Choose a VPN known for strong encryption, a no-logs policy, and compatibility with various devices. The Hidden Wiki is a popular onion link directory on the dark web offering categorized lists of sites. Use VPN, avoid logging into personal accounts, enable Tor security settings, and stick to trusted sites. Tor anonymizes by bouncing traffic through relays; VPN encrypts and routes through a single server. While difficult, tracking is possible if security measures are misconfigured or if users reveal personal information.
Disable JavaScript & Use Privacy-preserving Tools
Then individual applications must each be separately configured to work with I2P. You’ll need to configure your browser’s proxy settings to use the correct port on a web browser. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method.
The Hidden Wiki & Co
Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy. By following this dark web access guide, applying Tor browser safety practices, and knowing when it’s safe to browse the dark web, you can navigate responsibly without compromising your security. With rising curiosity around hidden corners of the internet, many professionals wonder, “how to access the dark web” safely. From cybersecurity researchers to IT managers, understanding how to navigate the dark web can help monitor cyber threats, protect sensitive data, and investigate cybersecurity incidents. To find what you’re looking for, you may need to try multiple search engines or visit directories of trusted .onion links.
Using a VPN obstructs your privacy and specifies an entry node, and a VPN with an obfuscation feature makes it look like to your ISP that you are browsing the regular web. However, your information is vulnerable without a VPN since it has only Tor’s layered encryption as protection. A solution to this is to set up a VPN within your router, effectively encrypting your entire connection. Furthermore, Freenet enables users to link in both Opennet and Darknet modes. Opennet mode uses a decentralized P2P network and centralized servers to connect and automatically assign your peers. Conversely, the Darknet mode allows you to create restricted anonymity networks of people you only trust or know to share content with.
Now my computer is connected to the Latvia Onion #1 server, and Now you also connected, If yes then We will ready for next step. Now time for connecting with the best server, but inside NordVPN, you can select Onion Over VPN support server. For server selection, you need to click on Countries after then Speciality Servers. Once you click on Speciality Servers, you will get the NordVPN screen like below.
Master Ethical Hacking: A Guide To The Best Certifications And Courses
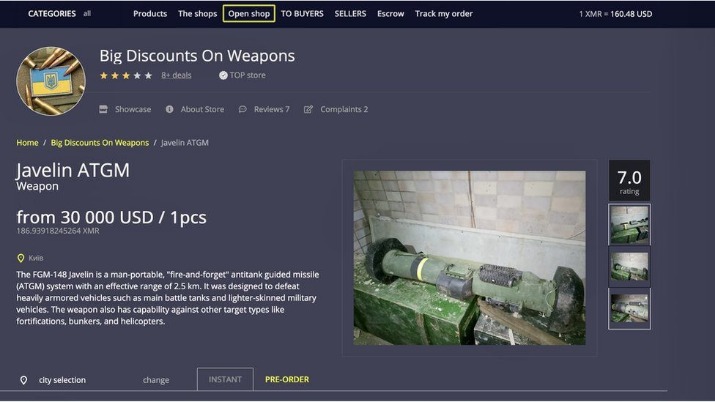
Proton VPN makes it easy to safely gain access to the dark web by connecting users to the Tor Network in a single click. Its server network includes dedicated nodes set up to reroute internet traffic through the Tor network. Tor Over VPN servers are identified with an onion symbol and found in the country list. Cybercrime services, such as hacking tools and stolen databases, are available for hire, creating a marketplace for illicit online activities. Dark web monitoring platforms provide secure communication channels for individuals seeking to expose information without fear of retribution. Additionally, the Dark Web serves as a haven for those in censored environments, offering access to restricted information and enabling the free expression of opinions.
How To Access The Dark Web Or Deep Web Using Tor
Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Prior to Keeper, Darren served as an advisor to JiWire, now called NinthDecimal. NinthDecimal is the leading media and technology service provider for the WiFi industry.
Dark Web Search: The Best Dark Web Search Engines In 2025
The victim types in their information, thinking they’re accessing a site that they know and trust, but they’re actually giving away their data. There are a lot of these sites across the dark web, which is why you have to be extra careful. The easiest way to avoid falling victim to them is to simply not provide any personal data when browsing the dark web. Many cybersecurity and tech experts recommend using a VPN whenever you want to access the dark web via the Tor Browser or any other specialist browser. A quality VPN like ExpressVPN will encrypt your internet traffic and mask your IP address, providing an extra layer of anonymity when establishing the initial Tor connection. As such, it’s important to be extremely careful when accessing the dark web, as you could inadvertently access a site containing, displaying, or linking to illicit content in some form.
The right tools, like Forest VPN, can help you explore safely and securely. Let’s unpack the steps and safety measures you’ll need for this expedition. It’s important to note that not all websites on the dark web are illegal or malicious. Some hidden sites are used for legitimate purposes, such as private communication, whistleblower platforms, and forums for activism and free speech.

Navigating The Dark Web Safely
I2P cannot be used to access .onion sites because it is a completely separate network from Tor. Instead, I2P uses its own brand of hidden sites called “eepsites”. A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. If you want to access the dark web, your first step toward a more private experience should be to secure your internet connection and data with a reliable VPN. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer.
Tor has an in-build slider which lets you adjust the level of security. This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman. It’s also used by journalists, advocacy group members, and political refugees in hiding.

The Tor Browser is the most trusted option for accessing the dark web, but it’s not invincible. In fact, the network has faced real challenges, including seven months of DDOS attacks in 2022 (Securityaffairs)2. In this article, I’ll guide you through the safest way to enter the dark web, like downloading Tor securely, booting from Tails, and using a trustworthy no-logs VPN. By the end, you’ll know how to explore with confidence while keeping your data safe.
Downloads
Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites. Meanwhile, Facebook also offers dark web access to their social network. Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic.
- Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine).
- The button above leads you to its website where you can claim an exclusive 70% discount for the 2-year plan.
- To be on the safe side, we recommend combining the Tor or onion browser with a secure VPN, such as NordVPN.
- In brief, while exploring the dark net isn’t inherently illegal, you should be careful about the material you interact with.
- It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity.
The surface web (also called the Visible Web, Indexed Web, or Clear Web) is the part of the internet you can access anytime using mainstream browsers, like Chrome, Firefox, Safari, etc. It includes any page that you can find with a simple Google search. However, your access is limited to the information that the website’s administrator permits you to see.