Hence, you’ll see accurate search results similar to searching on Google. You can download the Tor browser from the official website, Torproject.org. There is no official Tor version for iOS because Apple requires all iOS browsers to use WebKit, which affects Tor’s privacy features. Initially created to protect U.S. intelligence communications, Tor was released for public use in 2003. In 2004, the Naval Research Laboratory then released the code and made it open-source. Since then, volunteers and sponsors around the globe have maintained Tor and the Tor Browser.
- If you do proceed, arming yourself with knowledge and taking every precaution are the keys to staying safe in this shadowy corner of the internet.
- In 2004, the Naval Research Laboratory then released the code and made it open-source.
- The reason why the deep net provides this level of privacy for website hosts is that the .onion address that you use to access the website obfuscates the actual IP address of the server.
- Although there’s a Google Play Store entry for the Tor Browser’s Android app, you’re always safer going the slightly longer way around.
- This means you can use ExpressVPN’s proprietary protocol, Lightway, for the best possible speeds when using Tor to browse the dark web.
What Is Onion Routing, And How Does It Work?
As mentioned, Tor servers are completely concealed from regular internet browsers. However, by connecting to them using the Tor browser you can easily access them in a completely private and anonymous manner. Regular browsers like Firefox and Chrome can’t access this concealed portion of the internet, because they are not designed to find websites listed using The Onion Router hidden service protocol. Using NordVPN or even ExpressVPN or PIA seems to be beneficial for many users.
Step 1: Download Hyphanet

This is a completely separate form of internet that can’t be accessed by typical search engines. The anonymity that the dark web provides attracts criminals, hackers, and malicious entities. Visiting dark websites can expose users to malware, ransomware, and phishing attacks, putting personal and financial information at severe risk. Securing a VPN and choosing your overlay network has you in the final stretch for accessing the dark web safely.
Use A VPN To Stay Safer On The Dark Web
Onion sites are websites hidden inside the Tor network, and only the Tor browser can access them. Many popular websites, such as Facebook and DuckDuckGo, have Onion versions, so check if yours has one. If so, it’s better to use the onion address instead of the standard one.
Freenet: Best Config Setup For Safety

In this guide, we will walk you through the steps to access the dark web using DuckDuckGo on the Tor browser, ensuring your safety and anonymity throughout the process. Welcome to the dark web, a mysterious and uncharted corner of the internet that offers both intrigue and danger. Contrary to popular belief, the dark web isn’t inherently evil or illegal, but rather a hidden network that provides privacy and anonymity for online activities. Instead, use disposable email services and end-to-end encrypted communication tools like ProtonMail or Signal.
Using Tor Browser FAQs
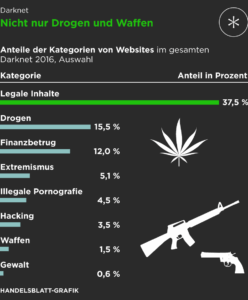
Windows users simply need to double-click the exe file and walk through the installation wizard. According to dark web expert and author Eileen Ormsby, the dark web comprises only about 5% of the total internet. But that small slice receives an outsized amount of attention due to its association with illicit activities.
A VPN automatically encrypts your data as soon as it leaves your device through the VPN server. This means your private information, location, and any communications you send are hidden and protected. The first rule for accessing the dark web is to go into it with a purpose or a defined goal.
- To reduce the risk of these threats, it’s highly recommended to disable JavaScript when browsing dark web sites.
- Ultimately, the dark web can be a place of great intrigue, but it’s essential to approach it responsibly.
- If you do need to create or use any dark web accounts, use dark web email addresses.
- Sections of the dark web are often closed down too, as part of police operations.
- Advocacy groups are also reaping the advantages of the darknet because, here, the term of censorship is as popular as HTTPS.
- This means your private information, location, and any communications you send are hidden and protected.
Dark Web Links: The Best Onion And Tor Sites In 2025
The encrypted data, such as WhatsApp messages, is secured behind end-to-end encryption and is not visible to your ISP. While a website can’t identify you or an ISP can’t decrypt your internet traffic; still, they can still see you using Tor, which can draw some unwanted attention and raise suspicions. Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent. The Darknet offers a place of free expression where not even a chunk of these limitations exists.
Your information might be on the dark web if it was exposed in a data breach, sold, or stolen by hackers. To check, you can use dark web scanning or breach detection tools like Avast Hack Check or LifeLock Breach Detection to search for compromised data. If found, take immediate steps to secure your accounts and personal information. As always, protect yourself from online threats with mobile Android security or iOS security software.
Step 3: Use Best Practices For Privacy
The “VPN-over-Tor” approach offers added protection, even if Tor is compromised. Research of the dark web is legal as long as national or international laws are not broken. When you’re done, clear your browsing history, power down your machine, and ensure no traces of your session remain. Ever felt like a file or folder should be there—but you can’t find it?

Is The Tor Browser Safe Without A VPN?
Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. Internet providers and websites can detect when Tor is being used because Tor node IPs are public. Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used. Officially, the Tor Browser is only available on Windows, Mac, Android, and Linux.
To avoid that you will need to set up your browser as well as your VPN to protect against such leaks. The dark web presents various threats, including malicious software and computer viruses, posing risks to users’ systems and data security. Users also face the potential danger of government monitoring and surveillance — or scams and fraud, and other activities that can lead to financial loss and identity theft. As such, it’s important to be extremely careful when accessing the dark web, as you could inadvertently access a site containing, displaying, or linking to illicit content in some form.
Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. Get Avast BreachGuard for Mac to protect your privacy and keep your personal data from falling into the wrong hands. Get Avast BreachGuard for PC to protect your privacy and keep your personal data from falling into the wrong hands.