Most URLs on the dark web have unrecognizable names, so it’s easy to fall for this trap — putting your private files, financial data, keystrokes, and other personal information at risk. Social engineering tactics are also common, where bad actors try to get you to willingly give up sensitive information, like login details, financial information, etc. The dark web is the home of many criminal activities — from the use of stolen or fake documents to drug and weapon dealing.
Top 13 Dark Web Forums Of 2025 To Monitor
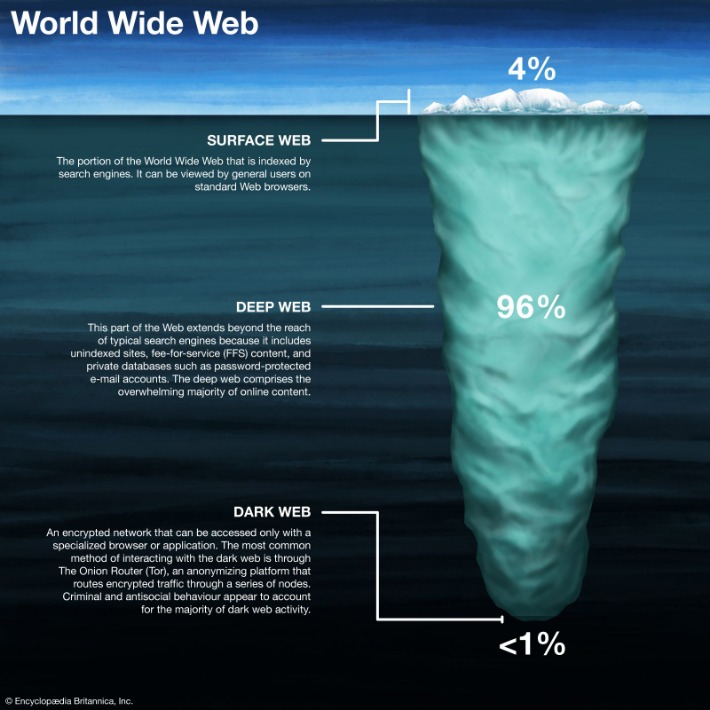
It’s simply a hidden part of the internet that you can reach using special tools like the Tor Browser. People use it for different reasons, such as privacy, research, or even reading the news in places with strict censorship. Simply isiting a .onion site isn’t considered a crime in most countries.

VPN Over Tor (Not The Best Option)
Even if they aren’t actively malicious, they might still have weak security or expose you to threats. Additionally, make sure that you only download the Tor Browser from the official website. While the dark web comes with risks, it’s possible to explore safely if you take the right precautions. By following some basic security tips and using the right tools, you can greatly reduce your chances of running into trouble. If you come across suspicious links, you should avoid clicking on them.
The urban legend of ‘Red Rooms’ that features live murders has been debunked as a hoax. Some websites monitor and analyze the dark web for threat intelligence. The story hints at why taking dark web safety measures is essential, even if you are jumping into the dark side of the internet only because of some curiosity. The information can be of any kind, either social security numbers or even bank card numbers (the bank/credit card information is usually sold in bulk).
- Though the intention and purpose of users on the dark web may vary, the dark web itself is neither good nor bad.
- Navigating the dark web can be like exploring a labyrinth — there are hidden treasures but also potential traps.
- These browsers offer the best security and privacy for browsing the dark web on mobile devices.
- Accessing the dark web is legal in India as long as you do not engage in illegal activities such as buying drugs or hacking services.
- Using a different browser than these could put your privacy at serious risk and could expose you to attacks from cybercriminals.
It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. It will offer you an additional layer of encryption to access the deep parts of the internet. The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article).
While the dark web itself isn’t illegal, several laws come into play depending on what’s being done. Choosing a dark web monitoring tool requires a lot of factors, including price, availability, and many other things. However, effectiveness comes down to how well the tool aligns with your risk profile and operational needs. These platforms sell counterfeit or forged documents, including passports, IDs, driver’s licenses, and other official papers.
Popular Posts
- As you might expect, these websites sometimes host explicit, gory, harmful, and illegal content.
- Underneath it are deeper layers that aren’t visible through normal browsing.
- This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites.
- In a similar vein, I was an early adopter of many social media platforms, but now I’m just an infrequent Reddit lurker.
- It is important to note that even browsing the dark web can be risky, as there is a high risk of encountering malicious content, scams, and other dangers.
With all this data, your ISP could create a very accurate profile of you and link it to your IP address. This is one of the reasons why it is always good to hide your IP address. Your Internet service provider, or ISP, is your gateway to the Internet. As much as the Darknet contains even the “good” stuff, it’s not a place you need to stumble about blindly without proper dark web safety. Reports of hitmen for hire and crowdfunded assassinations on the dark web are believed to be hoaxes.
Marketplaces For Everything Illegal
The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. Signal is our Editors’ Choice for private messaging apps because it does a great job of blending privacy and social media functionality for a highly customizable chat experience.
Caution: Safety Comes First When Visiting Dark Web Links
Stay vigilant, trust your instincts, verify sources, and prioritize your security to make the most of the anonymity these networks provide. Now that you understand the essentials of anonymous networks and how to prepare yourself for secure browsing, it’s time to explore the practical steps involved in accessing the Dark Web. While the process is not overly complicated, it demands attention to detail, adherence to best practices, and an understanding of the risks. Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network.
Is The Dark Web Truly Safe?
We already went through VPNs, anonymizing web browsers, and disposable operating systems, so I won’t bother reminding you about those. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect. You can also take a look at the blogs & essays section if you want to find some nifty coding resources.
Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online. So not only is your web activity hidden, but you can mask your IP address by connecting via a wide range of global VPN server locations. For more advanced use, Hyphanet allows you to create and host your own freesites, participate in forums, and communicate anonymously with other users.
Table Of Contents
For a number of technical reasons, it’s much faster and more reliable than Tor. The peer-to-peer routing structure is more advanced, and it does not rely on a trusted directory to get route information. I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. Due to all the nodes that your traffic passes through, Tor by itself significantly limits bandwidth. Adding a VPN to it, even a fast one like IPVanish will make it even slower, so please be patient. Another vital precaution is to ensure that your .onion URLs are correct.
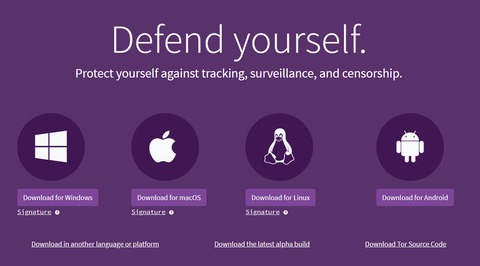
Step 3: Connect To The Tor Network

Darknet markets facilitate transactions for illegal goods and services. Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources. While many dark marketplaces have been shut down by authorities, new ones soon appear in their place.
Is The Dark Web Used For Illegal Purposes?
Setting up Tor correctly is critical if you want to browse the dark web without exposing your real identity. A single misstep, like skipping a leak test or using the wrong browser, can undo all your privacy efforts. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links.
If something bad happens in one box, such as a website trying to drop malware, it’s contained there. My old laptop wasn’t gonna cut it, so I had to commandeer my husband’s PC to test it out. Malware, ransomware, and hacking tools are widely sold in underground forums. Learn how CrowdStrike can help protect your brand and data with CrowdStrike Falcon® Adversary Intelligence. The 2024 Global Threat Report unveils an alarming rise in covert activity and a cyber threat landscape dominated by stealth.



