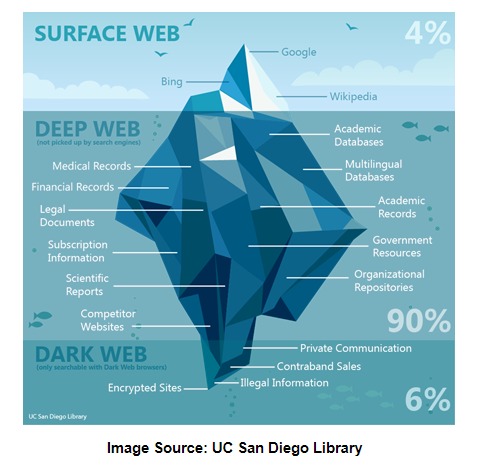
While there are risks, being cautious and following safety guidelines can mitigate them significantly. Although we use the Surface web for quite a long part of our days and feel like it is infinite, it actually is just a fraction of the whole package. The remaining part is hidden or invisible, but it is not impossible to access it.
Start Your Protection,
Hacking and cybercrime forums on the dark web are spaces for newbie hackers to ask questions, veteran cybercriminals to share their expertise, and buyers to find sellers. Cybercrime services are more commonly sold through marketplaces, but you can usually find someone offering hacked servers, computer logins, and stolen data on such forums. There are several ways to protect your online activities from being tracked.
Fake sites are everywhere, and even a one-character difference in the URL can land you on a phishing page. Underneath it are deeper layers that aren’t visible through normal browsing. As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web.
Preparing To Access The Dark Web
If your connection uses a proxy you can configure it by clicking on ‘Settings …’ against ‘Configure how Tor Browser connects to the Internet’.In most cases, this is not necessary. Many who access the dark web do so by first connecting to it with the Tor (an acronym for the “The Onion Router”) browser. Navy and made public in 2004, Tor is the most popular dark web browser because of its unrivaled security and privacy. Turn on your VPN and launch the Tor browser and it will automatically connect to the Tor network from which you can access the Dark Web anonymously. On the Dark Web, you will not find search results indexed by Google, which can make it difficult to find what you are searching for. The Tor browser is completely free to use and is available for most major platforms, including Windows, Linux, macOS, and Android.
Final Thoughts On Staying Safe On The Dark Web
It masks the user’s IP address, making it difficult for websites, internet service providers, and other entities to track their online behavior. It is crucial to approach the dark web with caution and understand the risks involved. Engaging in illegal activities can lead to severe consequences, and exposing personal information or engaging with malicious individuals can compromise your privacy and security. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. Another challenge of finding dark web sites is that they don’t often last long.
Use Strong Anti-malware Software
Dark web sites use encryption software so their visitors and owners can remain anonymous—it’s why the dark web is home to so much illegal activity. Over 2.7 million active users browse the dark web every day, and many do so for legitimate reasons. Here’s a guide that will help you learn about the dark web, the sites that populate it, and how you can visit it safely using the added protection of a VPN and antivirus software. Dark web sites are hidden by non-indexing, making them completely anonymous. You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content. Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions.
How To Access onion Sites With The Tor Browser
Take a look at the sites that these directories have collected and see what topics interest you. If you want to improve your security further, you could also use a VPN at the same time as Tor. For the most security-conscious, you can even install the Tails operating system on a flash drive and run Tor from that. The Dark Web remains a shrouded corner of the internet—an enigmatic space where privacy, free speech, criminality, and censorship resistance intersect. Navigating the Dark Web can be a complex endeavor, but you don’t have to do it alone. Reputable organizations, security researchers, and privacy advocates provide a wealth of insights, tutorials, and software to help you explore safely and responsibly.
- This (practically) irreversible process highlights the importance of taking preventive measures by utilizing a service that monitors your data for potential breaches.
- If the traffic passes through a Tor exit node run by a law enforcement agency, they will only see the IP address that the VPN assigned, not your real IP.
- Links posted to the clear web, in particular, are often malicious.
- It derives its name from the encryption system, which is structured like the layers of an onion.
- It’s a precaution to protect yourself before diving into the dark web.
Getting Onto The Dark Web Using Mobile Devices
For an added layer of protection, consider purchasing a virtual private network, or VPN. A VPN provides you with anonymity by creating a private network from a public internet connection. The Tor network’s principal benefit is that it routes your traffic through numerous servers, wrapping it in several layers of encryption. This makes it difficult for interlopers to monitor the traffic or trace any legal or criminal activity back to you. The hidden web (also known as the deep web or deep net) is the largest part of the internet. It comprises websites that aren’t easily accessible mainly because they are non-indexed, password-protected or paywalled.
That is why you need to follow certain security precautions to keep yourself protected. Make sure all unnecessary programs are closed before running the Tor browser. Besides this, ensure that services like remote desktop or file-sharing that are easy to exploit are disabled and check that your webcam is covered. To be on the safe side, we recommend combining the Tor or onion browser with a secure VPN, such as NordVPN.

Step 4: Navigating The Dark Web
A VPN hides your internet activity from your Internet Service Provider (ISP). Since using Tor can itself draw suspicion, a VPN masks the fact that you’re using it. It also adds a crucial layer of encryption before your traffic even enters the Tor network. Talking about the fundamentals, the dark web and the darknet guarantee privacy and anonymity. Information on the dark web is not meant for public consumption, and the dark web protects personal data intended to be private.
Step 3: Use Best Practices For Privacy
However, keep in mind that the dark web is not organized like the regular internet. Instead of search engines, you’ll need to rely on directories or specific .onion links. Tor protects your identity inside its network, but it doesn’t hide everything.
This guide dives deep into Tor, explaining how it works, its pros and cons, and how to utilize it to protect your online privacy. This allows you to access Facebook through Tor, and your connection doesn’t ever leave Tor where it can be snooped on. This may be useful in countries that block Facebook, for example. Avoid phishing links, unknown files, and suspicious login portals to prevent security risks. After graduating with a philosophy degree from the University of Bristol in 2018, Aaron became a researcher at news digest magazine The Week following a year as editor of satirical website The Whip. Freelancing alongside these roles, his work has appeared in publications such as Vice, Metro, Tablet and New Internationalist, as well as The Week’s online edition.
You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous.