Addressing these risks requires clear regulations, effective monitoring, and collaboration between regulators and blockchain developers. Implementing compliance measures and leveraging technology can help balance privacy with security. A well-structured approach ensures transparency while preserving the benefits of decentralized finance without hindering innovation.
Privacy Wallets

To stay safe on the dark web, use a reliable VPN, avoid clicking on unfamiliar links, confirm URLs, and never provide personal information. Onion sites are websites on the dark web that use the ‘.onion’ top-level domain. They require the Tor browser for access, ensuring encrypted connections and anonymous communication. For safer browsing on the dark web, consider Forest VPN to keep your data secure and private. This feature is satisfied when \(\phi _i(t) \le \tau\), where \(\tau\) is the maximum value of mean interevent time. From 2012 to 2016, the largest component of S2S network continuously grows in number of nodes and connections, as shown in Fig.
Block Web Trackers
Once the dispute is resolved, the escrow service will release the funds to either the seller or the buyer, depending on the final decision. If the buyer is awarded a full or partial refund, the funds are returned to their account. In some cases, the escrow service may request additional information or evidence from the buyer and seller to make an informed judgment. This could include photographs, videos, or any relevant documentation to support each party’s claims. As cryptocurrencies gain more attention, individuals and businesses are recognizing the potential benefits of using bitcoin for legitimate purposes. The dark web’s use of bitcoin has served as a catalyst for further exploration and adoption of the technology.
Step 4: Finding A Dark Web Marketplace

Its decentralized nature, absence of a central authority, and encryption techniques made it ideal for anonymous and untraceable transactions. The Dark Web soon became a hotbed for illicit activities, with various marketplaces facilitating the exchange of drugs, stolen data, hacking tools, and more using Bitcoin. A dark web wallet is a cryptocurrency portfolio that operates on the deep web, which is a part of the World Wide Web which is only accessible by special means. Transaction participant’s directly without a need of a middleman or any third-party party involved.
The key is knowing how the system works—and how to outsmart the tools used to track it. Discover the dark website’s hidden layers, its uses, and how to navigate it safely while protecting your privacy. By using Forest VPN in conjunction with Tor, you ensure your activities are double-layered, making it nearly impossible for anyone to trace back your actions. Platforms like Bisq allow trades without a centralized authority, meaning you can transact without revealing your identity. Chainalysis provided an update to its 2021 report on Aug. 16 and the 2022 data has shaped up in an interesting way.
Conclusion: Staying Informed And Secure In The World
Then, we investigate both market star-graphs and user-to-user networks, and highlight the importance of a new class of users, namely ‘multihomers’, who operate on multiple marketplaces concurrently. Specifically, we show how the networks of multihomers and seller-to-seller interactions can shed light on the resilience of the dark market ecosystem against external shocks. Our findings suggest that understanding the behavior of key players in dark web marketplaces is critical to effectively disrupting illegal activities. The Dark Web is a vast and anonymous online marketplace where illicit activities and transactions take place. Operating in this hidden realm comes with inherent risks, including scams, counterfeit goods, and unreliable sellers.
- If not, fake wallets can send your data to hackers or steal your Bitcoin entirely.
- Most people who own bitcoin do so as an investment rather than as money–a medium of exchange.
- It is important to note that communication with the escrow service should be conducted securely on the Dark Web.
- Whether you’re a student seeking study-enhancing nootropics, or a septuagenarian with limited internet skills but a need for pain relief, this article is for you.
- Then, during 2017 and 2018, it shows the structural change due to operation Bayonet, when it shrinks.
- Opting for Forest VPN ensures your privacy remains intact while browsing the dark web.
Step 5: Regularly Update All Privacy Tools
It allows users to engage in online transactions without the fear of their personal information being compromised. This can be particularly beneficial in regions where internet censorship is prevalent or in situations where individuals want to avoid government surveillance. The dark web is a hidden part of the internet that can only be accessed through special software, such as Tor. It is a collection of websites and online platforms that are not indexed by search engines and require specific knowledge or access to enter. This unique characteristic makes the dark web an appealing space for those seeking privacy and anonymity. Exploring Bitcoin on the dark web can be a risky endeavor, as it is fraught with potential dangers.
Advantages Of Using Bitcoin In Dark Web Transactions

By the age of 14 she would finish the New York Times crossword puzzle every day of the week. Periodically, the door would open, the light would turn on, and a petite, dark-haired graduate student named Sarah Meiklejohn would enter the room and add to the growing piles of miscellaneous artifacts. Then Meiklejohn would walk back out the door, down the hall, up the stairs, and into an office she shared with other graduate students at the UC San Diego computer science department. One wall of the room was almost entirely glass, and it looked out onto the sunbaked vista of Sorrento Valley and the rolling hills beyond. She was wholly focused on the screen of her laptop, where she was quickly becoming one of the strangest, most hyperactive Bitcoin users in the world. All of it began when a young, puzzle-loving mathematician named Sarah Meiklejohn started to pull out traceable patterns in the apparent noise of Bitcoin’s blockchain.
- Silk Road was utilised by its users as a black market for all types of (in most countries) illegal activities, like buying and selling drugs, credit card data or even guns and other weapons.
- These exchanges often use privacy-focused technologies, such as mixing services and coin tumblers, to obfuscate transaction traces and enhance privacy.
- Law enforcement agencies have begun collaborating internationally to share intelligence and resources.
- This openness ensures no one can alter or fake transactions, which is great for security—but bad for privacy.
The use of Bitcoin in Dark Web transactions provides a level of anonymity, making it difficult for law enforcement to track these transactions. Escrow services and tumblers are used to add an additional layer of security to these transactions. However, these transactions come with significant risks, including the possibility of fraud and legal repercussions. Bitcoin remains the most widely used cryptocurrency, thanks to its popularity, widespread acceptance, and relatively easy accessibility.
This makes Bitcoin an attractive currency for those looking to carry out illegal activities on the dark web. Bitcoin mining, a crucial process for validating and recording transactions on the digital currency’s decentralized blockchain, requires significant computational power. As the popularity of cryptocurrency has surged in recent years, so has the demand for mining equipment and energy. However, some individuals and organizations have found a way to exploit the dark web’s anonymity and privacy features to engage in illicit mining activities.

Selling On The Black Market

Unauthorized access to sensitive information, data breaches, and identity theft are constant threats. If you value digital privacy, you should take the necessary precautions, such as anonymously paying for online items and services. By implementing these safety measures, you can enhance your security and protect yourself when using escrow services on the Dark Web. While no method is foolproof, exercising caution, staying informed, and taking proactive steps can significantly reduce the risk of being a victim of scams or fraudulent activities. It is important to follow the instructions provided by the escrow service precisely when depositing funds. It’s also crucial to ensure that you are using secure payment methods and verifying the authenticity of the escrow service to protect against fraud or scams.
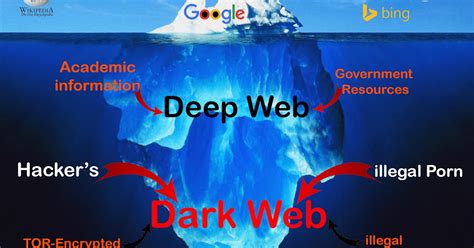
Transactions may not only lead to financial loss but also result in purchasing illicit goods that could have legal repercussions.Phishing schemes are rampant as well. Unsuspecting users might find themselves lured into traps disguised as legitimate platforms, leading them straight into cybercriminal hands.Malware poses another threat. Downloading files or software from dubious sources can compromise devices and personal information without any warning. The Dark Web is a part of the internet that isn’t indexed by traditional search engines.
As we delve into this underground network, we find that the allure of making money on the Dark Web is both a tantalizing prospect and a perilous endeavor. To access sites in the Darknet, users need to use special software such as the Tor Browser as they are on an encrypted network to hide the identities of the people running the sites and services connected to them. Two ways Monero makes its users’ identities and transactions anonymous and secure are ring signatures and stealth addresses. Monero is one of the Best Anonymous Payment Modes for anonymous cryptocurrency payments.
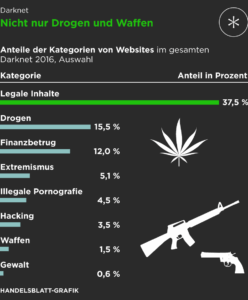
As law enforcement agencies crack down on illegal activities on the dark web, money laundering schemes utilizing cryptocurrencies emerge as a growing concern. Cryptocurrency, particularly Bitcoin and Monero, plays a significant role in facilitating transactions for illicit goods and services. The most popular items purchased with cryptocurrency on the dark web are drugs, such as cannabis, cocaine, and MDMA. However, the dark web marketplace also offers a wide range of illegal offerings, including stolen credit card data, hacking tools, and counterfeit identities.