You’ll notice that some websites’ loading times are longer when using Tor. Once the app is installed, simply open it up and sign in with the credentials you provided during registration. The dashboard should open properly, indicating you’re ready to connect to any VPN server. This is just the first but also very important step to go to the dark web anonymously.
It’s not easy to find what you’re looking for on the dark web, especially if you want to do it safely. You should only ever access websites you know are safe because they’re vetted by websites or other sources that you already know are safe. Take a look at the sites that these directories have collected and see what topics interest you. If you want to improve your security further, you could also use a VPN at the same time as Tor. For the most security-conscious, you can even install the Tails operating system on a flash drive and run Tor from that. Carefully consider your actions and motivations when exploring the dark web.
Understanding The Basics: What Is The Dark Web And How Can It Be Accessed On An IPhone
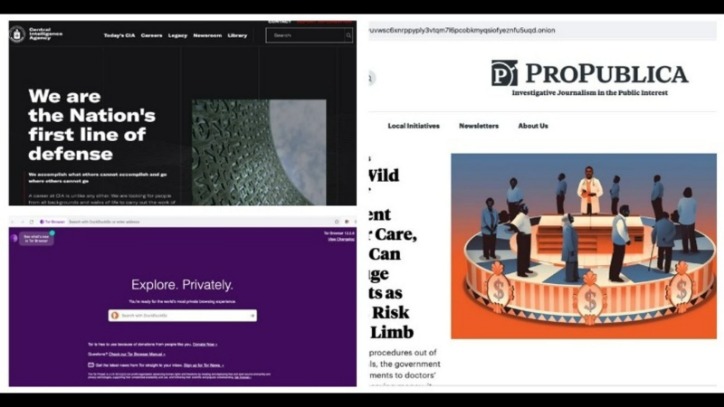
The first step in accessing the dark web using DuckDuckGo is to download and install the Tor Browser. Tor is a powerful tool that enables you to browse the internet anonymously by routing your connection through a network of volunteer-operated servers. Make sure you install and run strong security software on your computer and devices to help ensure the privacy and security of your data. For example, dissidents who fear political prosecution from their governments might use the dark web to communicate with each other. As many as 70.79% of users claim to use the Tor browser for anonymity, 62.28% said they use it for additional security, and 27.07% used it out of curiosity about the dark web.
FAQs About Accessing The Dark Web Safely On Your Phone
Tor (The Onion Router) is a free, open-source browser that allows users to access and browse the dark web anonymously. To access a dark web resource, you will need to know its web address to the letter. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers.
Is It Illegal To Access The Dark Web?
We’ve clarified how to go on the dark web anonymously with the help of a VPN. A VPN is a confusing factor for many because there are two ways to use it with Tor. It might be because of the poorly maintained site or Tor’s slow speed because of the way it works. Either way, some sites take up to a minute or more to load, so don’t fret.
Navigating The Dark Web: Do’s And Don’ts
Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. Even if someone is asking and claims to be a legitimate source, don’t trust, and don’t reveal anything about yourself. On that same note, do not download or click on email attachments from suspicious senders.
Utilize Virtual Private Network (VPN) For Data Security
- Instead, you will need to rely on curated directories and specialized websites to find what you are looking for.
- You can’t just start surfing the dark web by typing something into Google.
- It’s developed by Mike Tigas, with support from the Tor Project and the Guardian Project.
- By following these essential tips, you can navigate the Dark Web on your iPhone with enhanced safety and privacy.
- However, because it’s almost completely anonymous, there are a lot of illegal images, information, products, and services on the dark web.
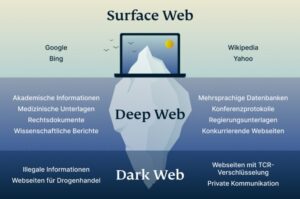
That’s not to say that the entire deep web consists of these difficult-to-find websites. If you have a legitimate or viable need to access the dark web, you’ll want to make sure you stay safe if you decide to use it. Malicious software — i.e. malware — is fully alive all across the dark web.
Maintain Anonymity
Next, disable Javascript in your Tor browser to prevent malicious scripts from attacking your browser sessions. You can disable Javascript by clicking on “Preferences” in the macOS app or “Settings” in the Windows app. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users.
- The Tor Browser is a free and open-source browser that provides anonymity and privacy by routing your internet traffic through a network of volunteer-operated servers.
- So not only is your web activity hidden, but you can mask your IP address by connecting via a wide range of global VPN server locations.
- The interface is simple to navigate, and all features and settings have helpful explanations.
- That’s why the defense is the best offense, so it’s worthwhile to be leveraging a service that monitors your personal data for you.
- This can often be for political reasons, but also because they may be involved in illegal activities, such as the ones listed above.
- A VPN app opens another potential vulnerability, as it can log the sites you visit via Tor.
When you purchase using links on our website, we may earn an affiliate commission at no extra cost to you.
Several pages and websites on the dark web are illegal and highly unsafe and can pose significant threats to your digital privacy. For instance, you can find malware, ransomware, and other potential cyber threats on the dark web. There’s a high chance of clicking on an infected link or downloading spyware or malware. Also, the bad actors can use tools like keyloggers to gather data and infiltrate your system.

While it’s technically possible, using a VPN is highly recommended to protect your identity and location. With easy setup and extensive monitoring, you can maintain your digital identity and gain peace of mind. Have you ever shared the make and model of your first car, your favorite movie or band, or your high school graduation year? This information helps unsavory characters figure out online passwords and security questions. When creating or updating your account passwords, make sure to choose ones that are difficult to guess. To use the dark web safely, use as many privacy-enhancing tools or programs as you can, and do not identify yourself in any way to anyone for any reason.
Patience is key here, as this process can sometimes be slower than standard browsing. Explore a diverse selection of goods and services, with a focus on privacy and security. Assume you have a checking or savings account with a financial institution. And if you type in “online banking” into a search engine, you’ll get to the login page, but not your personal information. Yes, you can access the dark web using cellular data, but a VPN is still recommended to ensure your anonymity.