Think big names like Target, Equifax, Facebook, or any number of hospitals, retailers, or travel sites. Hackers steal data from these sources and then either sell it or give it away on the dark web. The dark web is a small, hidden corner of the deep web that requires special software to access, and that’s where things can get dubious. If you need a great Tor VPN, I recommend ExpressVPN — all its servers allow Tor traffic, it has excellent security and privacy features, and it provides fast browsing speeds. Despite its anonymity, the Dark Web poses a serious threat to its users. Once you have decided to use the Dark Web, you should take as many security precautions as possible.
Roundup – Best VPNs For Speed
If you get an alert that your personal data, like an email address, password, phone number, or social security number, was found on the dark web, you don’t need to panic, but you should act fast. Always remember that while the above measures significantly reduce risks, no method guarantees complete security on the dark web. Always exercise extreme caution and verify the legality of any services you access. Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage.
Cryptocurrencies And Financial Anonymity
You do not need to learn how to access the dark web to protect yourself from it. That stolen data might include your name, email address, passwords, Social Security number, driver’s license info or payment details. You may not think your Netflix login is a big deal, but reused passwords across accounts can be a goldmine for hackers or a clue about how you construct all your passwords. Your data doesn’t end up on the dark web by accident; it’s there because a company you’ve done business with was breached.
How To Remain Safe When Using Darknet Browsers
It used to be that technological advancements were the main factor that motivated hackers. Malicious hackers on the dark web use various advanced techniques to perform cyber attacks, security breaches, and compromise data. The dark web is always evolving, and that goes for the types of users it attracts. Below are some of the nefarious characters found roaming the dark web hallways today, according to ID Agent.
Where Can I Find Safe Onion Links?
- There’s no application process for becoming a relay manager — anybody who meets the technical specs can run a Tor relay.
- Are Wi-Fi hosts and owners able to see what you’re doing online?
- It has billions of sites and addresses, it is amazing that we can both search for – and find – anything.
- Right-click on the downloaded file and select “Extract Here.” Once the Tor Browser setup files have been extracted, double-click on “Tor Browser Setup” to install the browser.
- When you’re finished, make sure to close your browser before disconnecting from your VPN.
- While not mandatory, using a VPN adds an extra layer of privacy and security by hiding Tor usage from your internet service provider.
It uses anonymity-focused programs like the Tor browser and encrypted connections to hide your IP address and browsing history. Because of this, it is challenging to determine your location or identity when using .onion websites or interacting on their forums. It’s very important to make sure you are on the correct website when using Tails, as there may be malicious websites with similar addresses. To ensure maximum privacy, users should set their security level to “safest” and disable JavaScript.
The Danger Of Tor Network

This process ensures that internet service providers, or anyone looking at the connection, cannot track a user’s internet activity (including the websites they visit). Dark web sites are hidden by non-indexing, making them completely anonymous. You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content. Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions.
How To Tell If A Porn Site Is Safe?
I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Others are looking for stolen data, hacking services, or even banned books and political content.
Illegal Streaming Sites
However, you should be very careful where you go and what you do there. Several secure email providers, such as Riseup and Mailbox.org, provide onion sites for users who want to add an extra layer of privacy and anonymity to email communications. This isolates any potential malware and prevents cross-contamination with your personal data. Using Tails OS can further security, as all your data is reset every time you close the device.

Your data is encrypted in the Tor browser before reaching the ZeroBin servers. Formerly known as Archive.is, it is one of the best onion sites on the dark web. It aims to preserve the internet’s scientific and cultural heritage. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network.
There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains.
How To Setup Free VPN On Windows 10
- So, that means that the number of pages increased by over 100 trillion in just over three years.
- You can’t access “.onion” sites through regular browsers like Chrome and Firefox.
- A VPN’s ability to hide your Tor usage from your ISP and from government authorities makes for a valuable addition to your online privacy arsenal.
- Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it.
- Services like Random Chat connects you with random people using the same service.
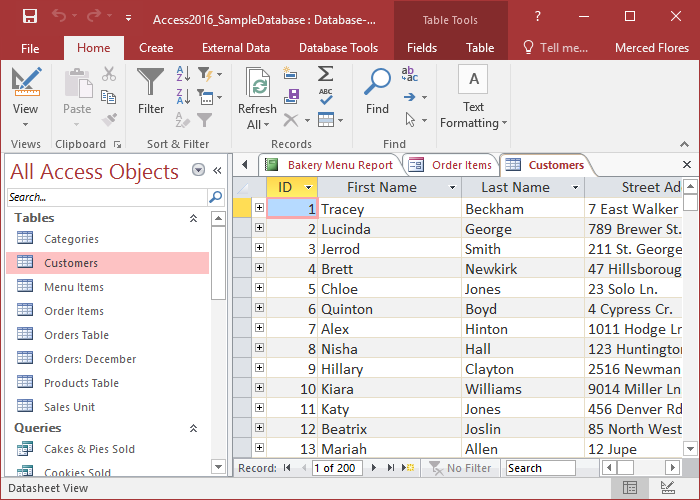
- You can use dark web monitoring services or free tools like haveibeenpwned.com to check if your email, passwords, or other personal data have appeared in known dark web data breaches or dumps.
Some people opt for a virtual machine (VM) or a live operating system (such as Tails) that runs off a USB stick and leaves no trace once you shut it down. Most dark web sites are unregulated, which means that there are fewer mechanisms in place to prevent you from accidentally downloading malware. It’s a good idea to connect to a trusted VPN before you even open the Tor Browser to access the dark web. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails. The major advantage of using a live OS such as Tails is that, on shut down, the OS wipes itself from the thumb drive you’ve installed it.
After it is leaked, first comes the blackmail, hackers threatening to send your porn history to your employer or spouse unless you pay up. People have lost jobs, marriages have ended, and careers have been destroyed. All because their data got caught in a breach they couldn’t prevent.
These “onion” sites are only accessible on the dark web and bear the “.onion” domain at the end of the URL. This is no different from the “.net” or “.com” of the regular Internet. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. Having trouble deciding what dark web sites are safe and reliable? Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else.
Learn what a dark web scanning service is, how it works, its pros and cons, and why monitoring—not just scanning—is essential for real protection. If the above dark web statistics and trends have alarmed you in any way, that’s perfectly valid. But that doesn’t mean there isn’t something you can do about it. By following the tips and recommendations outlined in this blog post, you’ll be in a far better position than most to defend yourself against cybercrime on the dark web.