This allows you to make anonymous and secure transactions with our online store. Explore our vast selection of high-quality cypher darkweb and cypher darknet url at unbeatable prices. Enjoy fast, secure delivery and our commitment to customer satisfaction. Understanding the intricacies of this challenge on HackTheBox will elevate your cybersecurity skills. Cypher introduces you to the world of cryptography and graph database vulnerabilities, including various query techniques. Mastering Cypher involves deciphering encrypted messages, exploring directories, and exploiting server weaknesses.
This Domain Name
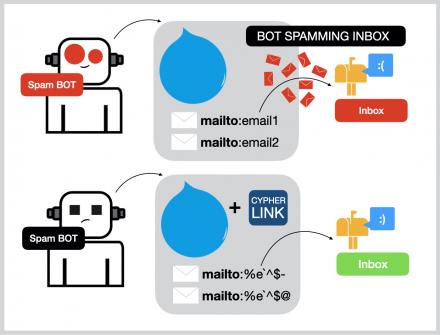
This system protects login credentials, bank details, and server access with heavy encryption and deeply isolated environments. By leveraging multi-layered encryption and secure protocols, even intercepted data is rendered indecipherable. Built for modern infrastructures, this solution integrates seamlessly into your organization’s IT framework, offering a robust shield against data breaches. With respect to Drupal, encryption/decryption of field values happens over ‘Cypher Link’ field-formatter. And currently, it has support for Links, Email, Text and Integer field types.
Non-linear Patterns
The domain will stay with Atom until you have completed all payments. However you can begin using the domain immediately after your first payment. Our team will assist you with any changes to the Domain settings. Once the domain has been fully paid off, we will transfer the domain to your ownership. Several of our domains offer payment plans, which allows you to make smaller monthly payments to purchase the domain. This is a great option if you are looking to minimize your upfront costs.
Discover The Best Cypher Darkweb For Your Needs At Our Store

Grant DROP INDEX privilege to drop indexes on a specified database to the specified role. Grant START privilege to start all databases to the specified role. Revoke ACCESS privilege to access and run queries against the home database from the specified role. Grant ALL DATABASE PRIVILEGES privilege for all databases to the specified role. Deny REMOVE LABEL privilege for all labels on a specified graph to the specified role.

Grant REMOVE PRIVILEGE privilege, allows the specified role to remove privileges for roles. Grant ASSIGN PRIVILEGE privilege, allows the specified role to assign privileges for roles. Grant ALTER ALIAS privilege to alter aliases to the specified role. Grant SET USER STATUS privilege to alter user account status to the specified role.
- Using the keyword IF NOT EXISTS makes the command idempotent, and no error will be thrown if an attempt is made to create the same constraint twice.
- List range indexes, can also be filtered on ALL, FULLTEXT, LOOKUP, POINT, TEXT, and VECTOR.
- The protocol’s contracts are now frozen as contributors attempt to make contact with hackers to negotiate a return of funds.
- Regularly the database is updated and new ciphers are added which allows to refine the results.
- Query the relationship vector index review-embeddings for a neighborhood of 10 similar reviews to the vector given by the query parameter.
Our Core Values
While there is a matching unique Person node with the name Oliver Stone, there is also another unique Person node with the role of Gordon Gekko and MERGE fails to match. While there is a matching unique Person node with the name Michael Douglas, there is no unique node with the role of Gordon Gekko and MERGE, therefore, fails to match. Similar to MATCH, MERGE can match multiple occurrences of a pattern.If there are multiple matches, they will all be passed on to later stages of the query. Cypher is one of the fastest-growing protocols on the solana blockchain in part because of its loyalty program, which rewards depositors and traders with points that many users expect is the setup for an airdrop.
Type Predicate Expressions

Additionally, familiarize yourself with an instance of gogs and cryptographic concepts to decipher codes and progress through challenges more efficiently. Embrace these tools and techniques to enhance your skills in conquering Cypher challenges seamlessly. As Charlie Sheen and Oliver Stone do not know each other in the example graph, this MERGE query will create a KNOWS relationship between them.The direction of the created relationship is left to right. As of Neo4j 5.20, specifying a property of an entity (node or relationship) by referring to the property of another entity in the same MERGE clause is deprecated. Grant SHOW PRIVILEGE privilege to list privileges to the specified role. Grant SHOW ALIAS privilege to list aliases to the specified role.
Source Code
Grant MERGE privilege on all properties, on all nodes with a specified label in all graphs, to the specified role. Grant SET PROPERTY privilege on a specified property, on all relationships with a specified type in a specified graph, to the specified role. Revoke MATCH privilege on all graphs and all nodes with either foo_label or bar_label and with a secret property that is null from the specified role.
Grant RENAME USER privilege to rename users to the specified role. Grant USER MANAGEMENT privilege to manage users to the specified role. To remove a granted or denied privilege, prepend the privilege query with REVOKE and replace the TO with FROM; (REVOKE GRANT ALL ON DBMS FROM role_name). Deny STOP privilege to stop the home database to the specified role.
Additionally, the page’s title is a triangle symbol “△”, and an eye emoji as its favicon “👁️”. Multi-layered defense against sophisticated cyber threats with real-time monitoring. Good community forums are the most reliable sources of verified access information.
Cypher is Neo4j’s declarative and GQL conformant query language.Available as open source via The openCypher project, Cypher is similar to SQL, but optimized for graphs. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps.
Remember, thorough reconnaissance lays a solid foundation for successful exploitation. The Cypher planner is not able to leverage indexes with index scans or seeks and must instead utilize the AllNodesScan operator, which reads all nodes from the node store and is therefore more costly. Because the Person node named Keanu Reeves already exists, this query does not create a new node.Instead, it adds a timestamp on the lastSeen property. Grant ALTER DATABASE privilege to alter standard databases the specified role. Grant SET USER HOME DATABASE privilege to alter the home database of users to the specified role. Grant CREATE INDEX privilege to create indexes on a specified database to the specified role.
Cypher Market has swiftly emerged as a significant entity within the darknet’s commercial landscape, acclaimed for its clean, minimalist aesthetic that places a high emphasis on user experience. Adhering to strict ethical guidelines, especially by excluding certain illicit materials, Cypher establishes a benchmark for conscientious management. Despite hosting a relatively modest vendor base, it boasts an extensive selection of rare and distinctive items, outperforming conventional market assortments. Explore online platforms like HackTheBox forums, Reddit’s hacking communities, and cybersecurity blogs for a wealth of resources on tackling challenges similar to Cypher. Engage in discussions, follow tutorials, and leverage tools, including anyone’s email address shared by the cybersecurity community, to enhance your skills with the app.
Merge With ON MATCH
Each cypher website and cypher darknet market we offer is carefully selected and rigorously tested to meet the highest standards of excellence. Our team of experts is dedicated to providing you with the best possible products and ensuring your complete satisfaction. Welcome to our cypher onion online store, where we pride ourselves on providing our customers with a seamless and enjoyable shopping experience. With years of expertise in the industry, we have dedicated ourselves to curating a wide selection of high-quality products that cater to your every need. Our mission is to become your go-to destination for all your cypher tor shopping needs, offering unparalleled convenience, competitive prices, and exceptional customer service.
Grant SHOW CONSTRAINT privilege to list constraints on a specified database to the specified role. Grant SHOW INDEX privilege to list indexes on all databases to the specified role. Grant INDEX MANAGEMENT privilege to create, drop, and list indexes for all database to the specified role. Revoke DELETE privilege on all nodes and relationships in a specified graph from the specified role. Deny TRAVERSE privilege on all graphs and all nodes with the specified label and with a secret property not set to false to the specified role.