In this post, we will teach you everything you need to start exploring the dark side of the Internet with the help of Tor. If one of the built-in bridges doesn’t work, you can also try manually entering a bridge address. Head over to Tor’s official Bridges page for more information.
Roundup – Best VPNs For Speed
For journalists, students, researchers, and security professionals, it’s a powerful tool when used ethically and safely. Journalist in India → Uses Tor to access a whistleblowing portal → Submits information anonymously while protecting their identity. These URLs are usually very long, consisting of a random jumble of letters and numbers.

Are Sites On The Dark Web Illegal To Use And Visit?
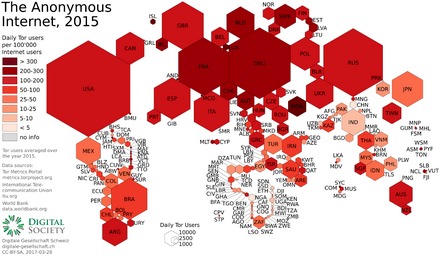
Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor. Using Tor is especially helpful in countries where authoritarian governments censor the internet, preventing citizens from accessing news outside their country. Copy your desired onion URL and paste it into the address bar at the top of the screen to begin searching on the dark web. Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website. By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges.

Tor was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag. Tor was designed to protect American intelligence communications online. Tor Browser has since become a popular tool of journalists, activists, and others that may be subject to being monitored online. We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention. If you find that Tor is restricted in your current location, you can use a bridge.
Using a VPN is perhaps the easiest and most efficient way to protect your online travels from prying eyes, as it hides your real IP address, and encrypts all of your online traffic. This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels. Check out my article for more information about the dark web and how to access it while staying safe. One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web.
A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing. A VPN, in combination with Tor, further enhances the user’s security and anonymity. That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. Again, we can’t emphasize enough that security and anonymity are paramount to those on dark websites. Your ISP and the government might not be able to view your activity when on the Tor Network, but they do know you are on the Tor Network, and that alone is enough to raise eyebrows.
Understanding the strengths and limitations of each solution helps you select the best tool for your specific needs. Follow this step-by-step guide carefully to ensure safe, anonymous, and secure access to the Dark Web using Tor. Understanding the Dark Web and its access tools, such as Tor, is crucial for anyone considering exploring these hidden parts of the internet safely and responsibly. For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. These settings can be found in the Router Console’s configuration panel. Tor Browser masks your IP address and routes traffic through multiple servers.
IP Address
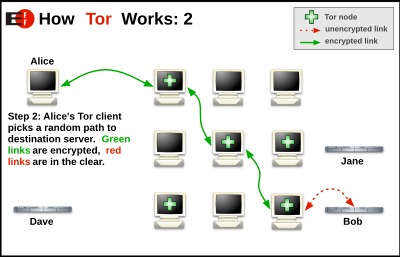
Tor’s onion routing method reroutes your data through a series of independent nodes. Though Tor is slower, the process of rerouting data through nodes makes it more difficult to trace your activity back to you. Lokinet is easier to set up than I2P, and it may run faster than Tor in some cases, especially when visiting regular websites through its secure network.
Connecting To The Tor Network On Any Device
You can check the Tor network status on the official Tor Project website using any other browser. You can also prioritize onion sites when onion site is available. When you open a website that has a ‘.onion’ mirror, you can set the Tor browser to redirect to its onion counterpart automatically.
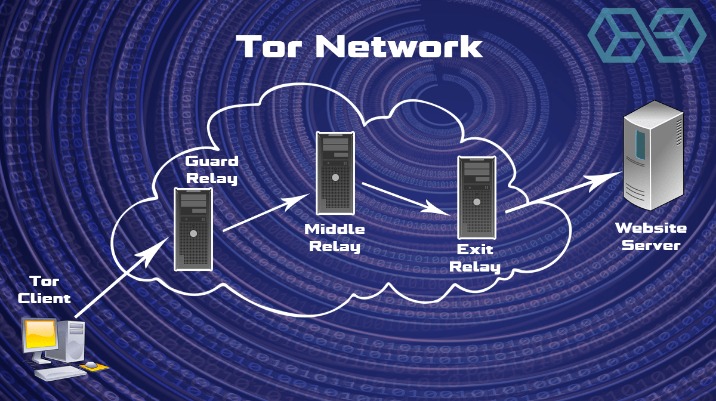
Tor over VPN also doesn’t protect users from malicious Tor exit nodes. Because Tor nodes are made up of volunteers, not all of them play by the rules. The final relay before your traffic goes to the destination website is known as the exit node. The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either.
Don’t Buy Anything
The Tor Browser is an essential tool for anyone seeking privacy and anonymity online. By following the tips above, you can use Tor safely and access the dark web responsibly. Using the internet anonymously is becoming increasingly important in today’s surveillance-driven world. The Tor Browser is a powerful tool designed to protect your privacy and enable anonymous browsing. If you decide to visit Tor’s hidden or anonymous servers, be mindful of the sites you visit. Despite the Tor Project’s good intentions, Tor has developed a bad reputation in the mainstream press, and not without cause.
How To Access The Dark Web On IOS
- Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data.
- One way to stay safe is to use a VPN while accessing the dark web, so be sure to check out my article on the best VPNs for the dark web.
- Alternatively, there’s IPVanish who claim to be the world’s number one VPN for Tor and comes highly recommended, you can save 60% on the annual plan here.
- Tor uses onion routing to encrypt and reroute web traffic through Tor’s onion network.
The Tor Browser protects you from tracing, tracking, surveillance, and censorship. This allows you to access Facebook through Tor, and your connection doesn’t ever leave Tor where it can be snooped on. This may be useful in countries that block Facebook, for example.
Jump Links
Here, select the ‘Always connect automatically’ option if you want the browser to automatically connect to the Tor network every time you start the browser. Then, click on the ‘Connect’ button to connect to the Tor Network. The Tor sends traffic through at least three relays (nodes) to reach its destination. These nodes can be an entry node, a relay node (or middle relay), or an exit node. Each time you click a link or load a webpage, the nodes are reset.
- That allows .onion sites to be accessible anonymously without services like DNS.
- There are many fake marketplaces and platforms that might offer to sell you goods or services but actually take your money without providing anything in return.
- The dark web is a refuge for information leakers and whistleblowers.
- It’s simply a part of the internet that isn’t indexed by traditional search engines like Google and requires special tools to access.
- Many .onion sites will even give you a security warning if you try to access them using that sort of service.
- In this guide, we will walk you through the steps to access the dark web using DuckDuckGo on the Tor browser, ensuring your safety and anonymity throughout the process.
Using Tor Browser #
And even if you find a VPN that does, you’ll still need to perform a manual setup, which is inconvenient and time-consuming. One of the key features of Tor Browser is its ability to access the dark web. By using Tor Browser, individuals can navigate websites on the dark web that are not accessible through regular browsers. It allows users to explore hidden marketplaces, access encrypted messaging services, and browse content that may not be available through traditional means. Within the dark web, there are various hidden websites, known as darknet markets, where illicit goods and services are bought and sold. These can include drugs, weapons, stolen data, and even hacking services.
Step 7: Use Additional Security Tools
You can also be identified if you log into an online account or provide personal details to a website while using Tor. This process anonymizes your browsing not only to websites but also to your internet service provider and anyone trying to monitor your network traffic. The first step is to download and configure the Tor browser from its official website. The Tor browser is your gateway to the dark web, allowing you to access .onion sites anonymously. Tor routes your traffic through a chain of relays to obscure your IP address. This makes it harder for websites, ISPs, or surveillance tools to see who you are or what you’re doing.