
Lastly, we emphasize the importance of due diligence and informed decision-making when engaging with the underground gun market. Our experienced team is always available to provide expert advice, answer your questions, and guide you through the process. By staying informed and cautious, you can successfully navigate the underground gun market and find the perfect firearm to meet your needs. From compact models ideal for concealed carry to full-sized handguns suitable for home defense, our collection covers it all. We prioritize quality and reliability, ensuring that each firearm meets stringent standards before it’s made available for purchase. Some popular brands in our inventory include Glock, Smith & Wesson, Sig Sauer, and Beretta.
- In addition to the brief introduction of “fake” marketplaces on the dark web, dark web users visiting political sites on the Tor network should realize that government-funded cyber teams are on the lookout for such users.
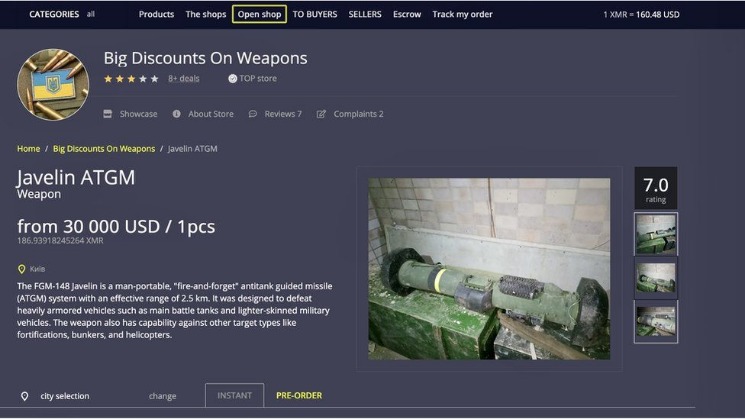
- There has been a steady increase in the availability of goods and services offered in the black markets.
- The Dark Web is only a small part of the Deep Web, with a more focused purpose.
- But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network.
- It uses TrustedServer technology on the entire server network to wipe out your data after every session.
Underground Website Used For Black Market Drug Sales Bigger Than The Original, Report Says
It supports operations in multiple languages and operates on both clearnet and Tor. For businesses and individuals alike, understanding these threats is the first step in securing their digital assets. However, combating dark web risks requires more than just awareness—it demands proactive and comprehensive protection. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.
How ICE Enforces Immigration Laws
It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Norton 360 Deluxe provides a comprehensive suite of protection that can help block malware and dangerous links in real time, and even detect scams using cutting-edge AI detection. Plus, it features a built-in VPN to encrypt your connection, hiding your IP address and online activity, for more anonymous and private browsing. The existence of black markets serves as an example of a larger debate over whether governments should attempt to legislate morality. Libertarians have argued that the only purpose of the government is to guarantee private property.
Topics And Products Sold

In this article, we explore the evolution of the digital black market. We first explore how the concept of currency evolved into a digital, anonymous form – a critical component of the modern vulnerabilities and illicit goods black market. Those risks were mitigated with cryptocurrencies, but we explore how even the new, supposedly anonymous cryptocurrency solution is not without risk or incredible insecurity, either. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details. These platforms continuously scour the deep and dark web, looking for any traces of your sensitive information.

What Are Ransomware Leak Sites
Band shirts have long been more than just merchandise; they are symbols of musical allegiance, cultural movements, and personal identity. However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered. Always tread carefully whenever crowdsourcing information on how to navigate the dark web. For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated. RussianMarket specializes in the sale of “logs”, CVVs, dumps and RDP access.
Chrome Security Update Addressing 21 Vulnerabilities
The digital monetary system online is predominately operated by the likes of Paypal, Western Union, and banking companies that try to follow government regulations to prevent fraud and money laundering. There are two steps to legally take money and have it converted at the current Bitcoin rate into BTCs in our digital and anonymous bank. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack. Dark web markets are home to a billion-dollar industry dealing in illicit goods.
What Is The Dark Web? How To Access It And What You’ll Find
Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. Those who access the dark web do so via the Tor (The Onion Router) browser.
Still, he said, attitudes towards the black market sites have changed somewhat, though not so much because of Ulbricht’s arrest or the threat of another law enforcement crack down. In the time since the FBI shut down the original Silk Road site there have been a number of instances where people were scammed into sending money for drugs, only to see the website disappear with the buyer’s money. The general volatility of darknet markets has led to calls for further decentralization of transactions to protect both buyers and vendors. If cryptocurrency is held in a customer account on a darknet platform, it’s always at risk if a site shuts down. Silk Road operated via a hidden darknet feature in the anonymous Tor network.
Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. You can choose the best darknet (.onion) website that suits you and start surfing.
- The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo.
- Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more.
- The stolen data included names, contact information, and order histories.
- Hidden Tor Servers are now the norm for storing, accessing and hiding illicit activity such as child pornography.
- The Silk Road website was a Tor hidden service, which made it difficult for the authorities to shut the site down.
Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web. Estimates place the size of the deep web at between 96% and 99% of the internet. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”. The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google. Deep web content includes anything behind a paywall or requires sign-in credentials.
However, some surface web platforms like ProtonMail offer encrypted email services in addition to dark web versions that enable people residing in more repressive areas to communicate freely. The political and ideological aspect finds itself far more prevalent in the fast-moving pace of chat environments and significantly less strong or abrasive in easier moderated communities such as web forums. These, too, find themselves hidden behind .onion domains accessible only via TOR-enabled web browsers.

Once you have Bitcoin in your wallet, you can proceed to our website and select the firearm you wish to purchase. At checkout, choose Bitcoin as your payment option, and you’ll be provided with a unique address to send the payment. After the transaction is verified, your order will be processed and shipped discreetly to your location.
Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. Impreza Hosting is a service that helps you host a site on the Tor network. It provides an .onion URL and an interface for you to manage your Tor site easily.
Conclusion: Safeguard Your Brand Against Dark Web Threats
Before your data reaches a site, Tor encrypts your connection and redirects it through a series of servers called “nodes” or “relays” to replace your IP address with each server’s address until it reaches the website. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely. Although it offers leaks from many different countries, the site has a dedicated lookup and leak section for Canadian profiles, making it extremely easy to use for buyers interested in Canadian leaks.



