For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. These settings can be found in the Router Console’s configuration panel. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. When you’re done surfing or shopping on the dark web, don’t forget to shut down Tails.
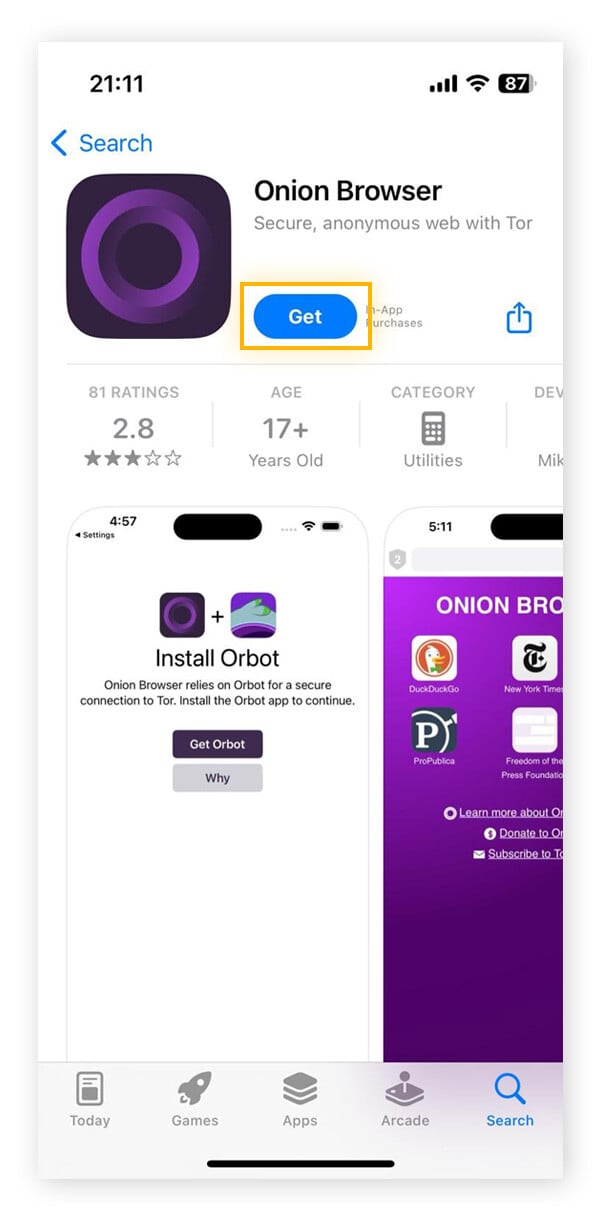
Step 2: Download The Tor Browser
- Installing the Tor Browser is the best way to access the dark web.
- You will also be browsing the internet in a true anonymous fashion – the onion routing capability of Tor will protect your ip address from servers and snoopers.
- Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis.
- It can only be used to access hidden services specific to the I2P network.
- Identifying specific individuals who use the dark web can be quite tricky.
If you can’t get a personal recommendation from someone you trust, verify the URL from multiple sources. If you want to use Tor privately, you can use either a VPN or Tor Bridges (Tor nodes that are not publicly indexed). Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. Based on Firefox, the Tor Browser lets you surf the clear and dark web.
Is The Dark Web Illegal?
Adding a VPN to it, even a fast one like IPVanish will make it even slower, so please be patient. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method. In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely. When using a VPN for the dark web, your ISP will not be able to see that you are connected to a Tor node, only an encrypted tunnel to a VPN server. Our rigorous research and testing have revealed revealing truths and busted myths.
How Do I Access The Dark Web Safely
If you’re after secure email, look for the Proton Mail service. TorConnect is your trusted guide to navigating the dark web. Stay informed about the latest darknet marketplaces, secure browsing practices, and privacy tools. The dark web offers a fascinating glimpse into a hidden world, but navigating it requires vigilance.
All of this keeps the sender anonymous thanks to how each intermediary node only knows the location of the previous and next node. Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node destination. When the final layer of the “onion” is reached and decrypted, the message arrives at its destination. All Tor Browser data is encrypted and relayed three times over the Onion Router network, which is composed of thousands of volunteer-run servers, which are known as Tor relays. Yes, many organizations monitor the dark web for cybersecurity intelligence—always in line with legal compliance.
How To Access The Dark Web Safely
As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web.
Minimize Or Rescale Your Tor Browsing Window
A VPN, in combination with Tor, further enhances the user’s security and anonymity. Tor is a network of volunteer relays through which the user’s internet connection is routed. The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous. Staying safe on the unregulated dark web requires vigilance, and its seedy reputation, fostered by controversy like that surrounding Silk Road, is well-earned. Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online.
Even in an era of increased online surveillance, the average person on the internet likely has too much to lose to bet on their safety for curiosity’s sake. Heck, I’m one of PCMag’s resident security experts, and I’m not playing around on the dark web just because I know how to. That’s why I’m not going to provide links or detailed instructions for accessing the internet’s shadier side. Designed to be hidden from conventional search engines like Google or Bing, the dark web is a portion of the internet. Access to “.onion” domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only. Well, I’ve gone to the dark web a lot of times and visited almost all the onion links that are available in the search engines (or equivalent things) the dweb has.
What Are The Differences Between Tor Over VPN Vs VPN Over Tor?

The Tor Browser is a popular online anonymity tool among political activists and journalists who fear totalitarian governments monitoring or arresting them. Other users appreciate the browser as it allows them to circumvent censorship. And yes, unfortunately, those seeking to perform criminal acts also use it. For over 40 years, PCMag has been a trusted authority on technology, delivering independent, labs-based reviews of the latest products and services.
- Its main appeal is that it offers more privacy and supports legacy Firefox add-ons.
- All your device’s internet traffic first goes to the VPN server, then bounces through the Tor Network before ending up at its final destination.
- Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive.
- Not only that but I am scared about my private information being used and sold to companies.
Hidden Facebook is hardly the only social media client on the dark web. Check out the list below for the ‘hottest’ dark web clients. Note that the process can take anywhere from 5 to 30 minutes depending on your machine. When you’re ready, hit the Close button and you’re all set. No, you need more than a VPN to enter the dark web safely. There’s no broad consensus on dark web safety, but you at least need to use Tor and VPN together.

Always use an abundance of caution when interacting with anything or anyone on the dark web. Use a computer that is not connected to your home’s internet to protect other computers on your network from malware infections or privacy intrusions. TOR is a web browser, just like Internet Explorer or Firefox. It also provides ‘some’ privacy by mixing your IP address up a bunch so people who track your computer don’t know where you actually live.
Browsing Dark Web Domains On Tor
It is much less populated – but the population is generally more technically savvy. You also have to watch out for scams and fraud – there is no regulation – so keep your wits about you. Using a VPN will hide these details and protect your privacy. This information can be used to target ads and monitor your internet usage. Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences.
Just below the surface is the gigantic “deep web.” Here, you’ll find all things that require a login, like your email, bank account, corporate intranet, government databases, etc. Files on the dark web may contain malware, and it’s best to avoid downloading from unknown sources. Each of these options offers unique privacy features, with Whonix and Qubes for higher security setups, and Kodachi and Liberté for portability. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. Now, if you want to see what lurks in the dark corners of the Internet but don’t really trust Tor, there are alternatives. This multi-layered redirection ensures your actions leave no trace, offering a high level of anonymity.
However, we advise connecting to one of our recommended VPN services to stay anonymous. There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. The dark web allows people to access and share all sorts of illegal and explicit material without judgment or censorship. The best way to find out is to check the “Have I Been Pwned” (HIBP) website. This website allows you to type in your email address or phone number and see if it’s been compromised in any data breaches.
Ensure that you’re aware of what is permissible in your jurisdiction. Do not use any personally identifiable information on the dark web. This includes email addresses, usernames, and payment details. Use aliases and avoid any activity that might reveal your identity. Since .onion URLs can be complex and random, consider bookmarking reliable sites in Tor for easier access. With your VPN active and Tor installed, you’re now ready to connect.