
NinthDecimal is the leading media and technology service provider for the WiFi industry. He was formerly the Chief Financial Officer and a principal shareholder of Apollo Solutions, Inc., which was acquired by CNET Networks. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. These attacks often include stealing victims’ data and threatening to release it on the dark web if the ransom isn’t paid.
How Many Dark Web Sites Are There?
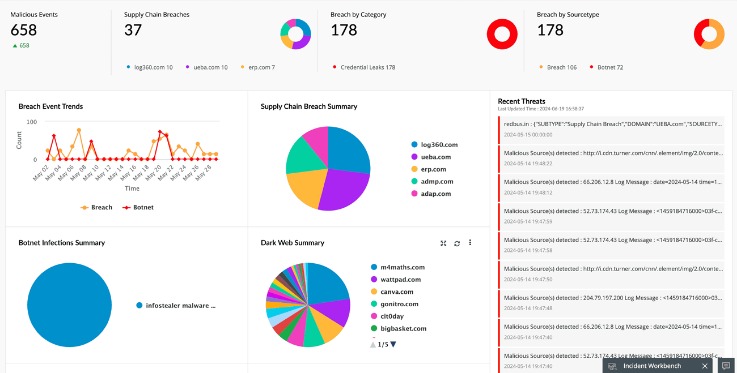
- Data breaches happen when a hacker steals user data from a company’s database.
- There are several whistleblower sites, including a dark web version of Wikileaks.
- To access a dark web resource, you will need to know its web address to the letter.
- Most users on the Dark Web are logged into a Virtual Private Network (VPN) to further conceal themselves.
Venturing further into the deep web does bring a bit more danger to the light. For some users, portions of the deep web offer the opportunity to bypass local restrictions and access TV or movie services that may not be available in their local areas. Others go somewhat deeper to download pirated music or steal movies that aren’t yet in theaters. If we continue to visualize the entire web like an iceberg, the open web would be the top portion that’s above the water. From a statistical standpoint, this collective of websites and data makes up under 5% of the total internet. For added peace of mind, your Aura plan comes equipped with a $1,000,000 insurance policy that covers eligible losses resulting from identity theft.
VPNs are also used for accessing geo-locked content hosted by streaming services. The best VPN options are paid-for and subscription-based, as many free options will either throttle your speed or collect your data. No longer restricted to dial-up, many of us now consider access to a stable high-speed internet connection a critical element of our daily lives. We pay our bills online, check our bank statements, communicate via email, find information, and maintain a presence on social media. Darren Guccione is the CEO and co-founder of Keeper Security, the world’s most popular password manager and secure digital vault.
That Innocent PDF Is Now A Trojan Horse For Gmail Attacks
The deep web is just the part of the web that isn’t accessible by search engines. You won’t find these websites when you use a search engine like Google or Bing, but they’re otherwise normal websites. The “dark web” is a smaller part of the deep web that can’t be accessed without special software. The moderators enforce a strict policy against posting links to illegal products or services, so you’re more likely to find safer dark web addresses here.
Services Sur Le Dark Web
For those who have endured harm at the hands of others, they may not want their attackers to discover their conversations about the event. If an activity is deemed illegal by the governing bodies you fall under, then it would be illegal. However, you can still take illegal actions within Tor that could incriminate you regardless of the browser’s legality. You could easily use Tor in an attempt to pirate copyrighted content from the deep web, share illegal pornography, or engage in cyber terrorism.
What Is The Tor Browser?
In the CrowdStrike 2024 Threat Hunting Report, CrowdStrike unveils the latest tactics of 245+ modern adversaries and shows how these adversaries continue to evolve and emulate legitimate user behavior. Though the terms dark web and deep web are often used interchangeably, they are two distinct concepts. Based on Mozilla’s Firefox, this browser hides all that pinging about in the background. That’s the desktop edition, but there’s a version for Android and an unsupported onion browsing app for iOS.
- Some of the tales are enough to make you tape over your webcam and disable your router just in case.
- Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter an onion URL to start browsing.
- For example, the Epic browser is programmed to always run in private mode, so it doesn’t store data about which sites you visit.
- This makes it extremely difficult for your ISP or anyone with access to your internet records to know which sites you visit or apps you use.
- It’s also used by political whistle-blowers, activists, and journalists who may be censored or could risk political retaliation if discovered by their government.
Data brokers such as LocalBlox for instance crawl the web and store information about business and consumers to sell for marketing purposes. Some of these are well-known, established threats that circulate in this nook of the web. However, others may be taking advantage of the dark web’s reputation to trick users out of large sums of money. Also, some users on the dark web may attempt phishing scams to steal your identity or personal information for extortion.
SecureDrop — Partagez Des Informations Anonymement Avec Les Médias
The dark web, however, requires special software to access, as explained below. Our goal is to deliver the most accurate information and the most knowledgeable advice possible in order to help you make smarter buying decisions on tech gear and a wide array of products and services. Our editors thoroughly review and fact-check every article to ensure that our content meets the highest standards. If we have made an error or published misleading information, we will correct or clarify the article.
However, it also lingers all across the dark web to infect unsuspecting users just like it does on the rest of the web. When viewed through this lens, the dark web’s legality is based on how you as a user engage with it. You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom. Others may act in ways that are illegal for the protection and safety of others. Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves. As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online.
It’s somewhere Google and Bing don’t index, and you need special tools to get to it. The dark web offers both benefits and risks for users going into it, but the intent of the user will also impact this. Similar to using a standard web browser to access the open web, the act of using Tor or a dark web browser to access the dark web is not illegal in and of itself. It is illegal to perform illegal acts on the dark web, regardless of the level of anonymity provided by the platform.
Tor’s Vulnerabilities
It actively scans workflows, services, and systems to detect compromised credentials. Regardless of the purpose of your interests in the dark web sites, whether it is for security purposes or for communicating anonymously, prudence is advised. It is dangerous because it contains many fake links, unreliable markets, and risks of police or hacker intervention.
Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. Sign up for our newsletter and learn how to protect your computer from threats. Depending on what you intend to do on the Dark Web, some users recommend placing tape over your laptop’s webcam to prevent prying eyes watching you. If you’re reading in the hope of finding out about torrent files, check out our separate guide on how to use torrent sites in the UK.
They are confusing the generally dodgy Dark Web with the much bigger and generally more benign Deep Web. Thus the ‘Deep Web’ includes the ‘Dark Web’, but also includes all user databases, webmail pages, registration-required web forums, and pages behind paywalls. There are huge numbers of such pages, and most exist for mundane reasons. Hackers stole the data and threatened to upload it to the web if the site did not close down, and they eventually acted on that threat. The spouses of Ashley Madison users received blackmail letters demanding they pay $2500 in Bitcoin or have the infidelity exposed.
The dark web consists mostly of services on the Tor network, but also includes some other networks like I2P, Freenet, and small peer-to-peer ones. For the purpose of this article, “dark web site” will specifically reference services on the Tor network. SentinelOne’s agentless CNAPP provides KSPM, CSPM, AI-SPM, and EASM features to assess vulnerabilities in cloud workloads, IT infrastructures, and services. It enforces compliance with regulatory standards like SOC 2, NIST, and CIS Benchmarks while identifying sensitive data exposures. The platform records detailed cloud workload telemetry using Storylines technology.

It has billions of sites and addresses, it is amazing that we can both search for – and find – anything. That said, anonymity comes with a dark side since criminals and malicious hackers also prefer to operate in the shadows. For example, cyberattacks and trafficking are activities that the participants know will be incriminating. The dark web was once the province of hackers, law enforcement officers, and cybercriminals. However, new technology like encryption and the anonymization browser software, Tor, now makes it possible for anyone to dive dark if they’re interested.
To visit a site on the Dark Web that is using Tor encryption, you have to use Tor. Just as your IP address is bounced through several layers of encryption to appear to be at another IP address on the Tor network, so is that of the website. Avast BreachGuard monitors the dark web for data breaches around the clock. If a breach is detected, BreachGuard will notify you right away and help you take the steps you need to secure your data immediately. Dark websites can be visited only with a suitable dark web browser, and most dark web URLs are strings of seemingly random letters and numbers — nothing like the easy-to-remember web addresses on the surface web.


