He was also inspired by his favorite book, Alongside Night — about a society built upon an open marketplace — to create what would become the Silk Road anonymous market. Darknet markets and deep web forums have been attacked quite often in the past with severe DDoS attacks. The seizure of the Hydra servers and cryptocurrency wallets was made this morning in Germany by the German Federal Criminal Police (the Bundeskriminalamt), in coordination with U.S. law enforcement. Before diving into extraction of the data, I took a look at counts of the crawls themselves to get a sense of the scale of the market. Each page in the p directory corresponds to a single product listing; each in the vendor directory corresponds to a vendor’s ‘storefront’ page.
We help you source life-changing products from far markets to your doorstep. One box is used for looking up vendors by their names, while the other one is for looking up vendors by their public PGP keys. Virtual Machine (VM) is a cloud-based emulation of a computer system that provides the functionality of a physical computer system. The site went offline shortly after I spent couple minutes on it and has been displaying a 503 error ever since.
Silk Road 20
- Some of this was driven by moderators trying to improve security measures and some due to ‘denial of service’ attacks.
- Not many people know about its existence, let alone venturing there.
- Good threat intelligence helps to monitor both intentional and inadvertent use of corporate brands so that these brands can be protected.
- People have been sharing their thoughts about drugs – the fun aspects, adverse effects, harm reduction messages – for many years.
- The Silk Road dark web link was tydgcecykixpbu6uz.onion.
- Dream Market has been a stalwart of the Darknet marketplaces wave of DDoS attacks is being launched dark0de darknet arket by rival market Agora If much of.
IOHK builds blockchain solutions for enterprise, government, and private sector clients as well as the Cardano smart contract platform. The length of settlement times vary widely depending on the structure of the different networks and organizations that process the transaction. Your email address is used only to let the recipient know who sent the email.

What Is A Cloud Access Security Broker?
Interesting Directory with deep web links divided into easy to use categories and online since several years. It’s pretty simple for hackers to gain financially, using malicious software to access and encrypt data and hold it hostage until the victim pays agora darknet market the ransom. Darknet markets are dynamic and constantly changing within the context of many disruptions, both external (e.g. law enforcement and denial of service attacks) and internal (exit scams).
Cypher Market Darknet
Data is collected weekly and figures represent snapshots of specific points in time. We monitor larger markets (with 100 or more listings) that are in English language. The intersection of drugs and the internet is not a new thing.
Reader Services
- The single market strategy is the European Commission’s plan to unlock the full potential of the single market.
- This template will give you some ideas on how to surprise your followers.
- These attacks were often designed to disrupt market operations to either extort money from moderators or entice customers to rival marketplaces.
- As much as I agora darknet market enjoy browsing the Dark Web, I take my private data seriously and I never go on without using a VPN as an extra layer of protection.
- Silk Road transactions were made with Bitcoin, so it was necessary to exchange cash into Silk Road Bitcoin before purchasing anything — like exchanging cash for tokens at an arcade.
DNeT bulletins providing details on trends in darknet markets over time are available at the Drug Trends website, with the next bulletin due for publication at the end of March 2016. Dark marketplaces Agora, AlphaBay, Dream Market, and Hydra replaced Silk Road and Silk Road 2.0, although all are now defunct. Some current darknet marketplaces include ASAP market, Archetyp, and Incognito, but many former dark web marketplaces have gone mobile on encrypted secure messaging apps like Telegram.
To help facilitate the smart contract development process, Ride uses three main types of scripts to create different types of smart contracts including dApp scripts, account scripts, and asset scripts. Journalists use the dark web to help protect the anonymity of their agora darknet market sources, and others use the dark web simply because they believe strongly in their right to privacy. For our analysis of dark markets, our data was provided by Chainalysis 40, which is a blockchain analytics company.

The First Dark Web Market: The Silk Road Website
Administrators of the biggest current dark web market have announced the site will be temporarily closed, claiming that recent research suggests the server locations of Tor hidden services could be discovered. If true, this could risk revealing sensitive information about the site and its owners. Berg suggested, other managers of agora darknet market the site who might soon be arrested. The Silk Road website was an anonymous internet marketplace active from January 2011 to October 2013. Accessible through encrypted dark web browsers such as Tor, Silk Road was known as a hotbed of illegal activity facilitated by cryptocurrency, and served as one of the initial use cases for Bitcoin.

Search Code, Repositories, Users, Issues, Pull Requests
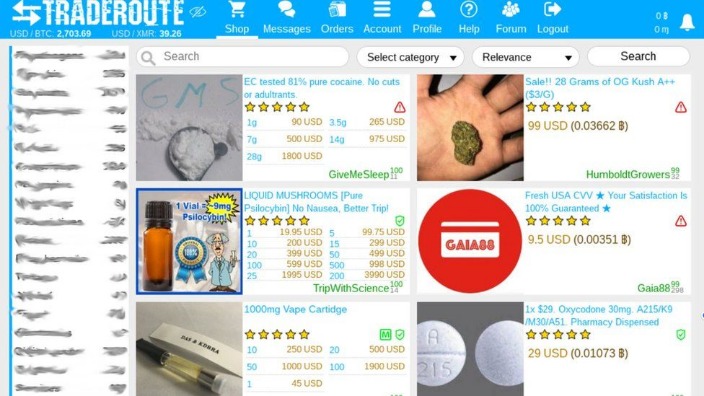
Empire Market, where people can buy and sell drugs, Empire Market was the most-trafficked dark web marketplace, Bloomberg reported. This project investigates the darknet marketplace industry. Specifically, it explores the items sold on such marketplaces, the currency used, the buyer-seller relationship, the impact on organized crime and the impact on drug-related violence. Additionally, it explores the potential uses of such data for understanding and regulating illicit drug markets.
Top Darknet Markets
Looks like some of my client’s info has been stolen. Due to this critical use of data, rigorous investigation and avoidance of false positives is crucial. Good threat intelligence helps to monitor both intentional and inadvertent use of corporate brands so that these brands can be protected. The spam messages sometimes contain phishing links to popular sites like LinkedIn and Baidu.
This visual provides a general overview of the scope of the demand and supply for products on Agora as the size of the category name corresponds to the percentage of total postings related to that product. Below each category name is a percentage value to give readers more of useful information. The second visual, the table, compares the types of weapons sold on Agora, ranging from the most common – handguns – to the least common – explosives, including weapons like tasers, shotguns, machine guns, and poisonous substances. A large chunk of the market for firearms consists of “custom orders,” in which the item name and description are hidden. This shows that even on the dark web, users prefer to be as vague as possible and appreciate privacy even for the sale of illicit activities.
Safe Darknet Markets
We provide you with news, links,markets and reviews from the dark web. We are committed to providingupdated, quality and reliable information. This prosecution is part of an Organized Crime Drug Enforcement Task Forces (OCDETF) investigation. Hydra also featured numerous vendors selling false identification documents. Users could search for vendors selling their desired type of identification document – for example, U.S. passports or drivers’ licenses – and filter or sort by the item’s price. Many vendors of false identification documents offered to customize the documents based on photographs or other information provided by the buyers.
Nightmare Market is a darknet market that exit scammed darknet wallstreet market taking all user’s funds and doxxed their admin who supposedly stole all the funds that were on the market. In doing so, Pavlov is alleged to have facilitated Hydra’s activities and allowed Hydra to reap commissions worth millions of dollars generated from the illicit sales conducted through the site. Hydra vendors also offered a robust array of money laundering and so-called “cash-out” services, which allowed Hydra users to convert their bitcoin (BTC) into a variety of forms of currency supported by Hydra’s wide array of vendors. In addition, Hydra offered an in-house mixing service to launder and then process vendors’ withdrawals.



