Within the dark web, there are various hidden websites, known as darknet markets, where illicit goods and services are bought and sold. These can include drugs, weapons, stolen data, and even hacking services. It is important to note, however, that not all activities on the dark web are illegal. Many individuals use it to communicate securely and anonymously or to access information that may be restricted or censored in their countries. The Tor browser uses the Tor network, which was developed in the mid-1990s by US Naval Research Laboratory employees.
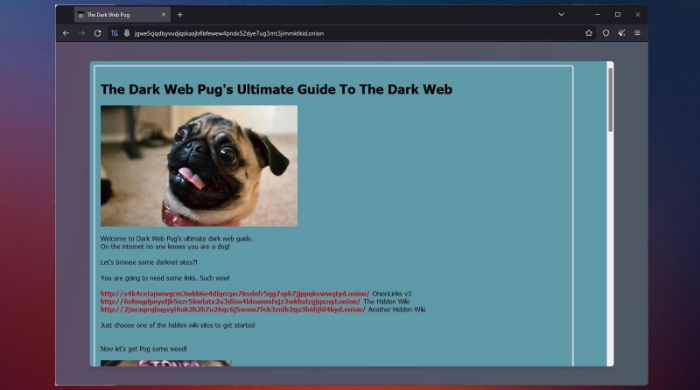
However, if you’re planning to spend any time exploring the dark web, it’s crucial you take the necessary precautions to keep your device, your data, and yourself safe. The first rule for accessing the dark web is to go into it with a purpose or a defined goal. This will help you navigate the dark web safely while staying out of markets you don’t want to come across or engage with. While there is a lot of criminal activity on the dark web, there’s nothing actually illegal about accessing the dark web. In certain countries, the dark web facilitates political discourse and conversation that would otherwise be censored, outlawed, or eradicated in entirety. Sites on the dark web don’t come with easy-to-remember URLs, and many disappear suddenly.
How To Install Tails OS

Cloudwards.net may earn a small commission from some purchases made through our site. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. This infects a user’s device and essentially blocks them out of it until they pay a “ransom,” usually in the form of cryptocurrency (so it’s harder to track and recover). Users could accidentally fall victim to ransomware just by clicking the wrong link or downloading a file on the dark web. As well as phishing scams, a multitude of other scams operate across the dark web. There are many fake marketplaces and platforms that might offer to sell you goods or services but actually take your money without providing anything in return.
The Hidden Wiki & Co
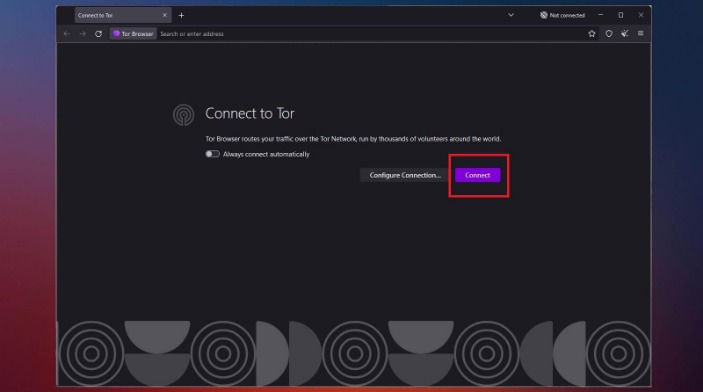
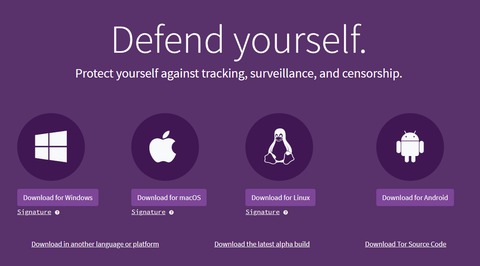
The dark web is a small, hidden subset of the deep web that requires special tools to access. Tor’s browser connects to what’s called the Tor network, which establishes an anonymous connection that protects against network surveillance and tracking. In addition to being able to access any website you can in a standard browser, you can also access Dark Web URLs that end in .onion. Now you’re probably asking, is the Deep Web and Dark Web even legal?
Because it’s easier to contain malware in a virtual environment, which can be fully controlled. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security.
How To Install Windows 11 With An Offline Account
Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges. As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps. VPN-over-Tor breaks dark web compatibility, reintroduces trust in the VPN provider, and creates unnecessary complexity.
- The 2024 Global Threat Report unveils an alarming rise in covert activity and a cyber threat landscape dominated by stealth.
- A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous.
- You’ve probably heard that Tor makes you anonymous on the dark web — but that’s only half true.
- Dark net websites are called “Tor hidden services“, and they can be distinguished from normal websites by their URLs.
- Relays help route traffic securely by passing encrypted data through multiple nodes before reaching its destination.
- Instead of search engines, you’ll need to rely on directories or specific .onion links.
Some users explore the dark web out of curiosity or to gather information that may be unavailable on the surface web. However, the hidden nature of the dark web does attract criminal elements who exploit its anonymity for illicit purposes. In theory this should make your deep web browsing (as well as your regular web browsing) entirely private from interlopers. However, since your traffic is routed through nodes that you don’t have any control over, you are at the mercy of whoever operates these nodes. Serving is the final step of the process for search engines like Google.
Opennet mode uses a decentralized P2P network and centralized servers to connect and automatically assign your peers. Conversely, the Darknet mode allows you to create restricted anonymity networks of people you only trust or know to share content with. The VPN has over 3,200 servers distributed across 100 countries worldwide. These servers offer decent speeds for browsing the dark web and other activities like streaming, gaming, or torrenting. Thankfully, it allows you to connect unlimited devices, which will be useful when exploring the onion links with many devices. ExpressVPN is a top-notch VPN service with features like super-fast speeds on most servers, its onion site, and robust security, making it easy to browse the onion web pages.
Install A Virtual Private Network (VPN)
I2P cannot be used to access .onion sites because it is a completely separate network from Tor. Instead, I2P uses its own brand of hidden sites called “eepsites”. A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity.
You should now be equipped with the tools and knowledge necessary to surf the dark web. Remember that accessing it is not legal in every country, so check your local regulations before doing so. By employing these tips and tricks, you can navigate the dark web with increased confidence and better protect your safety and privacy.
Understanding these risks is essential for anyone considering accessing the dark web. In the next section, we will discuss the precautions you should take before venturing into the dark web to protect your online safety and privacy. Additionally, accessing the dark web increases the risk of being targeted by hackers and cyberattacks.
Major Risks And Downsides
That means that only 0.024% of all the known pages are findable in Google’s search engine. The users only have access to a fraction of the available data and web pages. The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo. The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more.
Method II – VPN Over Tor

Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post. It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims.
When not demystifying digital security, he indulges in diverse hobbies from bonsai to powerlifting. While it’s important to be safe when accessing the dark web, simply getting on Tor will not magically enable you to locate and ID the bad guys. As mentioned earlier, navigating the dark web can be a challenge in and of itself due to its anonymized structure, to say nothing of tracing a threat actor back to a real-life name and address. In the simplest of terms, both deep and the dark web are a subset of sites on the internet that are not indexed for traditional search engines. Dark web sites also have an added layer of anonymity because they must be accessed using specialized software, like Tor. The last thing you need to do to access the dark web is find links for sites hosted there.
- A VPN and Tor should be used together and it is advisable to connect via a VPN to Tor, rather than vice versa, for the best protection possible.
- (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder.
- Accessing the dark web comes with inherent risks and potential dangers that users must be aware of.
- This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware.
- DarkBlue regularly scrapes dark web sites, copying their data and ingesting it into a single, searchable database.
- This operating model is what makes the dark web such a valuable and appealing tool for cybercriminals and other people with questionable intentions.
However, it’s up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking. First — and this is strongly recommended — you should install a Virtual Private Network (VPN). Also, you need to use a privacy-focused browser such as the Tor network to connect via nodes and proxy servers, which are more secure and aim to anonymize traffic requests. The Tor browser is able to access the special domain names, with the suffix .onion, used in the dark web.
How Many People Use Dark Web
Additionally, always keep your Tor Browser up to date to benefit from the latest security enhancements and bug fixes. Regularly check the Tor Project’s website for updates and install them promptly. PrivateVPN is based in Sweden, which is a member of the SIGINT Seniors Europe international intelligence-sharing alliance. Although PrivateVPN has what sounds like a true no-logs policy, it has yet to be independently audited. It will still be able to get the job done if you’re interested in dark web browsing.



