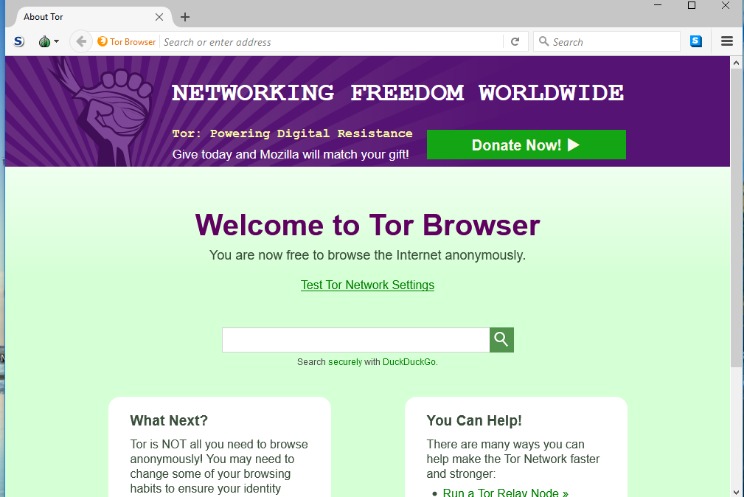
(Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now).
Search Engines
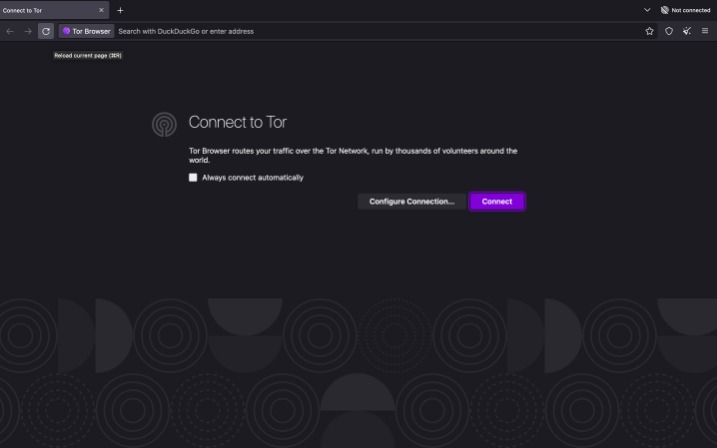
With dangers like this in mind, it’s even more important to stay safe when surfing the Dark Web than any other part of the internet. A common misconception about the internet is that, once you open google, you can access anything and everything available online. In fact, only about 5-10% of the information on the internet is available through common browsers like Google Chrome or Mozilla Firefox, known as the ‘surface web’. It will normally take a while to connect because Tor — unlike other browsers — will route your traffic through different nodes. You should also keep in mind that overall speeds will likely be impacted; for example, a page might take a few seconds longer to load than what you are used to. If you want to access the Tor network on your iPhone or iPad, you can use the Onion Browser app.
ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism. With your VPN active and Tor installed, you’re now ready to connect. This is an extra precaution that can protect your device from savvy hackers looking for any opening that presents itself. Once you’ve chosen a VPN provider and have successfully set up your account, you’re ready to start looking at overlay networks.
Is Tor Completely Anonymous?
Once the download is complete, locate the downloaded file and initiate the installation process. Follow the on-screen instructions to install the Tor Browser on your device. The installation process is straightforward and generally similar to installing any other software.
From there, it will go through a VPN server that conceals your IP and wipes geo-locations tags and other elements your Government or ISP might use to track the request.
More Ways To Stay Safe On The Dark Web
Bitcoin allows for anonymous donations, making it easier for terrorists to fund their activities and purchase weaponry. In some cases, fraudulent websites claim to be used by terrorist organizations such as ISIL. With the current technology, cyber terrorists can exploit their weaknesses to carry out attacks. The story hints at why taking dark web safety measures is essential, even if you are jumping into the dark side of the internet only because of some curiosity. It hosted over 7,000 .onion categorized links to make surfing the web easier. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online.
Best VPNs To Access The Dark Web Safely
That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls.
Tor And Onion Routing Explained
Explore this FAQ section to get answers to some common queries about this hidden part of the internet. Secure your online accounts with unique, strong passwords that are difficult to crack, such as a combination of uppercase and lowercase letters along with numbers and special symbols. Carefully matching your needs to the strengths and weaknesses of each solution ensures optimal privacy, security, and usability.
She holds a Bachelor’s degree in Liberal Arts and a triple Master’s degree in Literary and Cultural Studies. Outside of work, she is a travel enthusiast, music lover and avid learner interested in global cultures, spirituality, psychology and neuroscience. If you need a way to organize as an activist or you want to discuss censored topics with others, my first suggestion is to stick to offline meetups. The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. Signal is our Editors’ Choice for private messaging apps because it does a great job of blending privacy and social media functionality for a highly customizable chat experience.
Legitimate Use Cases For The Average User
Some consider it an outright necessity, as it helps encourage free speech, maintain a free press, and support the work of law enforcement and government agencies. The dark web is full of unknown and potentially dangerous content. Clicking on links there might take you to illegal or harmful material without warning. You should never trust websites and forums on the dark web with your personal information. You can check our guide on the best VPN services to find the right VPN solution to protect your privacy. Though the dark web offers anonymity for journalists and activists in oppressive regimes, it raises many ethical concerns.
There’s plenty of illegal content, products, and services available on the dark web. Anonymity doesn’t make carrying out illegal acts any more permissible, so be cautious about making purchases or downloading content. However, the line is drawn at what you’re doing once you’re on the dark web. Engaging in illegal activities—like buying drugs, trafficking stolen data, or distributing harmful content—is absolutely against the law. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. The subreddit r/deepweb is a good starting point for asking more experienced users about how to search the dark web and deep web for the content you want.
Browse Privately
Think of your email inbox, banking dashboard, cloud documents, subscription content, or internal business tools. The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines.
More Computing Guides
- Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
- However, it is crucial to recognize the dual nature of the Dark Web, understanding that while it has legitimate uses, it also harbors risks and associations with unlawful activities.
- Corporations and governing bodies alike currently participate in unauthorized surveillance of online activity.
- Onion URLs generally contain a string of seemingly random letters and numbers.
To reduce the risk of these threats, it’s highly recommended to disable JavaScript when browsing dark web sites. Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy. I2P is a private network built for secure, anonymous communication. Instead of the onion routing Tor uses, I2P relies on unidirectional tunnels and garlic routing, which bundles multiple messages together for better traffic obfuscation. It uses its own internal DNS to access “eepsites”, not .onion addresses. Tor protects your identity inside its network, but it doesn’t hide everything.
- There are multiple search engines on the dark web that can help you find what you’re looking for.
- This article lists some of the best dark web websites you can visit securely.
- The Dark Web refers to hidden websites that aren’t indexed by regular search engines like Google or Bing.
- Firstly, it is crucial to have a legitimate reason for accessing the dark web to avoid unnecessary risks.
- Accessing blocked content can result in being placed on a watch list or imprisonment.
- A lot of illegal activity takes place on the dark web, and engaging in any of that activity can be a criminal offense.
Its deep insights into cybercrime forums, compromised card databases, and exposed assets give security teams a critical edge. Accessing the Dark Web requires cautious navigation, and adhering to certain tips can help ensure a safer and more secure experience. What should you do if your information is found in a data breach or you think it’s been leaked somewhere? Change your passwords and watch out for suspicious activity on your credit reports. Dark web marketplaces offer a range of both legal and illicit goods. Here’s a look at several of the illegal items you can buy — with prices — courtesy of Privacy Affairs’s Dark Web Price Index 2023.
Stolen information from data breaches, drugs, guns, malware and various other illegal items can be bought there. Check out our article on the dark side of the dark web for more information about the dangers of the darknet. The Tor Browser is an open-source web browser created for anonymous browsing and to evade censorship. It routes users’ traffic through thousands of volunteer-run servers called nodes/relays.



