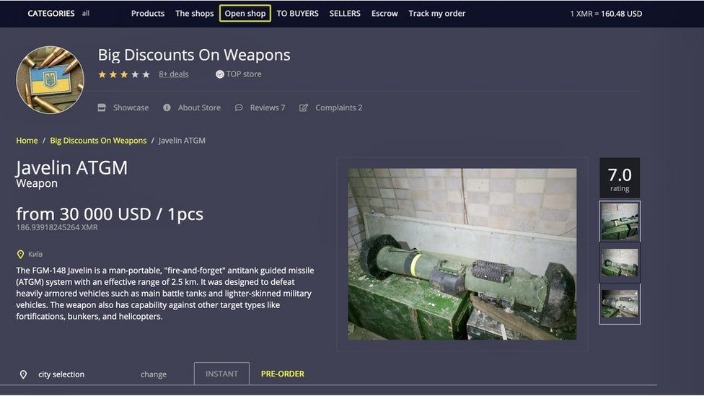
Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data. As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators.
- Knowing about various types of ransomware and common hacks can help you better prepare to spot cybersecurity threats on the dark web.
- Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place.
- You could compare the deep web with our knowledge about the oceans.
- The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines.
- Examples of this might be e-mail accounts or registration-only forums.
Facebook Onion Site
This means that it is not possible to find out where the server is actually located using conventional means. Due to this cascading, the use of file sharing services such as Bittorrent via the Tor network also makes no sense. What we see and use on the internet in web browsers such as Edge, Chrome, Firefox, Opera, and Safari is only a fraction of what is actually available. Information and data can be published and exchanged with the greatest possible anonymity on the so-called darknet, as PCWorld first noted in 2013. However, most are outdated and have not kept up with the changing landscape. For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question.
The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight. Just like you had to set up your VPN app before connecting, it’s best to make sure your overlay network client is adequately set up for safely accessing the dark web. Though not entirely shoddy, the dark web has a reputation for hosting illegal activities. It does support whistleblowers by offering them anonymity and secure communication in an oppressive regime.
Understand Legal Risks
And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing. Established in 2012, the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears.
Added Security: Use A VPN
Unlike typical web browsers, Tor Browser uses onion routing, which encrypts and routes traffic through multiple servers around the world to hide your IP address and provide private browsing. In addition, all domains on the Tor network end with the top-level domain .onion (instead of .com). The many layers of an onion represent the multiple layers of encryption in the Tor network.
Stick to tried-and-tested sites and do your best to avoid scams. If you manage to not expose your private information and avoid illicit activities, you can be sure everything will be okay. This internet space can be dangerous but you can safely get on it by using a VPN and then connecting to Tor.
You could consider the clear or surface web the “top” and visible layer of the internet, easily accessible using a browser such as Safari, Chrome, Edge, or Firefox. Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. There are some websites you can absolutely get in legal trouble for even visiting, so proceed with the utmost caution.
Meet LockBit 50: Faster ESXi Drive Encryption, Better At Evading Detection
However, in general, unless you’re 100% sure the service is legitimate, or the product you’re buying is legally sourced, don’t buy anything on the dark web. Just like there are privacy and security best-practices for using the surface web, there are some dos and don’ts for browsing the dark web. Most online content (whether stored in centralized servers or on a distributed P2P network, like blockchains) actually belongs to the deep web. This one is specially designed to help users access the free web worldwide, making it especially handy for users in countries where Tor is restricted or banned.
How To Access The Dark Web Using The Tor Browser
The platform is protected from government interference and malicious attacks to protect the user. In addition, it ensures that no record of communication is stored. This step-by-step guide is designed to help beginners navigate this hidden part of the internet safely and securely. It’s legal to access the dark web in the U.S. and most other countries. By some estimates, well over half of dark web content is illegal. This can include illicit marketplaces, drugs, cybercrime and hacking groups, and extremist, violent platforms.
The good news is that the BBC Onion site is an international edition. As a result, it not only focuses on the UK but also provides worldwide news. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023.

Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. However, there are some significant variances in the background despite the similarities.
Is Tor Enough, Or Do I Also Need A VPN?
As mentioned, Tor servers are completely concealed from regular internet browsers. However, by connecting to them using the Tor browser you can easily access them in a completely private and anonymous manner. Regular browsers like Firefox and Chrome can’t access this concealed portion of the internet, because they are not designed to find websites listed using The Onion Router hidden service protocol. By understanding the hazards you may face in the Dark Web and implementing the precautions outlined above, you’ll be better equipped to minimize your exposure to scams, malware, and identity risks.
Ultimately, the Dark Web is neither purely nefarious nor inherently virtuous—it’s a dynamic environment shaped by the motivations and actions of its users. Your decisions, responsible conduct, and awareness of potential risks will determine your experience in this hidden realm. Accessing the Dark Web can expose you to a range of risks that might not be immediately apparent. While many visitors manage to browse hidden services without incident, staying safe requires constant vigilance. This section outlines the primary dangers and offers practical advice to help you navigate these shadows responsibly.
Cracking down on many illegal marketplaces on the dark web is the result of such monitoring. So, you risk being flagged or investigated for visiting certain sites, even without criminal intent. Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor is by far the most widely used dark web network and is the biggest network in terms of content and activities.
Unique Features
However, having a faster computer does help as you’d be running Tor + the VPN. In worst-case scenarios, people are even blackmailed or fall prey to honeypots (darknet markets setup by law enforcement agencies). You can simply search for “Darknet markets” on the search engine and it’ll get you hundreds of them. Note that if you’re using NordVPN, go with the “Onion over VPN” servers.