Now, places like ASAP are talking decentralized setups, spreading the load across nodes so they’re harder to shut down. I’ve seen some beta versions popping up on forums, and they’re rough but promising. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages.
It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. All resources are offered to give insight into the workings of the Tor network and darknet markets. Use at your own discretion and always remain within the laws of your jurisdiction. Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser.
- All resources are offered to give insight into the workings of the Tor network and darknet markets.
- Dark web domains are generated in a cryptographically secure way, so they look like random strings of 16 characters or more (like 3g2upl4pq6kufc4m.onion, for example).
- These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
- For example, there are separate categories for blogs, email services, file uploaders, forums, and more.
- Moreover, if you must use public Wi-Fi, ensure that you use a VPN to mask your browsing activity and keep yourself secure.
(NOT) Lost In Translation – Why Your Language Doesn’t Matter To Cybercriminals
DuckDuckGo is a search engine available on the Tor network that lets you browse the surface and dark web. Essentially, it’s a search engine like Google or Safari, but unlike other search engines, it doesn’t track your browsing activity or collect user data. So, search results won’t be based on your browsing history, location, or anything else. And I liked that if I visited a site that had a .onion version, it prompted me to switch to that version. Using a dark web search engine is a great step towards enjoying a more secure experience while shopping on the platform.
Roundup – Best VPNs For The Dark Web

The use of digital signatures can also help verify the authenticity of users and transactions. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. This browser enables access to websites with .onion domain extensions, which are specific to the Tor network. These addresses cannot be resolved by conventional DNS servers, contributing to the hidden nature of darknets. Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps. Always transfer your cryptocurrency to a personal wallet under your control before making purchases on darknet markets.

Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. A VPN encrypts the data traffic and keeps your activities private on the dark web. It also masks your IP address, making it difficult for government agencies to monitor or track your activities. We recommend using NordVPN as it offers top-notch security features, including dark web threat protection. Dark web search engines support dark web marketplaces and allow users to use them, but still accessing them is full of risks; they can infect your device with malware or viruses, and can bring other legal consequences. Therefore, you must know how to access dark web marketplaces safely (covered later in this article).
- In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization.
- When in a public place or any location where you doubt the network’s safety, employ a virtual private network (VPN) to encrypt all communication.
- It is a place where citizens can provide whistleblower information in a secure, private, and anonymous manner.
- The deep web consists of all parts of the web that aren’t indexed by standard search engines like Google.
- Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers.
The Hidden Wiki
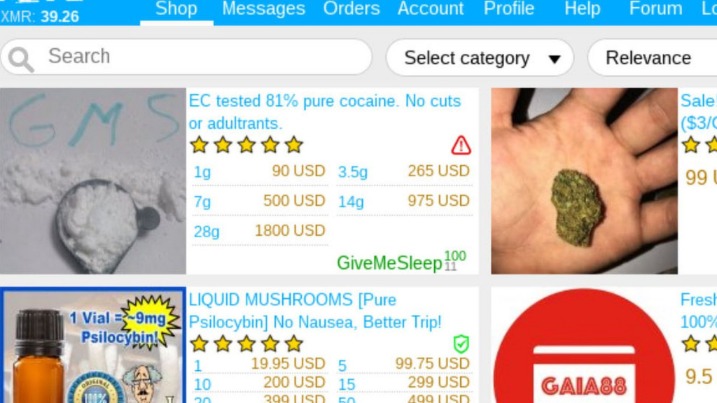
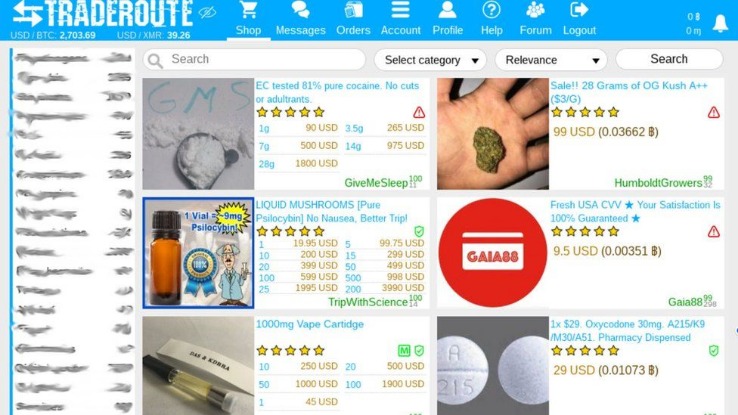
The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero. Here’s a look at the top 10 dark web markets currently dominating this underground space. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI.
What Is Tor?
“They do not curtail the collection of your online activity by your ISP, advertisers, and trackers. They don’t prevent someone monitoring your network from seeing what websites you’re visiting. Tor Browser does.” Torrez has been steady since 2020, rocking 4,650+ listings with BTC, LTC, ZCash, and Monero. Wallet-less payments and multi-signature deals make it a safe bet—I’ve never worried about getting burned, even after a close call with a dodgy vendor once.
The dark web is not a place that you can venture into without protection and caution; a slight slip-up can lead to major consequences. Perhaps, the lack of rules and anonymity of the dark web can be tempting, but those are the same things that make it a risky environment. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud.
The Best Dark Web Search Engines In 2024
As in the previous 3 years, we conducted research into the supply and prices of various goods and services sold by cybercriminals on the dark web. SecureDrop uses Tor to provide a safe way for whistleblowers to contact various news outlets. Prominent organizations like The Guardian, The New York Times, and ProPublica have implemented it. The software requires two-factor authentication to receive what’s been uploaded by the whistleblower and allows two-way communication between the anonymous contact and the media outlet. The Imperial Library of Trantor is a library of thousands of PDF and EPUB books that you can download for free, and many students find this an invaluable trove of information that they otherwise wouldn’t be able to access.
What Is WPA2 (Wireless Protected Access ?
During the second half of 2022, law enforcement cracked down on a large number of darknet markets, temporarily disrupting the supply of such illicit goods. Most dark web marketplaces use cryptocurrencies like Bitcoin for transactions to help maintain anonymity. Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought. DuckDuckGo is built into the Tor browser, making it a convenient option for looking up dark web websites. However, before you start your search, toggle the button beside “Onionize” to anonymize your session.
Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet. While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional. New darknet sites and markets continuously emerge to replace those that get shut down.
Hidden Services
Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous. It’s one of the largest darknet markets that launched in 2022 and trades sensitive financial credential transactions. It’s the place where you can buy or sell stolen credit card numbers, SSH login credentials, and personally identifiable information (PII).
Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware. Thus, use the best antivirus software that protects against these online threats. This guide outlines different ways of safely accessing dark web stores and the list of reliable dark web marketplaces you can consider visiting in 2025 for research and monitoring purposes.