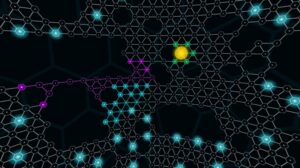
In fact, a recent judgment by the US Supreme Court denoted that simply using Tor was sufficient probable cause for law enforcement to search and seize any computer around the world. Internet providers and websites can detect when Tor is being used because Tor node IPs are public. Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used. Tor is a network of volunteer relays through which the user’s internet connection is routed. The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous. By following these steps, you’ll have I2P and Hyphanet set up for secure and private browsing on the dark web.
Want To Browse Anonymously?
On the internet, Google’s reach barely scratches the surface. So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content. But lurking beneath lies the expansive, mysterious “deep web” or“dark net” – the gigantic submerged part that remains invisible to standard searches. Accessing the Tor network through Tails OS (The Amnesic Incognito Live System) on a thumb drive is a highly secure way to browse the dark web anonymously. Tails is a portable operating system specifically designed for privacy, and it includes the Tor Browser by default.
What Is The Best VPN For Tor?
The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely. For built-in Tor over VPN functionality, NordVPN operates specialized servers that automatically route you through the Tor network. You don’t even need to use Tor Browser, but keep in mind other browsers can still pass identifying information through the network. Alternatively, there’s IPVanish who claim to be the world’s number one VPN for Tor and comes highly recommended, you can save 60% on the annual plan here.
Dark Web Tools And Services

The safest and best dark web browsing tool for Android users is the official Tor Browser APK from the Tor Project site. Not just Tor alone, there are official sites for downloading every similar web browser APK. Always ensure you get your Tor browser or any other software directly from verified sources only, not from third-party sites. When it comes to accessing the dark web (and safely), selecting a good dark web browser is critical. Tor Browser is the #1 in our list above for all the good reasons. We recommend that you use only the Tor browser to access the deep, dark web, if you must.
How To Get On The Dark Web Safely FAQs
Since each node server in the Tor network is volunteer-operated, you never know who operates the relays that your data is traveling through. While this isn’t an issue for most of the trip (since each relay only has access to the previous and next relays in the network), it is an issue with the exit node. Go to the directory where you downloaded the Tor Browser installation file. Right-click on the downloaded file and select “Extract Here.” Once the Tor Browser setup files have been extracted, double-click on “Tor Browser Setup” to install the browser. All of this keeps the sender anonymous thanks to how each intermediary node only knows the location of the previous and next node. In this comprehensive guide, I will endeavor to answer those questions and many more.

Finding Onion Sites
Files on the dark web may contain malware, and it’s best to avoid downloading from unknown sources. Each of these options offers unique privacy features, with Whonix and Qubes for higher security setups, and Kodachi and Liberté for portability. As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with.
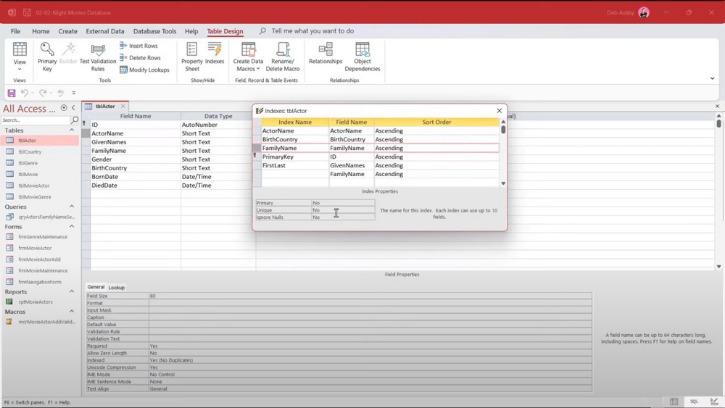
Step 2: Install Hyphanet
I2P must be downloaded and installed, after which configuration is done through the router console. Then individual applications must each be separately configured to work with I2P. You’ll need to configure your browser’s proxy settings to use the correct port on a web browser. The dark web has no shortage of criminal activity, scams, phishing sites, suspicious links, and malware designed to trick newbies.
Is Tor Safe
While there are numerous VPN services that work well with Tor, I’ve found that NordVPN offers the best protection and compatibility, and keeps your personal information safe. A secure VPN server slows down your browsing much less than the Tor Browser and also opens access to geo-blocked local content around the globe. This makes it a great option for watching videos from streaming services that are available only in other regions of the world. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you.
- You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web.
- Of course, I absolutely don’t support underage (stuff) and illegal drugs, passport and stuff.
- Analytics Insight is an award-winning tech news publication that delivers in-depth insights into the major technology trends that impact the markets.
- And yes, unfortunately, those seeking to perform criminal acts also use it.
- For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources.
Remember to update the Tor Browser regularly to ensure you have the latest security patches, and scan your computer for malware regularly using antivirus software. The deep web is every part of the internet that is not indexed by search engines, like private messages from your social media or your online banking portal. The dark web is a small section of the deep web that is hidden on purpose, requiring specific software to access. Unlike Tor, however, it cannot be used to access the public internet. It can only be used to access hidden services specific to the I2P network.
There are marketplaces where people can sell stolen credit card numbers, conduct illegal drug transactions, and scam people out of their cash and crypto. The deep web is the next layer, and it encompasses a massive amount of online data that is not available for public consumption and not indexed by clear web search engines. Deep web content includes academic research papers, court documents, or medical records.
The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources. Signal is our Editors’ Choice for private messaging apps because it does a great job of blending privacy and social media functionality for a highly customizable chat experience. If you need to use a computer and do not want to leave evidence behind (like a digital ghost), Tails is the best tool. While it’s not a browser, it includes Tor Browser installed by default that provides anonymity for web browsing and enables users to access the dark web. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network.
If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security. Additionally, Dread builds technical know-how among budding cybercriminals with its guides on carding, malware development, and hacking tutorials. Experienced fraudsters and drug traffickers use Dread to connect with partners and customers. Most onion sites are run by amateurs and are thus going down temporarily/permanently all the time.
Commercial Services
Yes, Tor-capable browsers are available for both major mobile platforms, Android and iOS. The dark web is a refuge for information leakers and whistleblowers. Edward Snowden used the Tor global network on a regular basis.