However, HTTP on its own isn’t secure– it doesn’t encrypt data during transmission, which leaves an opening for third parties to spy on your online activities. With your Tor connection established, you can begin surfing the web with the utmost privacy. Like standard browsers, Tor has an address bar where you’ll type the domain you want to visit. Open the downloaded file on your device to begin the installation process. The process is similar to installing any other software – follow the on-screen instructions and wait for the installation to complete.
Step 6: Access The Tor Browser On Tails OS

For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. These settings can be found in the Router Console’s configuration panel. I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing.
- It’s a place where anonymity reigns, and while it has its shadowy corners, it is also home to various forums and communities.
- Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked.
- You can choose 256-bit for maximum protection or 128-bit if you want a faster connection.
- As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with.
How To Get On The Dark Web On Tor Browser
It’s impossible to access the dark web with a regular browser like Chrome or Safari. So, to get into the Tor network, follow the steps I’ve listed below. The majority of the users on the dark web use the Tor (The Onion Router) browser.
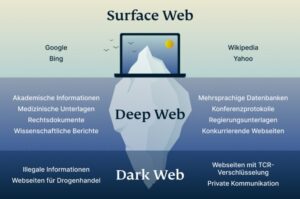
Tor works by routing your traffic through multiple encrypted servers, masking your location, and making it much harder to track your online activity. The dark web is a hidden part of the internet that requires tools like Tor to access. To protect your security, always use a VPN like NymVPN, disable tracking features, and follow safe browsing practices. To properly peel back the internet’s layers, you need a tool that provides layers of encryption to hide your activity. Those layers of encryption and routing activity help to anonymize your movements.
Navigating Dark Web Directories Safely
Simply download the file, install the software, and you’re ready to use its web-based interface. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. I2P can only be used to access hidden sites that are only available on the I2P network. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites.
The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content. Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online. So not only is your web activity hidden, but you can mask your IP address by connecting via a wide range of global VPN server locations. By using a VPN to connect to Tor — a special browser designed to access the dark web — you can securely access the dark web using a technique known as Tor-over-VPN.
Roundup – Best VPNs For Speed
However, before you start your search, toggle the button beside “Onionize” to anonymize your session. This hides your activity and personal identifiers so you can browse safely, protected from prying eyes and identity theft. In the internet’s darkest corners, a myriad of hidden websites cater to an array of needs and interests. From encrypted communication channels and hacking forums to illicit marketplaces, the dark web is a destination for millions of daily users. Read on to learn more about the five main types of darknet websites and what they contain. Get Norton VPN today to start browsing the web more freely and anonymously.
Remain Careful Of Your Browsing Habits
If you’re an iPhone user and curious about accessing the Dark Web, you’re in luck. With the right tools and precautions, you can explore this hidden realm directly from your iPhone. The dark web is a common gathering place for hackers and other cybercriminals, which can make browsing the dark web a risky activity. Visitors to the dark web should exercise extreme caution when downloading files, as they may infect your devices with viruses, malware, trojans, ransomware, or other malicious files. At a minimum, users should ensure that their cybersecurity defenses are activated and up to date.
Even in an era of increased online surveillance, the average person on the internet likely has too much to lose to bet on their safety for curiosity’s sake. Heck, I’m one of PCMag’s resident security experts, and I’m not playing around on the dark web just because I know how to. That’s why I’m not going to provide links or detailed instructions for accessing the internet’s shadier side. The dark web isn’t something you can just stumble upon, and that’s a good thing. Sites on the dark web can contain potentially catastrophic pitfalls in the form of illegal activity, phishing links, financial scams, and malware infections. There’s also little to no recourse to be had if you encounter any trouble there, because the dark web is a decentralized collection of websites hidden from search engines.

Cyble Partner Network (CPN) Join Us
By familiarizing yourself with these networks and protocols, you gain a clearer understanding of the diverse strategies people use to stay hidden online. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web.
Step 2: Download And Verify The Tails OS Image
All Surfshark servers are RAM-only and support the WireGuard, IKEv2, and OpenVPN protocols. The company operates a strict no-logs policy and protects internet traffic using AES-256-GCM encryption together with a SHA512 authentication hash and 2048-bit DHE-RSA key exchange. While NordVPN is undoubtedly a great service, it’s not without fault. In 2018, someone gained access to a third-party data center in Finland. NordVPN responded aggressively by upgrading its entire infrastructure to RAM-only servers and ending its reliance on rented servers.
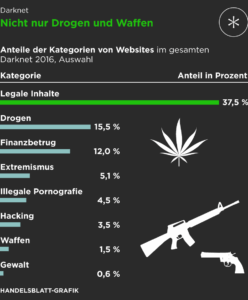
It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses. Accessing the Dark Web in The Sims 4 can be a fascinating experience, but it’s essential to remember that it’s a virtual representation of real-life illegal activities.
- But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network.
- We can conclude that this portion of the internet can be dangerous but again, you’re in control and decide which websites you want to visit.
- This allows you to get an overview of what is on offer, and to find onion sites depending on your needs.
- He holds a bachelor of arts degree from the University of Washington and is now based in Boston, Massachusetts.
- Take a look at the sites that these directories have collected and see what topics interest you.
ExpressVPN’s intuitive apps work on up to 8 devices at a time, ensuring protection for the entire family. You’ll appreciate its added features, such as Threat Protection, which shields you from malware and trackers. NordVPN also includes Double VPN servers to double your encryption and make you untraceable. One of its key benefits is unlimited bandwidth, which sounds awesome and allows for unlimited dark web browsing.
Tips For Using The Dark Web Safely
Whether you’re curious about exploring its depths or looking to access legitimate resources, we’ll show you how to navigate the Dark Web safely and responsibly. Once a user installs a dark web browser on a device, it functions like a regular browser. That said, it can be difficult for users to find the material they are looking for on the dark web. Addresses tend to be a mix of random numbers and letters, making them challenging to remember or access manually.