ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. Also, use an effective antivirus program to check threats if you decide to download files.

Download Tor Browser
Besides this, ensure that services like remote desktop or file-sharing that are easy to exploit are disabled and check that your webcam is covered. This makes it really appealing for those who want to avoid unnecessary surveillance or who need to communicate without fear of oppression or governmental retaliation. However, if you’re planning to spend any time exploring the dark web, it’s crucial you take the necessary precautions to keep your device, your data, and yourself safe.

A Drink With A Stranger (Ghost Of Yotei) — Detailed Quest Guide
But the so-called “visible” Internet (aka surface web or open web) — sites that can be found using search engines like Google and Yahoo — is just the tip of the iceberg. The dark web is just the name for all of the Tor hidden services on the internet, including websites with .onion URLs that can only be accessed with the Tor Browser. Many of the sites on the dark web are perfectly legal and legitimate. The deep web is everything on the internet that isn’t indexed by search engines. PrivateVPN’s security and privacy features include a kill switch, and an Application Guard — which will disconnect named apps if the VPN connection fails.
The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. Other sites explicitly block search engines from identifying them.
However, remaining anonymous can be invaluable to protesters, civil rights groups, journalists, lawyers, and other vulnerable groups. Illegal marketplaces are merely a small fraction of what’s actually there. When the dark web is mentioned online, it is usually in tandem with criminal marketplaces and arrests made by law enforcement agencies.
- These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information.
- Microsoft Word is one of the best word processors around, allowing you to craft powerful documents with an intuitive interface.
- KEY TAKEAWAYS Tor is one of the most popular private browsers in the industry.
- We’ve also looked at how Tor allows users to access the dark web, and we’re now aware of the resources and dangers that await us there.
- Illegal cyber activity cannot necessarily be stumbled upon easily but tends to be much more extreme and threatening if you do seek it out.
Step 6: Advanced Hyphanet Features (Optional)
Upgrade your lifestyleDigital Trends helps readers keep tabs on the fast-paced world of tech with all the latest news, fun product reviews, insightful editorials, and one-of-a-kind sneak peeks. Keeping your VPN and Tor Browser updated ensures you benefit from the latest security patches. Outdated software can have vulnerabilities that may put you at risk. Files on the dark web may contain malware, and it’s best to avoid downloading from unknown sources. Lifehacker has been a go-to source of tech help and life advice since 2005.
Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for.
How To Browse The Dark Web
Corporations and governing bodies alike currently participate in unauthorized surveillance of online activity. Some simply don’t want government agencies or even Internet Service Providers (ISPs) to know what they’re looking at online, while others have little choice. Users in countries with strict access and user laws are often prevented from accessing even public sites unless they use Tor clients and virtual private networks (VPNs). Dark web sites use encryption software so their visitors and owners can remain anonymous—it’s why the dark web is home to so much illegal activity.

Google Warns About 97 Zero-Day Vulnerabilities Exploited In 2024
The best thing is to actually understand how to find the fresh, new links. This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. The social media giant is also aware of the many attempts by repressive regimes to restrict its access.
This prevents cyber criminals prowling the dark web from snooping on your activity. Therefore, to access the deep web, you need passwords to those databases. If you are a journalist or whistleblower and want to access the dark net for legal purposes, this guide is for you. We have covered some in-depth and tested steps to use it safely. Accessing the dark web sites isn’t safe and requires a user to go through several privacy measures to access it anonymously.
Final Thoughts On Staying Safe On The Dark Web
Originally used by the United States Department of Defense for anonymous communication, the dark web is now a place for those wishing to stay anonymous themselves. To say the least, DOT Security does not recommend going to the dark web unless absolutely necessary. However, if you’re going to venture into the dark web, you’ll need to be well–prepared, so keep reading to keep safe.
And though some dark web marketplaces offer user reviews, not all do. Lack of regulation by authorities or other users makes it easy for cybercriminals to carry out scams. The Hidden Wiki is a surface website offering a collection of dark web links.
Tor is a powerful tool that enables you to browse the internet anonymously by routing your connection through a network of volunteer-operated servers. The dark web is the part of the internet that isn’t indexed by search engines like Google or Bing. You can read about it on Google, but you can’t actually visit dark web sites with regular browsers like Chrome. Here’s a guide that will help you learn about the dark web, the sites that populate it, and how you can visit it safely using the added protection of a VPN and antivirus software. Norton 360 Deluxe provides a comprehensive suite of protection that can help block malware and dangerous links in real time, and even detect scams using cutting-edge AI detection.
The final relay before your traffic goes to the destination website is known as the exit node. The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions.
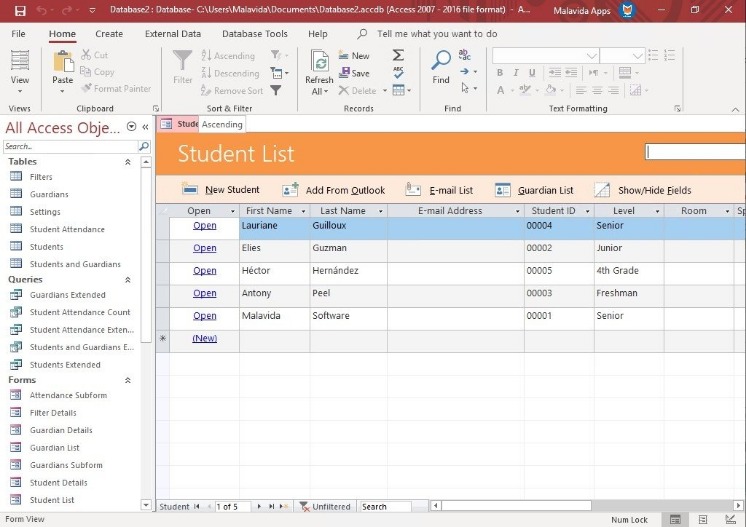
When you install the Tor Browser, it comes preconfigured with the most secure privacy settings. That means Javascript is disabled, extensions are disabled, and the browser is configured to warn you if an attempt is made to download a file and open it in another application. Turn on your VPN and launch the Tor browser and it will automatically connect to the Tor network from which you can access the Dark Web anonymously. On the Dark Web, you will not find search results indexed by Google, which can make it difficult to find what you are searching for. The Tor browser is completely free to use and is available for most major platforms, including Windows, Linux, macOS, and Android. You simply need to download it for the platform you use and install it on your system.
Use A Dedicated Device Or Virtual Machine
You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays.