All data is routed from the exit node through a secure VPN connection. This prevents the node operator from detecting your IP address or from finding out any other information. Whereas Tor routes your traffic through a decentralized network of encrypted relays, helping to mask your identity, a VPN encrypts your internet connection and tunnels data via a single server. They serve similar goals but use distinct technologies with different benefits. The Tor Browser works by routing internet traffic through a global network of server nodes to mask your IP address and activity.
Safety Precautions For Using The Tor Browser
It offers outstanding privacy features and there is currently a discounted rate available through this link. As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%.
Use A VPN Before Connecting To Tor
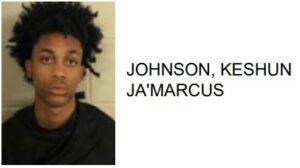
Law enforcement agencies, with the help of cybersecurity experts, have successfully tracked down individuals involved in illegal activities on the Dark Web. The Tor Browser is an essential tool for anyone seeking privacy and anonymity online. By following the tips above, you can use Tor safely and access the dark web responsibly.

How To Sell Counter-Strike 2 Skins Instantly? A Comprehensive Guide
Remember, while these tips can significantly enhance your safety and security, there is no foolproof method to eliminate all risks. Practice discretion, stay informed about current security practices, and always prioritize your online safety when using the dark web. Some services will try to entice you with unrealistic deals and prices.
You can check the Tor network status on the official Tor Project website using any other browser. When you open a website that has a ‘.onion’ mirror, you can set the Tor browser to redirect to its onion counterpart automatically. If the default engine is not available in the list of search engines, you can add it by clicking the ‘Find more search engines’ option. From the drop-down menu below Default Search Engine, choose a search engine you want to set as default in the address bar and search bar. Dark Web, Open Web compared to (surface web), it has fundamental differences in terms of transparency and accessibility. The Open Web consists of all public internet sites that you can easily access through browsers.
- Your information might be on the dark web if it was exposed in a data breach, sold, or stolen by hackers.
- Using Tor Browser, individuals can browse the internet with a higher level of privacy and anonymity.
- Again, we don’t recommend this method, though it might be preferred if the security of Tor exit nodes is of concern.
- For instance, there are some organizations who employ the services of white-hat-hackers for a number of reasons.
- Well, now it’s time to fire up Tails and do a little bit of tinkering.
- This type of security layer is extremely important, especially in order to hide your location and real identity during access to the Dark Web.
The server does not need to provide the IP address, and the user does not need it, instead using an onion address, a 56-character code that clients enter in place of a traditional URL. Remember, the Tor browser connects to the internet differently than regular browsers in an attempt to increase your anonymity online. While the Tor network was not created for illegal activities, as it’s harder to trace websites to their physical location, cybercriminals have also adopted it to host their websites. Before you go much further, it’s important that you close out of other applications and software that offer malicious users on the dark web an entry point into your device or network.
How To Use The Tor Browser & Stay Safe: Full Guide 2025
For more information, read more about the most secure email service providers in my other post. So, to get into the Tor network, follow the steps I’ve listed below. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users. The dark web is a decentralized web, which means that the data is stored on many different servers around the world. Data gleaned from ransomware and data breaches is available on the dark web.
Step 4: Browse Responsibly

And unlike the Tor browser that only secures the traffic that passes through it, a VPN secures all of your device’s web traffic. Tor greatly enhances anonymity, but if an attacker controls both the entry and exit nodes, they could attempt traffic correlation to link your identity to your activity. You can also be tracked by logging into personal accounts, downloading unsafe files, or modifying browser settings that expose your digital fingerprint. Using Tor with a VPN adds an extra layer of protection by masking your IP from the Tor entry node. When it comes to accessing the dark web, getting a reliable virtual private network (VPN) is crucial. A VPN creates a secure and private connection between your device and the internet.
Scammers are active on the dark web, often trying to trick users into revealing personal information or sending money for fake services. Always remain cautious and question the legitimacy of what you encounter. Always use caution when clicking on links from these directories, as some may lead to malicious sites.

Wait For The Browser To Connect To The Node Network
With your VPN up and running and all of your other apps closed down, you’re finally on the brink of actually accessing the dark web. To access the surface web or the deep web, all you need is a standard internet browser like Google Chrome or Safari. For the dark web, though, you need an entirely different entry point known as an overlay network. The first rule for accessing the dark web is to go into it with a purpose or a defined goal. This will help you navigate the dark web safely while staying out of markets you don’t want to come across or engage with.
We Helped Patch A Chromium Bug That Could Leak Your Real IP — Here’s How
(By default, the installation location is the “Applications” folder. Open the Downloads folder on your Mac, and double-click the file you just downloaded. The Tor Browser does have its flaws, which we’ll go into a bit later. Suffice it to say that your Internet Service Provider (ISP) can detect when you’re using the Tor Browser, which can make you the target of increased surveillance by both the ISP and the government. However, there is an easy-to-use way around that, which we’ll talk about later. In this day and age, we understand the importance of online privacy and security and we want to help you make well-informed decisions.

This site will provide in-depth information about the Tor network, internal system, and Tor Project websites. The default option is ‘Ask every time’ which shows you the ‘.onion available’ button in the address bar. But, if you want to automatically redirect to the onion site version of a website, select the ‘Always’ option.
Step 6: Access The Tor Browser On Tails OS
Journalists, activists, and individuals concerned about privacy and censorship often use the dark web to communicate securely and anonymously. Nevertheless, caution should always be exercised when venturing into this hidden realm. The dark web has many legitimate use purposes and contains legitimate content, including dark web mirrors of popular websites and services such as BBC News and Facebook. Despite this, many people prefer not to advertise to their Internet Service Provider that they are accessing the dark web. There’s plenty of illegal content, products, and services available on the dark web. Anonymity doesn’t make carrying out illegal acts any more permissible, so be cautious about making purchases or downloading content.