By familiarizing yourself with these networks and protocols, you gain a clearer understanding of the diverse strategies people use to stay hidden online. Each network has its strengths, drawbacks, and intended use cases. Freenet is one of the oldest anonymity networks, focused on providing censorship-resistant communication. Instead of simply routing traffic, Freenet stores encrypted chunks of data across nodes.

Risks Of Accessing The Dark Web:
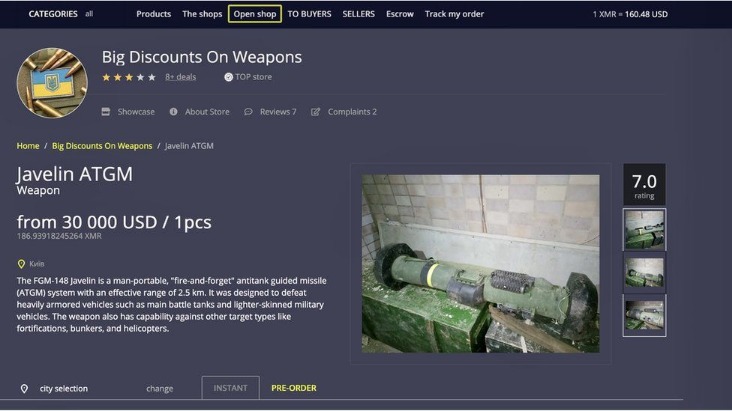
We’ll also share some tips for protecting your personal data if you decide to explore it. So, I mentioned previously, I briefly touched on the fact that it’s not always possible for law enforcement to catch and bring the perpetrator to justice in these sort of situations. So, people high up in these criminal enterprises, hitting them where it hurts the most, which is their reputation. We’ve probably touched on it before in this podcast, but reputation is a very big deal on the dark web and in the, kind of, cyber crime community.
However, it’s important to note that this built-in VPN is not designed to connect directly to the Tor network or .onion sites. But it’s recommended that you stick to Tor Browser still for true dark web access. It can access the regular internet through “outproxies,” but that’s not its strongest suit.
Common Dark Web Threats
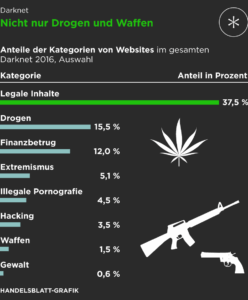
Bitcoin, once the go-to currency for illicit trade, is increasingly viewed as traceable. Cybercriminals and privacy advocates alike are transitioning to more obscure digital currencies. Forums often host ideological debates, echo chambers, and radicalization pipelines. These sociological undercurrents shape user behavior, attract like-minded individuals, and sometimes spawn collective actions—both beneficial and destructive. Another alarming development is the proliferation of zero-day exploit markets. Vulnerabilities previously unknown to software vendors are traded at premium prices, empowering hackers to penetrate even the most fortified systems.
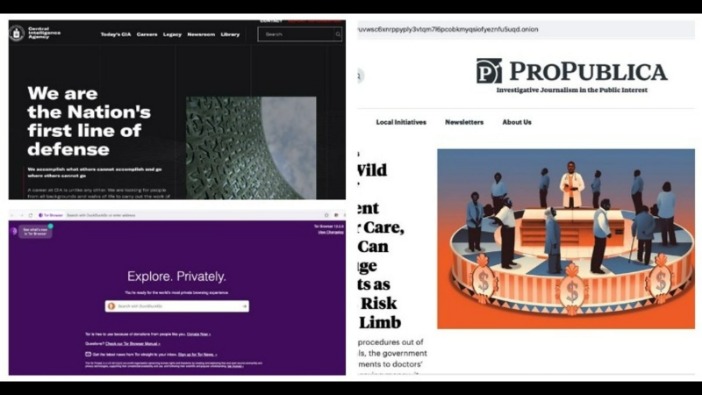
If you’re lucky enough, you can find it on clearnet privacy forums. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted.

Dark Web Chat/Social Networks
Hackers may target users to steal information or infect devices with viruses. Even after establishing a connection via the Tor network, users are met with a barren interface—void of bookmarks, ads, or algorithms guiding behavior. This is where the vast difference in user orientation becomes apparent. In the surface web, search engines curate relevance; in the Dark Web, individuals often need referral links, invitation-only forums, or hidden indexes like The Hidden Wiki to even begin.

The Best Antivirus Software For Multiple Devices: Secure Every Digital
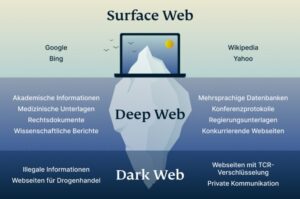
If you’re using Windows, macOS, Android, or iOS to access the dark web, there are a lot of extra safety precautions you need to enact before even connecting to your VPN. Just like there are privacy and security best-practices for using the surface web, there are some dos and don’ts for browsing the dark web. Cybercriminals and even regular criminals also use the dark web to conduct illegal activities. Most online content (whether stored in centralized servers or on a distributed P2P network, like blockchains) actually belongs to the deep web. The deep web is anything and everything online that you can’t find using a search engine.
Why Should I Use A VPN Before Tor?
For more information, read more about the most secure email service providers in my other post. So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. It’s impossible to access the dark web with a regular browser like Chrome or Safari.
- It’s your responsibility to understand and abide by local regulations.
- For this reason, iPhone and iPad users can’t use the real Tor Browser app.
- There are several misconceptions about the dark web, as many users use it for illegal activities.
- This guide explores how to access the dark web safely on different devices while also covering both the benefits and risks of delving into this part of the internet.
- Plus, in some regions, accessing the dark web alone may raise suspicion or get you flagged for extra monitoring.
If you’re unsure about a link, do some research or ask trusted sources within dark web communities. Open the VPN app and connect to a nearby server before launching the Tor Browser, and that’s it! As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman. It’s also used by journalists, advocacy group members, and political refugees in hiding.
The Anatomy Of Anonymity: How The Dark Web Operates
Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity.
The Dark Web—a hidden part of the internet accessible only through specialized tools like Tor—often conjures images of mystery, intrigue, and even danger. However, navigating this hidden digital landscape in 2025 presents heightened security risks, from advanced cyber threats to targeted surveillance. This guide provides clear, step-by-step instructions to safely explore the Dark Web using Tor, helping you stay protected, informed, and anonymous.
- Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more.
- JavaScript is a programming language used by websites to add interactive features, such as videos, forms, and dynamic content.
- Tumbling services—or cryptocurrency mixers—are frequently used to obfuscate the origin of funds, further enhancing anonymity.
- Techniques such as undercover operations, malware tracing, and blockchain analysis help identify users.
When browsing .onion websites, it’s important to ensure that the website is legitimate and not a fake website created to steal information. Though the dark web is designed for anonymity, law enforcement has developed tools to investigate and track illegal activities. Agencies like the FBI and Europol have infiltrated marketplaces and arrested key operators. Techniques such as undercover operations, malware tracing, and blockchain analysis help identify users.
I review privacy tools like hardware security keys, password managers, private messaging apps and ad-blocking software. I also report on online scams and offer advice to families and individuals about staying safe on the internet. Before joining PCMag, I wrote about tech and video games for CNN, Fanbyte, Mashable, The New York Times, and TechRadar. I also worked at CNN International, where I did field producing and reporting on sports that are popular with worldwide audiences. Finding real dark web links is possible via some clear web forums or social platforms like Reddit, though it’s just as easy to come across phishing links containing malware or links to scam sites.
How To Turn Off SafeSearch On Google, Bing, DuckDuckGo, Yahoo
I2P’s most attractive angle is to access its own internal eepsites, which are its version of .onion sites. It is definitely a strong contender for the best, strongest, layered encrypted web browser. However, there are plenty of legal and legitimate online activities that require privacy and anonymity.