You may be targeted by law enforcement, exploited by hackers, or threatened by criminals using the dark web for nefarious purposes. This setup is easy to configure, and you don’t need any special settings or features. Just turn on your VPN, wait for the connection to stabilize, and launch Tor. Your internet activity is still subject to exit node risks, so always use HTTPS and avoid entering any personal information on unencrypted sites. You’ll know you’re on the dark web when the URLs end in “.onion” — these addresses only work inside the Tor network.

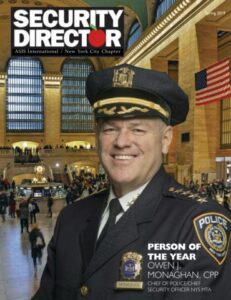
How To Effectively Communicate Cyber Risk To The Board: Lessons From APRA Compliance
Remember to update the Tor Browser regularly to ensure you have the latest security patches, and scan your computer for malware regularly using antivirus software. As I mentioned above, the dark web is a decentralized, non-indexed network of web pages, and the sites don’t use standard URLs. There are marketplaces where people can sell stolen credit card numbers, conduct illegal drug transactions, and scam people out of their cash and crypto. If you carefully follow the six tips we have provided, you will be well on your way to accessing the dark web safely, securely, and anonymously.
How To Change The Onion Browser’s Security Settings On IPhone
I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you.
Step 2 Visit A Good Dark Web Search Engine
Some sites are safe to use, especially those where you don’t need to provide sensitive information to use. ExpressVPN is slightly expensive but a trustworthy provider for risk-free dark web browsing. You’ll also enjoy its Smart DNS support, 24/7 live chat service, the Keys password manager, and a lot more. Feel free to grab its 49% discount thanks to 3 free months for the annual plan. It also has 10 simultaneous connections, support for all devices, and server obfuscation that works in China. These websites will now work without issues, as the VPN hides the exit node and makes your traffic look inconspicuous.
Which Is The Best Laptop For Cyber Security Course?
Unfortunately, it requires you to have an invitation code to create an account. This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. To access a dark web address, you must use a VPN and a suitable browser (it should be Tor).
Social Media
The final relay before your traffic goes to the destination website is known as the exit node. The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content.
Step 3: Use Best Practices For Privacy
The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. Those who access the dark web do so via the Tor (The Onion Router) browser. The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones. For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”.
That said, there are still some ways to protect yourself when using the Tor Browser. TOR (The Onion Router) is a software that makes it possible for users to communicate and browse the internet anonymously. This is achieved by directing internet traffic through a global network of servers, which conceals the user’s identity and location. The main purpose of TOR is to provide access to the dark web and bypass censorship and surveillance in countries with restricted internet access. On the other hand, the TOR browser is a web browser that uses the TOR network to offer users private and anonymous internet browsing.

Like NordVPN, this provider doesn’t store logs and has around 20 third-party audits to prove it. Its RAM servers and Private DNS go a step further to protect your identity online. Not to mention its Advanced Protection that blocks malicious sites, trackers, and ads. This is accompanied by the Network Lock kill switch that also prevents IP leaks.

Make sure to protect your device with reliable anti-malware to mitigate such attacks. Admittedly, you might be practicing caution while venturing the dark web. However, a slight action or a wrong click on some websites can land you in deep trouble. With any malware infecting your device, you can suffer horribly and come across data loss and, in the worst-case scenario, lose your device, too. According to the Into the Web of Profit report, the following services or tools may pose a data compromise or network breach threat.
From data breaches to counterfeit products and unauthorized brand use, malicious actors exploit the Dark Web’s anonymity for financial and reputational harm. These include VPNs, proxy servers, and anonymizing networks such as Tor, which are used to hide a user’s online activity and location. Some dark websites offer hacking services, such as password cracking and DDoS attacks, for a fee.
- Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there.
- These include VPNs, proxy servers, and anonymizing networks such as Tor, which are used to hide a user’s online activity and location.
- Browsing the dark web safely requires more than just Tor — your ISP can still see you’re using it.
- Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs.
It is designed to provide online anonymity and privacy to its users. Journalists, activists, and individuals concerned about online privacy and security often use it. Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble. Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web.