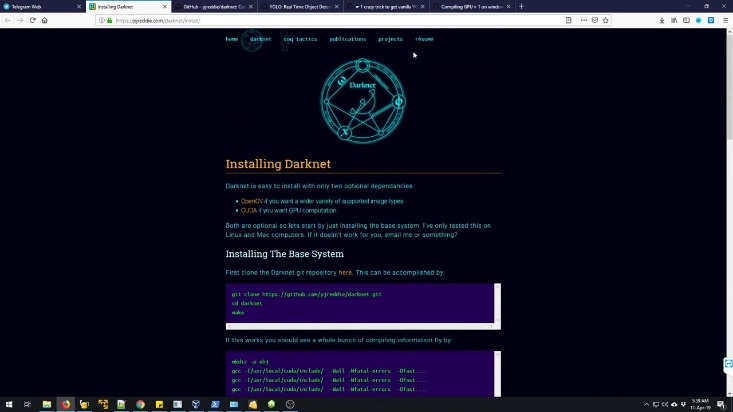
Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity. It allows access to the .onion sites on the dark web that you won’t find using a regular browser. The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption.
But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access.
How Cryptocurrencies Enable Safe Trade On The Darknet
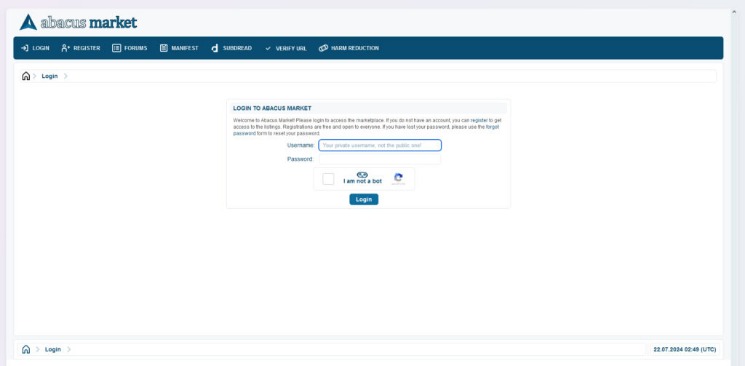
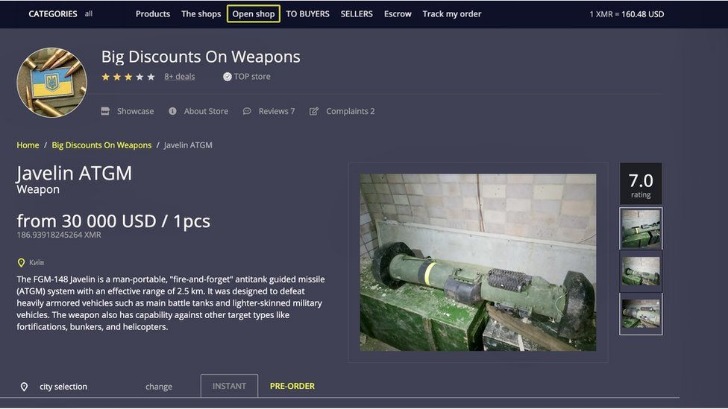
The websites (darknet markets in this case) on the onion network can only be accessed using Tor. The dark net is famous for being a hub of black market websites for buying and selling products and services. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace.
Never Use Your Credit And Debit Card For Purchases
However, there’s a lot more to DNM (Darknet Market) security than just human verification. Hence, you may find more dead links on link directories than on search-engines. Note that if you’re using NordVPN, go with the “Onion over VPN” servers.
Secure And Efficient Drug Trade On Darknet Platforms
This has led certain individuals to engage in transactions of illicit or illegal goods. And the Deep Web is where the dark side of the Internet how to create a darknet market flourishes. Every communication is encrypted, so even the simplest transaction requires a PGP key. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers. Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web.
The market has built trust among users as it brings vendor reviews from different places and then verifies them with PGP signatures – that way, the buyers feel confident. All payments on the platform are via Bitcoin (BTC) and Monero (XMR) for anonymous transactions. Who doesn’t like privacy, especially when dealing with the buying and selling of illegal products and services? Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others. To access the darknet you’ll need to download and install the Tor (the onion routing) browser. To ensure the safety of your darknet market, it’s important to use a reputable hosting provider, to use a virtual private server (VPS), and to establish strict rules and regulations.
The use of cryptocurrencies, particularly Bitcoin and Monero, further enhances privacy by eliminating traceable financial transactions. The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL. Everything is in English, but users from around the world are welcome. You’ll get stolen credit cards, remote desktop account info, personal details, and various logs.
Torrez Market
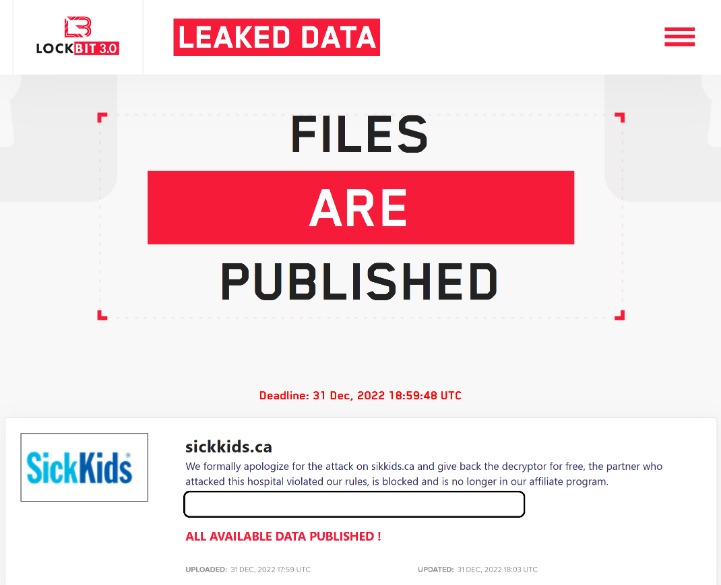
The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. The most recent example is the shutdown of the oldest marketplace Hydra Market in 2022 which took a combined effort of the FBI and the German authorities. Unfortunately, that as well didn’t stop other darknet markets from rising. That’s exactly what happens when it comes to the dark web marketplaces. We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online.
- These products are often sourced from international suppliers, ensuring competitive pricing and a wide variety of options.
- Darknet markets are accessible through encrypted networks like Tor, where users’ identities are masked for enhanced anonymity.
- Companies should be extremely cautious when dealing with ransomware.
- In the U.S., at the federal level, the Federal Bureau of Investigation’s (FBI) Cyber Division is the agency within DOJ charged with combating cybercrime.
- Using bitcoin and accessing the darknet for the first time can be bewildering.
- You can use platforms like Tor and I2P to create a hidden service website that is only accessible through the dark web.
Fraudulent Markets
On average, the marketplace consists of more than 11,000 items and 1000 vendors. In April 2016, its APIs were compromised, resulting in stolen messages. But since its relaunch, the developers are focusing more on operational security and ensuring that users can have a good experience on this site.
This mechanism holds funds in a secure account until the buyer confirms receipt of the product, reducing the risk of fraud. Additionally, multi-signature transactions are increasingly common, requiring multiple parties to approve a payment, further enhancing trust between users. The use of onion links ensures that access to these markets remains anonymous, further enhancing user privacy.
Acronis Cyber Protect Cloud: New Version C2505
- The vendors openly advertised their drugs on Hydra, typically including photographs and a description of the controlled substance.
- If your information has been compromised, then it’s likely that your phone number is also on the dark web.
- Make sure that when you download the Tor file, it’s from their official website.
- Monero’s my go-to for dark web payments because it’s darn near impossible to trace.
- On Friday the 13th of January, the WayAway team hacked Solaris, taking advantage of a weakness in its coding, and shut it down.
This involves reaching out to potential users and promoting your platform. You can do this by advertising on other darknet markets, forums, and social media. However, if you’re up for the challenge, it can be a lucrative business.
That means that Google wants to minimize the amount of time users spend searching for certain queries. Did you know that Google only shows you a glimpse of all the websites that actually exist? The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search.
The quantity, price, and characteristics of the product are all provided. However, the platform lacks an advanced search option and a wallet-free payment option. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins. DarkOde Reborn is a great darknet market where you can find anything you want. The website has a great design and a clean and organized interface that is easy to use.

And while the dark web isn’t synonymous with illicit activities, it’s undeniably the breeding ground for the internet’s black markets, hacker forums, malware vendors, and other illegal activity. Accessing these markets is straightforward, with users connecting via Tor or other encrypted networks. Onion links provide direct access, ensuring anonymity and bypassing traditional internet restrictions.
How Kaspersky researchers obtained all stages of the Operation Triangulation campaign targeting iPhones and iPads, including zero-day exploits, validators, TriangleDB implant and additional modules. Moreover, the rise in the popularity of other cryptocurrencies with enhanced privacy features might also influence the Bitcoin mixer market. Service providers could diversify their offerings to include mixing for these alternative cryptocurrencies, further expanding the scope of their operations.
Vendors are rated based on their reliability, product quality, and delivery speed, creating a competitive environment that benefits consumers. This system of vendor ratings ensures that only the most trustworthy sellers thrive, further enhancing the overall user experience. The evolution of darknet markets in 2025 reflects a growing emphasis on user safety and operational efficiency.