Many turn to the dark to grab such medications with their private and secure networks. Some common pain relievers and sleeping pills available in the EU are illegal in various Middle Eastern and Asia countries. The dark web has several convenient uses, which are not all basic. People who live under a government that deeply supervises or censors internet traffic eventually get attracted to the dark web.
Step 3: Start I2P
Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account. By following these steps, you are on your way to exploring the hidden depths of the internet and enjoying a heightened level of online privacy and anonymity. This requires your connection to go through multiple nodes and relays, which will slow down browsing on Tor. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges. As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps.
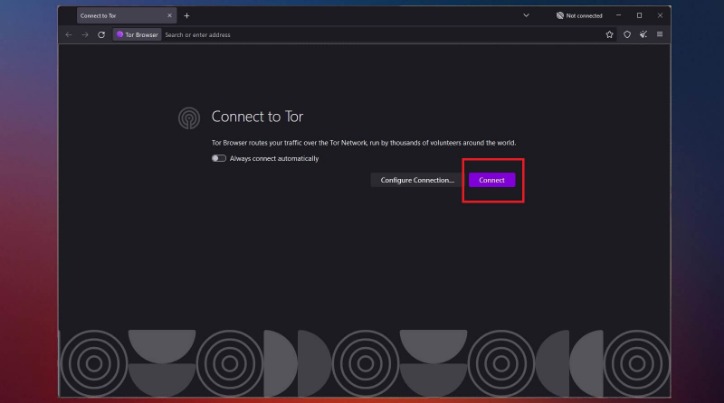
Get Started With Tor

Especially if you are planning to access it without enabling online privacy and security, you might be in for a nasty surprise. No matter what you do online, there’s always at least some risk of being tracked — especially on the dark web. While no method guarantees complete anonymity, you can minimize the chances of being tracked with the right precautions. As a general rule, it’s best to use the default settings in Tor or the Onion Browser. Changing any of the default settings can make websites misbehave or not load correctly.
Forest VPN: Your Gateway To Safe Browsing
While the Tor Browser is designed to protect your privacy, it’s not 100% safe on its own. Without a VPN, your ISP can see that you’re using Tor, and the first Tor server (entry node) can see your real IP address. Additionally, if Tor leaks, your IP address will be exposed to everyone. You can eliminate these privacy concerns by connecting to a VPN before launching the Tor Browser in a setup called Tor over VPN. For most people, Tor over VPN is the safer and more practical choice. It protects your real IP address even if Tor leaks, is easier to set up, and works with most major VPN services.
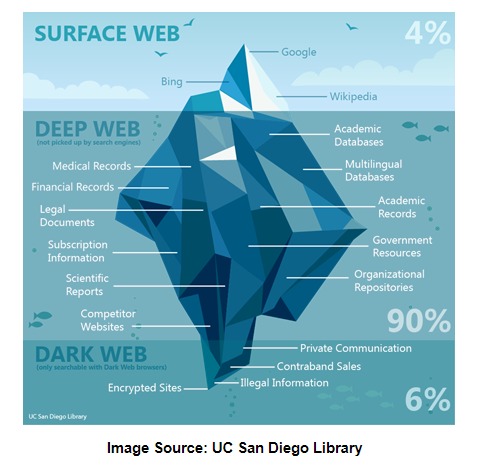
As such, it’s important to be extremely careful when accessing the dark web, as you could inadvertently access a site containing, displaying, or linking to illicit content in some form. It’s illegal to use the dark web for any form of criminal activity, like buying stolen goods, drugs, user accounts, and so on. The dark web is a part of the internet that isn’t indexed by search engines. You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. The dark web presents various threats, including malicious software and computer viruses, posing risks to users’ systems and data security.
Regularly Update Your Software
Tor has an in-build slider which lets you adjust the level of security. This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman. It’s also used by journalists, advocacy group members, and political refugees in hiding. Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use.

What Is The Safest Way To Download Tor Browser?
You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client.
Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network. The dark web has no shortage of criminal activity, scams, phishing sites, suspicious links, and malware designed to trick newbies. Links posted to the clear web, in particular, are often malicious.
Dark Web Monitoring And Identity Theft Protection At Your Fingertips
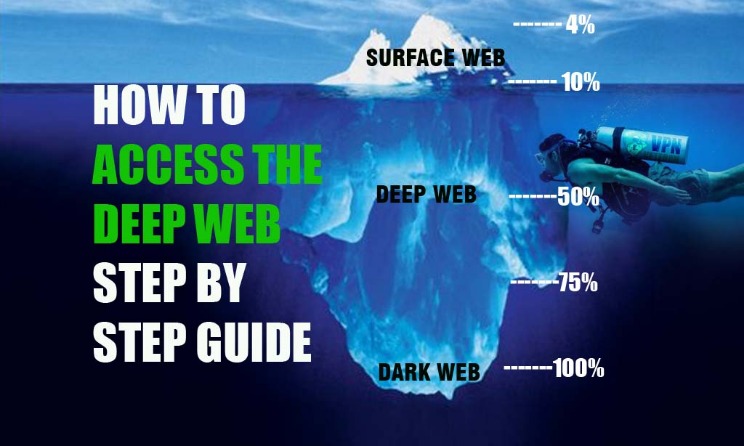
A lot of the user data that gets stolen or leaked from big platforms ends up on the dark web, where users buy, sell, and exchange it among themselves. As explained earlier, you won’t be able to access the dark web the same way you would the surface web. You can’t type dark web addresses into your usual browser or search for them via Google. Instead, you have to use a specialist browser, designed to navigate the dark web. Given the prevalence of malware across the dark web, it’s vital to have antivirus software installed and active on your device when accessing it.
Ensuring Security And Anonymity
Since using Tor can itself draw suspicion, a VPN masks the fact that you’re using it. It also adds a crucial layer of encryption before your traffic even enters the Tor network. You’ll find the more dangerous content and activity at the dark end of the deep web. This is where Tor websites are located, deemed the ‘dark web,’ and can only be accessed by an anonymous browser.

Social Engineering And Identity Exposure
- It’s possible to buy and sell illegal drugs, malware, and prohibited content in darknet marketplaces.
- When you click through from our site to a retailer and buy a product or service, we may earn affiliate commissions.
- Most people can use the Tor browser right away, but some countries block or censor Tor.
- However, the Dark web is a portion of the deep web that can only be acquired through special tools.
- It uses TrustedServer technology on the entire server network to wipe out your data after every session.
Then, install Norton 360 Deluxe to get AI-powered scam detection to help secure your browsing against online threats. Accessing the Dark Web can expose you to a range of risks that might not be immediately apparent. While many visitors manage to browse hidden services without incident, staying safe requires constant vigilance. This section outlines the primary dangers and offers practical advice to help you navigate these shadows responsibly. By following these steps, you enter the Dark Web with more confidence and preparedness. Although it’s not inherently illegal to access the Dark Web, remember that certain sites and activities may be.
While ProtonMail has a solid commitment to privacy, its location has caused problems for users in the past. In 2021, it was forced by the Swiss courts to begin logging the IP addresses and browser fingerprint information of one of its customers. While NordVPN is undoubtedly a great service, it’s not without fault. In 2018, someone gained access to a third-party data center in Finland. NordVPN responded aggressively by upgrading its entire infrastructure to RAM-only servers and ending its reliance on rented servers. It also introduced a bug bounty program, hired a cybersecurity consulting firm to test its infrastructure, and then carried out a third-party security audit.