The Deep Web consists of countless legitimate applications, such as research or retrieval of personal medical records, or corporate management of data. Researchers generally use databases like JSTOR for articles, while healthcare providers maintain private information regarding patients in secure systems. Many organizations employ the Deep Web for secure data storage and communication. In this way, the Deep Web is a constituent part of today’s Internet usage.
Why Are All Dark Websites In The onion Top-Level Domain ?
Deep web communication tools offer encrypted and anonymous channels for messaging, file sharing, and collaboration, enhancing privacy and security for users. This information about the implication of accessing not only the deep web but also the dark web empowers the person to make responsible decisions and fathom the complexity of internet interaction. In the end, this is advantageous because one does not risk increasing personal safety or ethical integrity in this increasingly digital world.

While the mere use of the deep web is not illegal, certain activities, such as accessing or distributing copyrighted materials or illegal content, can lead to legal problems. It is therefore important to familiarize yourself with the laws and regulations that apply to the deep web and to comply with them. Cyber criminals are increasingly and persistently targeting the financial services sector, particularly banking institutions, using the dark web, according to a new report by Searchlight Cyber. Silobreaker helps security teams stay ahead of threats – whether they originate from a mainstream news report, a leaked credential dump or a covert dark web marketplace.
Is It Legal To Browse The Dark Web?
These schemes have real financial consequences – airline miles, hotel stays, and high-value retail goods can all be cashed out. Another example, AppLite, an Android banking Trojan, has spread through fake job offers and phishing sites, leading to full device compromise. By comparing its techniques with past threats, defenders can identify recurring vulnerabilities, prioritize patching and refine incident response plans. Most ransomware gangs have a presence in the dark web today, where they announce their attacks.
A Beginner’s Guide To The Dark Web And Online Anonymity
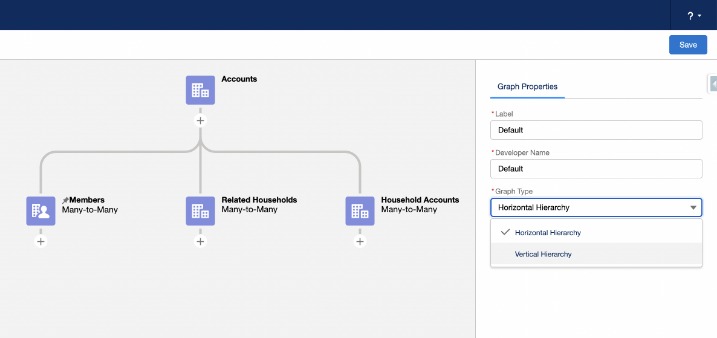
- The part that we are most familiar with is really just what we might think of as the surface web.
- Explore this research report on Grocery Pricing Data Intelligence in USA, comparing weekly and daily insights to track trends, optimize pricing, and drive decisions.
- You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers.
- Recent high-profile attacks on business leaders have pushed executive protection into the spotlight.
This is the part of the Internet that is visible to search engines like Google and accessible via normal web browsers. The Gray Web is referred to the part of the Surface Web where fraudsters discuss or research their activities. However, the Surface Web represents only the tip of the iceberg when it comes to the internet – the majority of it is actually hidden. While the anonymity provided by deep internet searches can be beneficial for protecting privacy and free speech, it also creates a breeding ground for malicious actors to operate without fear of repercussions.
D Access To The Deep Web: Tools And Techniques
They operate in what some economists call “digital black markets,” which, although mostly illegal, follow economic principles similar to legitimate markets. It’s very easy to click on something and go down a rabbit hole of the Internet you probably don’t want to visit. We do not recommend venturing into prohibited, unethical sites on the Dark Web. When you find nasty content, just close all the windows, and Tor will erase your records.
The 14 Best Deep Web Search Engines To Find What Google Can’t
Providers of DefCon, ProPublica, CIA, various libraries, and open-source software are also included in this area. The Deep Web, which includes sites accessible via normal browsers but not visible to search engines, makes up a much larger portion of the Internet. The Dark Web, which is only accessible via special web browsers, uses the same network infrastructure as the Surface and Deep Web but is completely distinct from it. What most people think of as the “Internet” or the world wide web is actually what is known as the Surface Web, or Clear Web.

The dark web threat landscape is continually evolving, with new threats emerging as quickly as existing ones are countered. This makes it imperative for financial institutions to stay abreast of the latest developments and arm themselves with the best defenses. These services are controversial because while they may protect the legitimate privacy of users, they are also widely used to launder money from illicit activities. On the other hand, collusive insider threats involve an employee conspiring with external threat actors to undermine the organization.
Cybercriminals Targeting Financial Institutions From The Dark Web
Using dark web browsers like Tor is legal in most countries, but accessing illegal content or services remains unlawful regardless of the technology used. Organizations should establish clear policies governing the acceptable use of anonymizing technologies by employees. Organizations that monitor dark web activities can detect credential exposure and potential threats before they materialize into breaches.
The deep web is a part of the Internet that, while not completely hidden, cannot be indexed by search engines like Google. These parts of the web are hidden behind firewalls, paywalls, and other types of web security. Within this vast, hidden space, a parallel financial ecosystem has developed that operates outside of traditional systems. These financial services on the deep web have evolved significantly in the last decade, leveraging emerging technologies such as cryptocurrencies, advanced encryption, and anonymity networks. Additionally, Trustwave SpiderLabs recommends organizations examine their network to remove, lock down, or monitor legitimate tools, like TeamViewer, that a threat actor can leverage to gain access. If your Social Security number is found on the dark web, take immediate action to protect yourself.
You can find plenty of old articles and media resources archived by the US government. Unlike the deep web vs dark web that encompass such secrecy or illegality, this surface web is totally safe to be used daily as well as it falls under more familiar laws and regulations. Hence, while the face of the internet remains the surface web, the deep and dark web are the hidden layers of the internet that require caution and understanding to traverse.
Threat intelligence enables proactive threat hunting, where analysts actively seek out potential threats before they manifest into attacks. This could involve monitoring dark web forums for mentions of their organization or upcoming attacks, identifying patterns in threat actor behavior, and staying abreast of emerging cybercrime tools and techniques. The dark web also hosts forums where threat actors can buy and sell stolen insider information. This can include non-public information about upcoming mergers, acquisitions, or other market-moving news, which can be exploited for illicit financial gain. Financial services institutions, with their vast amounts of sensitive data and monetary transactions, are prime targets for threat actors.
What Are Examples Of Deep Web Resources?
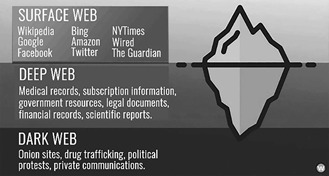
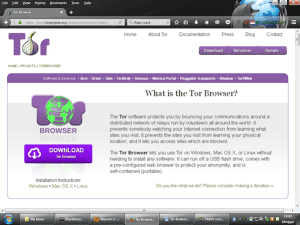
This means there is no easy, direct way for the general public to search this vast amount of unindexed content. In some cases, websites use various methods to block spiders and prevent indexing. These methods include using CAPTCHAs, multiple IP addresses for the same content, non-HTML content or data that spiders cannot pick up, password protection, and unlinked content. Website addresses that end in “.onion” aren’t like normal domain names, and you can’t access them with a normal web browser. Addresses that end with “.onion” point to Tor hidden services on the deep web.
- The 12 search engines we have introduced you to should provide a solid base on which to start your hunt for content.
- This makes Dark Web sites a rich source of threat intelligence for organizations; however, the design of the Dark Web can make this information difficult to find.
- Many of the directories of .onion sites are themselves stored on .onion sites, though, which you can only access through Tor.
- The financial sector consistently ranks among the most targeted industries year after year, and for good reason.
- It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor.
Both the client and the hidden service host have active roles in this process. Tor networks are popular solutions for maintaining anonymity and privacy and for defeating traffic analysis. Journalists, whistleblowers, dissidents, or generally any Internet users who do not want third parties to track their behavior or interests. Tor serves many good purposes, but also attracts Dark Web users wanting to keep their activities or marketplaces secret and untraceable. Many Internet users use encryption – for example, Virtual Private Networks (VPNs) – to keep Internet activities private. Conventional routing, however, is susceptible to traffic analysis, a surveillance technique that can reveal traffic origins, destinations and times of transmission to third parties.