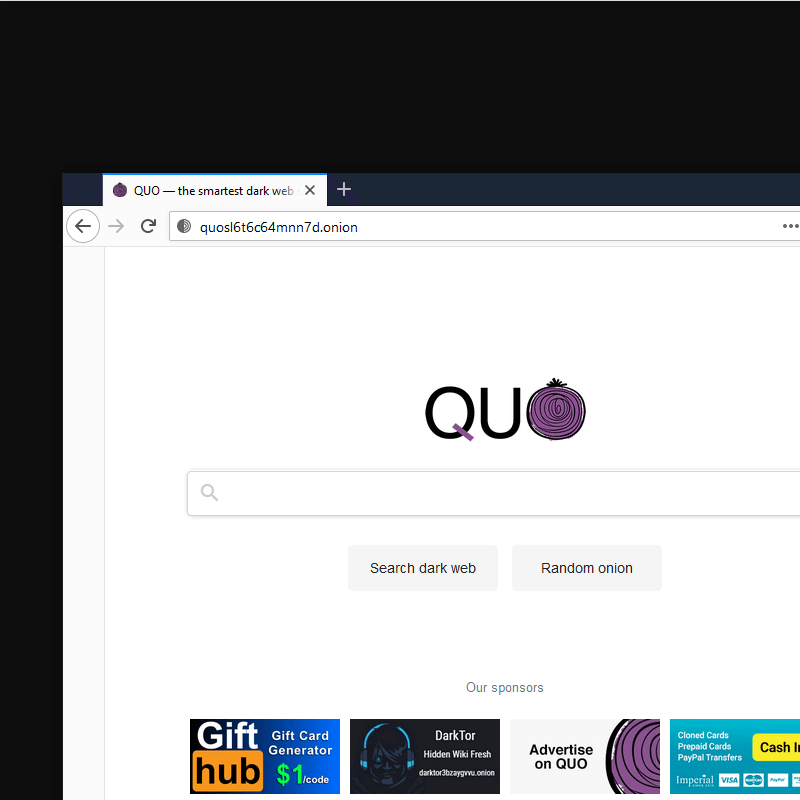
Compromised online accounts can also lead to your credit card information being published on the dark web. A compromised online account is an account that has been accessed without the permission of the person who owns it. Accounts are often compromised due to weak password practices like using short passwords or reusing passwords across multiple accounts. After you have found a credit card that you want to buy, you can place an order.
The Intersection Of Cybersecurity And Artificial Intelligence
By following these steps, you can protect your money and avoid more trouble. Look out for unusual transactions, account activity, or changes to your account info. The key is catching this activity before large volumes of card data make it to market. This type of malware silently infect payment terminals and exfiltrate card data in real-time. What many don’t realize is that much of this stolen data comes from large-scale breaches rather than individual card skimming. Trustwave, A LevelBlue Company, is a globally recognized cybersecurity leader that reduces cyber risk and fortifies organizations against disruptive and damaging cyber threats.
- Once you find a forum or market that offers the service you’re looking for — such as stolen passports — signing up for them is not unlike creating an eBay account.
- Depending on the type of account a cybercriminal compromises, they can gain access to many types of personal information, including your credit card information.
- As one of the prominent platforms supporting such activities, card shops make carrying out such scams relatively easy and popular.
- “There’s a disproportionately high number of cards available in Hong Kong considering the population size, so there’s a much higher chance of any given card being on the dark web databases,” he said.
- This opens the door to applying for loans, creating fake IDs, or taking out credit cards in your name.
Beef Up Your Online Security
At Keeper, Darren leads product vision, global strategy, customer experience and business development. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. Still, for those willing to put up with the inconvenience, the dark web provides a memorable glimpse at the seamy underbelly of the human experience – without the risk of skulking around in a dark alley. Once you have selected a vendor, you will need to communicate with them to arrange the purchase.
Dumps – Magnetic Stripe Data
This enables systems to detect fraud based on minute changes in transaction velocity, merchant category patterns, and even the time of day purchases are made. I’ve worked with family-owned businesses that nearly went under after getting hit with a wave of fraudulent purchases. When fraudulent transactions occur, merchants frequently end up eating the costs through chargebacks. They invest massive resources into fraud detection systems, customer service teams dedicated to handling compromised cards, and the logistical nightmare of card reissuance.

These attacks rely on the actual physical swipes of cards, which then allow the malware to exfiltrate credit card data along with verification data such as a PIN numbers or zip codes. Over half of the 6 million stolen credit card records analyzed came from the US, most likely due to its high rates of card penetration, sizable population, and strong economy. However, stolen US cards commanded a comparatively low price ($6.86 as opposed to the $7.01 average) on dark web marketplaces — the most valued cards (at $11.54 on average) were from Denmark. It is important to note that engaging in such activities is illegal and unethical.
Be Cautious Of Online Transactions
Experian’s free credit monitoring service is one easy way to stay alert. It tracks changes to your credit report and helps you spot potential identity theft early, so you’re not the last to know when something goes wrong. Comparitech researchers sifted through several illicit marketplaces on the dark web to find out how much our private information is worth. Once stolen card data hits the dark web, it can be hard to track down just where it lands, and it can be even harder to prosecute offenders. “The vulnerability depends on factors like the proportion of non-refundable cards (if a card is refundable, the owner can be reimbursed in case of being scammed).” The cards were likely compromised online, using phishing, malware, or JavaScript-sniffers, which are increasingly popular among cybercriminals.

How To Keep Consumers Safe From Carding
Once you have found a marketplace, the next step is to make a purchase. To do this, you will need to create an account and fund it with bitcoin. Most marketplaces only accept bitcoin as a form of payment, so you will need to set up a bitcoin wallet if you don’t already have one. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web.
Threat Actors Are Selling Prescription Pharmaceuticals On Underground Internet Markets

There is some uncertainty about how many of the cards are actually still active and available for cybercriminals to use. Cyble researchers noted that threat actors claimed that 27 percent, according to a random sampling of 98 cards, are still active and can be used for illegal purchasing. AllWorld.Cards appears to be a relatively new player to the market for selling stolen credit-card data on the Dark Web, according to Cyble.
We’re back with another video in our Webz Insider video series on everything web data. Infosec Insider content is written by a trusted community of Threatpost cybersecurity subject matter experts. Each contribution has a goal of bringing a unique voice to important cybersecurity topics.
Cyberattack Darkens Kansas State University, Network Disruptions Rampant
- The threat actor’s marketing strategy involves leaking a large number of credit cards to attract potential clients from hacking and cybercrime forums.
- What many don’t realize is that much of this stolen data comes from large-scale breaches rather than individual card skimming.
- Increased international cooperation between law enforcement agencies will become essential, targeting global criminal networks through coordinated actions and intelligence sharing.
- In fact, the overwhelming majority of leaked credit cards in past months originate from Telegram channels.
- Over 60% of cards were sold alongside other personal information relating to the victim, such as their address, phone number, email address, date of birth, or Social Security number.
- It is a form of financial fraud typically involving stolen credit or debit card numbers, expiration dates, cardholder names, billing addresses, and card verification values (CVVs).
Criminals engaged in carding acquire this sensitive data through various methods, including phishing attacks, malware, skimming devices at ATMs, and hacking into databases of retailers or financial institutions. In conclusion, buying stolen credit cards on the dark web is not only unethical but also illegal. Engaging in such activities puts both buyers and sellers at risk of facing legal consequences.
Step 1: Obtaining The Stolen Credit Card Data
These marketplaces operate similarly to legitimate e-commerce websites, but they sell illegal goods and services. Dark web credit cards are standard, but you don’t have to fall victim to stolen credit cards. With appropriate safety and security measures, you can avoid stealing your credit card information online. In recent years, I’ve observed some shifts in how carding is carried out—changes that mirror broader developments in both technology and threat intelligence research. Notably, cryptocurrency has become a valid option for carding operations, whether through exploiting stolen crypto wallets and accounts or using stolen credit card details to purchase cryptocurrency.
Most vendors will have a preferred method of communication, such as through the marketplace’s messaging system or through an encrypted email service. Be sure to follow the vendor’s instructions carefully to avoid any issues. In the complex and rapidly evolving threat landscape of today, no campus stands secure in isolation. Success in safeguarding our institutions depends on the strength of our partnerships — internally across departments and externally with community stakeholders, vendors and law enforcement. This subreddit is for technical professionals to discuss cybersecurity news, research, threats, etc.