Navigating the dark web responsibly and cautiously will help ensure your experience remains secure. Always prioritize safety and legality, and remember that your actions on the dark web can have real-world consequences. While browsing online, you might have noticed that the websites you are visiting have URLs starting …
How To Sell Counter-Strike 2 Skins Instantly? A Comprehensive Guide
Nevertheless, Proton VPN says that the situation is different for VPNs. “Within the current Swiss legal framework,” it says, “Proton VPN does not have forced logging obligations.” It goes on to recommend the use of a VPN or Tor connection when using its email client. In any case, it can be used for any dark web activity thanks to various privacy features. Let’s take a closer look at the best VPNs you can use to safely access the dark web. To access the Dark Web, you have to use a browser called Tor, also known as The Onion Router.

Step 5: Configure And Start Tails OS
Be cautious of downloading it from unofficial sources, as they may provide modified versions that could compromise your security. By following these steps, you are on your way to exploring the hidden depths of the internet and enjoying a heightened level of online privacy and anonymity. One of the problems with free VPNs is that they have a poor user-to-server ratio, with too many users and not enough servers. This is not what you want when also using the Tor network, as the two in conjunction will be painfully slow. PrivateVPN allows torrenting and has dedicated servers in its home country for just that purpose.
What Are The Best Privacy Tools For The Dark Web?
Always verify a site’s legitimacy before visiting – onion addresses are long, random strings, making it easier for malicious actors to create lookalike addresses for phishing. A little typo can lead you to a clone designed to trick users into handing over sensitive data. However, the most secure way to use Tor is via .onion sites, which are built exclusively for the Tor network. With your Tor connection established, you can begin surfing the web with the utmost privacy.

How To Access The Dark Web On Your Device
Initially created to protect U.S. intelligence communications, Tor was released for public use in 2003. In 2004, the Naval Research Laboratory then released the code and made it open-source. Since then, volunteers and sponsors around the globe have maintained Tor and the Tor Browser.
Core Anonymous Networks And Protocols
Based on Mozilla’s Firefox, this browser hides all that pinging about in the background. “It’s a web browser. Use it like one. It’s that simple,” says Muffett. That’s the desktop edition, but there’s a version for Android and an unsupported onion browsing app for iOS. The dark web is infamous as a dangerous place, where drugs are bought and hitmen hired, but it can be a safe way to browse the internet if your privacy is serious concern. A VPN can help disguise your use of Tor and your visits to dark web resources.
Cybersecurity Blogs And Forums
This negates the need to download, install, and run the Tor browser separately, and lets you access the Tor network without your ISP knowing. Using a VPN in conjunction with the Tor (The Onion Router) browser is the best way to access the dark web safely. A dark web VPN prevents websites and your ISP from knowing when you’re using the Tor browser.
Tor, I2P, and Freenet are three common technologies that make up the dark web. For instance, your email inbox, online banking account, or a company’s internal database resides in the deep web. To access these resources, you need to log in with a username and password using a traditional browser like Chrome or Safari. For example, your Geekflare.com—your trusted business resource for growth exists on the surface web. To reach Geekflare.com, you can either type its URL in your standard web browser or search for Geekflare in your favorite search engine. The U.S. has a strong legal framework when it comes to cybercrime, and many of those laws apply directly to activity on the dark web.
How To Remain Safe While Using The Dark Web – Essential Tips
It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor is by far the most widely used dark web network and is the biggest network in terms of content and activities. On the other hand, the deep web is the hidden part of the Internet that contains private or restricted content that is not indexed by search engines. Unlike the surface web, you can’t access deep web resources directly through a search engine; they require login credentials or special permissions. However, the line is drawn at what you’re doing once you’re on the dark web. Engaging in illegal activities—like buying drugs, trafficking stolen data, or distributing harmful content—is absolutely against the law.
- The dark web is a part of the internet that is not accessible through traditional search engines and requires specific software or configurations to access.
- Ensure that you’re aware of what is permissible in your jurisdiction.
- Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent.
- As the digital environment evolves, so do the tactics employed by cybercriminals, law enforcement agencies, and privacy advocates.
- The concept of an encrypted, hidden layer of the internet began taking shape in the 1990s.
- KEY TAKEAWAYS If you’re in a hurry to find out the disposable email service provider, have a q…
The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. Learn how to access .onion sites safely with tips on privacy and security for your dark web journey. It’s simply a hidden part of the internet that you can reach using special tools like the Tor Browser.
- Tor Browser is pre-configured with privacy settings optimized for secure browsing, so you can enjoy a higher level of anonymity right from the start.
- Just because the dark web feels anonymous doesn’t mean it’s invisible—especially to U.S. authorities.
- Data theft, cloud breaches, and malware-free attacks are on the rise.
- The dark web is a hidden part of the internet that isn’t indexed by traditional search engines and requires special software like Tor to access.
- As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with.
Not many providers support this, so a manual and sometimes tedious configuration is needed. The exit node can also be compromised but our experience has shown this happens extremely rarely. Besides, if the exit node malfunctions, you still have your trustworthy VPN so no one can track your footsteps.
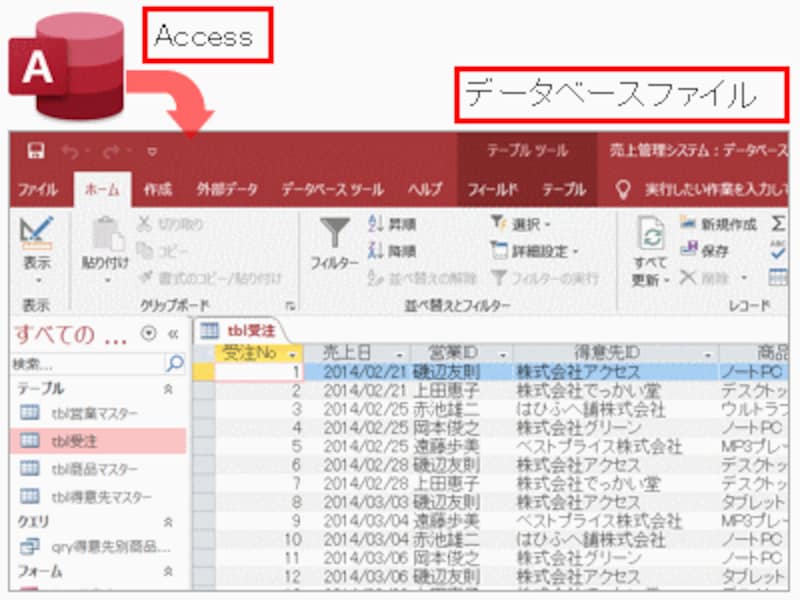
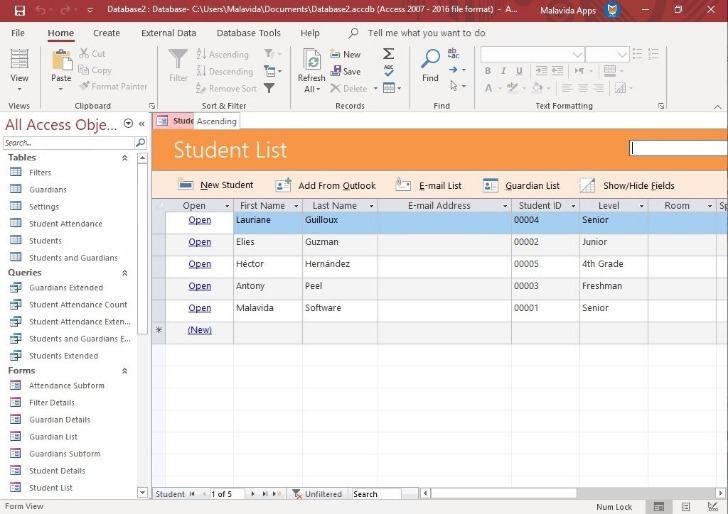
KEY TAKEAWAYS Tor is one of the most popular private browsers in the industry. Each time you want to use it, you won’t have to download it on your device; instead, you can insert the DVD or the USB flash drive and use the OS. Furthermore, you must download and install it via the router console port before configuring its settings. Individual apps are configured separately to function with I2P, whereas a web browser’s proxy setting must be configured to use the correct port. Dark Web also does not have traditional websites like you find on the Surface web. By traditional websites, we mean websites with domains like .com, .org, .gov, etc., and easy-to-remember names, like google.com.