Use aliases and avoid any activity that might reveal your identity. By following these steps, you’ll have I2P and Hyphanet set up for secure and private browsing on the dark web. Both networks have unique strengths, and while they aren’t as user-friendly as Tor, they offer excellent alternatives for those seeking robust privacy and decentralized communication options. Whether you’re a journalist, a privacy advocate, or just curious, this guide will walk you through how to access the dark web safely and responsibly. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details.
I Stopped Getting Lost In Giant Excel Sheets When I Found These Two Features
To surf the web privately, you need to connect to the Tor network from your browser. Manually implies clicking the Connect button each time you open Tor, while automatically means an automatic connection whenever you open the Tor browser. Open the downloaded file on your device to begin the installation process.
First, Install A Reliable VPN
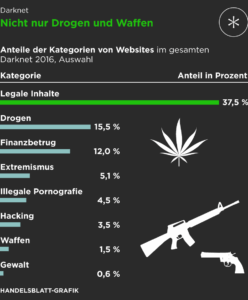
Contrary to popular belief, not all activities on the dark web are illegal. Many individuals access the dark web for legitimate reasons, such as maintaining privacy and anonymity. For example, journalists and whistleblowers may use the dark web to communicate securely and protect their sources.
FreeType Vulnerability (CVE-2025- : A Comprehensive Guide To Understanding And Mitigating The Risk
The clear web is made up of websites that you can get to via a search engine like Ecosia or Google. Your clear web browser activity can be logged and tracked by advertisers, governments, and your ISP if you’re not using a VPN. Given the amount of illegal and unsettling content on the dark web, there is always a risk that you might encounter something that could disturb you.
Is It Illegal To Use Tor?
The dark web isn’t only about illegal activities; its primary purpose is to provide maximum anonymity by making your connection private online through encrypted servers. While the dark web is famously known as an illegal platform for criminal activities, that’s not all about this part of the web. The darknet is a private place where nobody can intercept, monitor, or steal anything online from you. The dark web is a hidden part of the internet that requires a special browser like the Tor browser to access it. Normal search engines like Google and DuckDuckGo don’t index this part of the web due to its illegal nature. Tor’s anonymity has spurred many malicious actors to host dangerous sites on the network, including scams, phishing links, malware, and illegal content.
How Do I Stay Safe On The Dark Web?
In case you’re wondering how to access the deep web, chances are you already use it daily. The term “deep web” refers to all web pages that that are unidentifiable by search engines. Deep web sites may be concealed behind passwords or other security walls, while others simply tell search engines to not “crawl” them.
You can use Tor to spoof your location so it appears you’re in a different country to where you’re really located, just like when you use a VPN service. There’s no such thing as perfectly private or secure on the internet. It’s still possible to track someone’s traffic pinging through the Tor nodes, though it is difficult.
Minimize Or Rescale Your Tor Browsing Window
- Examples of this might be e-mail accounts or registration-only forums.
- However, some of these alleged services, such as professional ‘hitmen,’ may be scams designed to defraud willing customers.
- A VPN will give you an extra layer of protection and anonymity, making it much safer to explore the dark web.
- Staying informed and making informed decisions are key to navigating the dark web responsibly.
- Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators.
Locating surface web websites is possible because search engines can index the web via visible links (a process called “crawling” due to the search engine traveling the web like a spider). Accessing the dark web is easy; you just need the Tor Browser, which connects you to the Tor network where .onion websites live. However, you should be very careful where you go and what you do there. Regardless of why you may need to get on the dark web, protecting your connection and your data is crucial.
We will discuss the setup procedure, ensuring security and anonymity, and offer tips for navigating the dark web safely. It’s essential to follow these guidelines to protect yourself and your personal information when exploring the depths of the internet. Welcome to the dark web, a mysterious and uncharted corner of the internet that offers both intrigue and danger. Contrary to popular belief, the dark web isn’t inherently evil or illegal, but rather a hidden network that provides privacy and anonymity for online activities.
This setup is easy to configure, and you don’t need any special settings or features. Just turn on your VPN, wait for the connection to stabilize, and launch Tor. Your internet activity is still subject to exit node risks, so always use HTTPS and avoid entering any personal information on unencrypted sites. The deep web refers to anything that search engines can’t crawl.1 These pages aren’t public — not because they’re illegal, but because they require a login or special access. Think of your email inbox, banking dashboard, cloud documents, subscription content, or internal business tools. The privacy offered by the Tor browser is important in the current digital age.
You can use third-party tools like Bleach Bit to completely wipe temporary files if you want to go the extra mile for security. After clearing the temporary files, reboot your computer to end any background processes that might still be running after closing the browser. However, since it is so popular, you will find several versions of the program on the internet. These are unreliable copies that can cause you to download malicious content on your computer. That is why you should only download the Tor browser from its official website.
If you choose to pursue exploring any sites on the dark web, you put yourself at risk of being singled out and targeted for hacks and more. Most malware infections can be caught by your endpoint security programs. That said, anonymity comes with a dark side since criminals and malicious hackers also prefer to operate in the shadows. For example, cyberattacks and trafficking are activities that the participants know will be incriminating.

Microsoft Word is one of the best word processors around, allowing you to craft powerful documents with an intuitive interface. If you know how to use Microsoft Word, you’re typically working with large files that span multiple pages. So, you’ll be happy to know there are several easy ways to delete a page in Word, including both blank pages and those you simply no longer need. Due to compatibility issues and technical restrictions imposed by Apple, Tor browser isn’t available on iPhones that haven’t been jailbroken. Onion Browser is typically the go-to alternative for iOS devices and is powered by Tor.
Your best option is to take steps to make sure your information is useless to criminals. For example, it’s a good idea to change your passwords, contact your financial institutions, freeze credit, and set up two-factor authentication. If you get an alert that your personal data, like an email address, password, phone number, or social security number, was found on the dark web, you don’t need to panic, but you should act fast. The dark web was created not long after the first message was sent in 1969 over the original internet, ARPANET. Covert networks — or darknets — emerged quickly and provided users with private networks to communicate. There are countries where access to the dark web is restricted by the government.