“A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. Darknet markets can also be used to promote freedom of speech and expression. In some countries, the government heavily censors the internet and restricts access to certain websites or online services. Darknet markets, however, are not subject to the same level of censorship and can be used to disseminate information that may be banned or suppressed in other parts of the internet.
Legitimate Uses For The Dark Web
We are also the longest running dark net search engines with over 1 million pages indexed! Telegram has now introduced voice chats for channels that can have unlimited participants so channel admins can conduct live voice chat sessions. Despite Silk Road’s ultimate failure and Ulbricht’s incarceration, the Dark Web continues to be a hotbed of criminal marketplaces.
Navigating Ransomware Attacks While Proactively Managing Cyber Risks
A company trading at a significant discount to its peers or historical averages could be a deep value stock. However, from another point of view, DPI can also be seen as a threat to privacy. The technology allows organizations to monitor and analyze individual users’ online activities, including their web browsing, email, and messaging. Having your social security number leaked on the dark web requires immediate action. Watch financial accounts closely, consider enrolling in identity protection, and report any suspicious activity to the authorities or the Federal Trade Commission.
Darknet Market Versus Shuts Down After Hacker Leaks Security Flaw
While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes. For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity. The darknet market is a segment of the internet that indexes various illicit and legal activities, primarily operating on the dark web. It allows users to buy and sell goods and services anonymously, making it a unique ecosystem with distinct purposes.
In July 2016, passwords for roughly 200 million Yahoo! accounts appeared for sale. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. The “dark web” is a part of the world wide web that requires special software to access. Once inside, web sites and other services can be accessed through a browser in much the same way as the normal web. Most darknet markets have a dispute resolution process that involves reviewing evidence and making a fair decision based on the provided information.
Agentic AI–Driven Threat Intelligence Tailored For Every Function
In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. In addition to traditionally forbidden trade, the dark web became a hub for the sale of stolen information. Credit card and social security numbers are routinely purchased, as are passwords for e-mail accounts—sometimes en masse. In March 2012 Russian hacker Yevgeniy Nikulin and three accomplices stole passwords for 117 million e-mail addresses from the social media company LinkedIn and then offered the data for sale on the dark web.
How Do Users Remain Anonymous?
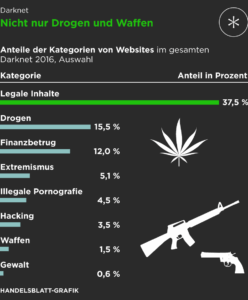
Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. Several darknet marketplaces currently exist that follow the Silk Road model, allowing anonymous cryptocurrency transactions on websites only accessible through dark web browsers. The dark web is a part of the internet that isn’t indexed by search engines.
Cryptocurrency Transactions
Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. Dark markets, often accessed through specialized marketplaces within darknets, are breeding grounds for underground economies, where users can engage in transactions while evading law enforcement and ethical oversight. Another reason that darknet markets exist is to protect their users from law enforcement.
Those wishing to enter the darknet site via a regular browser, will need to use a service called ‘Tor2Web’. It’s no secret that healthcare is the industry most plagued by data breaches. Reports show the value of a health record can be worth as much as $1,000, whereas on the dark web, a credit card number is worth $5 and Social Security numbers are worth $1. If you get an alert that your personal data, like an email address, password, phone number, or social security number, was found on the dark web, you don’t need to panic, but you should act fast. Tor is an entire network (not just a browser) of volunteer-run servers, known as nodes or relays, that work together to hide online activity. When you use the Tor Browser to visit a dark web site, your data doesn’t take a direct path.
- They operate similarly to regular e-commerce sites but use cryptocurrencies for transactions.
- This browser enables access to websites with .onion domain extensions, which are specific to the Tor network.
- People use it for various legitimate reasons, such as bypassing censorship in restrictive countries.
- 2, we present the lifetimes of the selected marketplaces and the reasons behind their closures.
- For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity.
This level of anonymity is particularly appealing to individuals who are concerned about their privacy and want to keep their personal and financial information separate. By taking steps to protect yourself and being aware of the risks involved, you can help to ensure that your transactions are as safe and secure as possible. To fully understand the Deep Web, it is essential to know the difference between it and the Dark Web.
This includes drugs, counterfeit money, stolen data, hacking tools, firearms, and even access to criminal services such as hitmen or hackers for hire. Darknet markets, also known as cryptomarkets, are online marketplaces that operate on the dark web. These markets are accessible only through specialized software, such as the Tor browser, which allows users to remain anonymous and conduct illicit activities with relative impunity. While the illegal nature of many darknet market transactions is undeniable, it is important to understand that these markets also serve a purpose beyond facilitating criminal activity. One of the main purposes of darknet markets is to facilitate the sale of illegal goods and services. These markets are often used by criminals to sell drugs, weapons, and other contraband.
Does Silk Road Still Exist?
The listing shown below is for a “Corona Lock Down Survival Pack” The contents? Perhaps even more concerning are listings for coronavirus “cures” that have begun to spring up on certain marketplaces. In order to gain information on the analysed marketplaces, we collected additional data from the Gwern archive on dark marketplace closures1. To compile comprehensive information, we also used law enforcement documents on closures as well as a number of online forums31,32,34 dedicated to discussing dark marketplaces (see Supplementary Information Section S2). Out of the selected marketplaces, 12 were subject to an exit scam, 9 were raided, 3 were voluntarily closed by their administrators, and 7 are still active.
Since the disappearance of Evolution and Agora, several smaller markets have appeared, with some approaching the size of Evolution or Agora at their peak, though no one market leader has emerged. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Internet surveillance of the surface net is pervasive, and may limit corporate and individual ability to communicate privately and safely online.
If the attorney attends the hearing, the conspiracy charges of the accused remain while 90% of the other charges drop. When the accused vendor is arraigned and released, his lawyer asks if he wanted to do a proffer. Proffer is telling the feds or law about the accused’s actions, employers, customers, and vendors. A visual barrier is a solid-colored vacuum seal bag that anyone can’t see through. In addition to C4 plastic explosives, rocket launchers and numerous other weapons can also be purchased on the Darknet.