This portion of the internet can be accessed using search engines such as Google, Bing, or Yahoo. It includes websites, databases, and other online resources indexed by search engines and is easily discoverable by users. The dark web isn’t only about illegal activities; its primary purpose is to provide maximum anonymity by making your connection private online through encrypted servers. While the dark web is famously known as an illegal platform for criminal activities, that’s not all about this part of the web. The darknet is a private place where nobody can intercept, monitor, or steal anything online from you.
Should I Use The Tor Browser For Everything?
To protect your security, always use a VPN like NymVPN, disable tracking features, and follow safe browsing practices. The dark web presents various threats, including malicious software and computer viruses, posing risks to users’ systems and data security. Users also face the potential danger of government monitoring and surveillance — or scams and fraud, and other activities that can lead to financial loss and identity theft. On the other hand, the dark web hosts marketplaces and forums where illegal goods and services—such as drugs, weapons, and stolen data—are traded, making it a hotspot for criminal activity. Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions. Many people use Tor to avoid surveillance by government agencies, ISPs, or other entities monitoring online activities.
What Is The Dark Web? Here’s Everything To Know Before You Access It
The websites listed above are all reliable darknet sites but always make sure that you first connect to a trusted VPN provider before accessing any of these sites. Below are the steps based on our tests to access Onion sites safely on your cell phone. The deep web is significantly larger than the surface web, but it’s not inherently illicit or dangerous. In fact, most of the deep web consists of perfectly legal and functional services that are simply not meant for public access. The distinction between the deep web and the dark web is important to understand — while the dark web is part of the deep web, not everything in the deep web is hidden for nefarious reasons. That said, using Tor can be a little intimidating, if not technically challenging.
Tips For Accessing The Dark Web
In general, once you download and install Tor, you’re good to go, though there are some things you should know. First, using Tor is slow, like the early days of dial-up internet, simply because it takes time to route your search requests through all those anonymizers. Second, accessing specific websites directly is a little different.
Alternatives To Tor
Some countries frown upon dark web usage, so it’s good to have your back covered by a reputable VPN service. Select your platform, click on it, and Tor will download in seconds. This time, you should do it, as you’re already hidden by NordVPN’s encryption. Once the app is installed, simply open it up and sign in with the credentials you provided during registration. The dashboard should open properly, indicating you’re ready to connect to any VPN server.
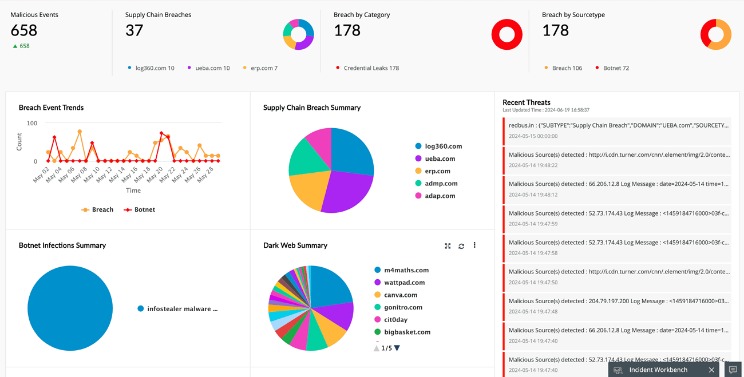
Monitoring For Leaked Personal Data
Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays. Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. It’s also important to never enable Javascript when prompted by a website, as this can compromise your privacy and security.
This is usually done to prevent tracking and website shutdowns typical for this part of the internet. The trick with these onion websites is their accessibility, which is made possible only with Tor. Tor is an abbreviation for The Onion Router and now, we can see why.
How To Safely Access The Dark Web
The open web, also called the surface web, includes any public web content that is indexed by search engines. Webpages on the open web will show up in search results on sites like Google and Bing. Though a large volume of traffic visits on the open web every day, it only represents 4% of the content on the internet. In addition to Tor’s three layers of encryption, the browser also deletes your browsing history, erases your tracks and prevents sites from identifying and tracking you, explains Wired. Keep in mind that if you use your real name, address, email address or other identifying information anywhere on the dark web, you’re giving away the protections provided by Tor. Be wary of buying services or products, even those that aren’t illegal, because the dark web’s anonymity makes it a haven for scammers.
- Many turn to the dark to grab such medications with their private and secure networks.
- Your gadget’s internet traffic routes through the VPN’s provider server first and then via Tor Network before it reaches the destination website.
- For instance, there are some organizations who employ the services of white-hat-hackers for a number of reasons.
- The Tor network allowed safe communication channels for political dissidents and American intelligence operatives around the world.
This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting. The “onion routing” technology underpinning the dark web was developed by researchers at the U.S. Initially designed for secure military communications, it evolved into a broader tool for online anonymity, later expanding to public use with the Tor network. Another challenge of finding dark web sites is that they don’t often last long. Many sites become defunct quickly, either because they are shut down due to illegal activity, their founders lose interest, or they change addresses and names to avoid detection.
Use a computer that is not connected to your home’s internet to protect other computers on your network from malware infections or privacy intrusions. While the iOS solution is not an official one, the Tor Project links to it, providing the browser its tacit approval. We’ve also looked at how Tor allows users to access the dark web, and we’re now aware of the resources and dangers that await us there.

A Dark Web Search Engine
Freenet is one of the oldest anonymity networks, focused on providing censorship-resistant communication. Instead of simply routing traffic, Freenet stores encrypted chunks of data across nodes. The phrase “how to access the dark web” often sparks curiosity, but the reality is that it comes with immense cybersecurity risks. For businesses, the priority should be monitoring dark web activity for threats, not exploring it casually. When using Tor, your traffic will never reach its intended destination directly, as it would on surface web browsers.
The Dark Web is a part of the Deep Web that remains hidden and can only be accessed with special browsers. Focusing on anonymity, it is a place where you can find information that is not otherwise accessible over the regular web. However, it can be quite dangerous, especially if you do not take the necessary precautions, and can pose risks like phishing, hacking, and more. If you want to access the Dark Web safely, there are certain steps you need to follow to ensure your safety and privacy. Now that your connection is active, it’s encrypted and untraceable by your internet provider. Everything you do is protected by NordVPN, which is key to accessing the dark web and enjoying it privately.