These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. The core principle of the Tor network was first developed by U.S.

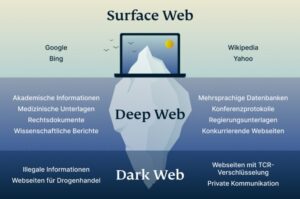
From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine. To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section.
The Risks Involved
Visitors can expect to discover hidden gems and support local artisans while exploring the eclectic offerings at this one-of-a-kind marketplace. We respect your privacy and never track or record any details of your online activity. So, be sure that whatever you do on the Internet—browsing, downloading, and other habits — remains completely confidential. Try using tools like password managers like Keeper, Passbolt, 1Password or others. Also, consider multi-factor authentication apps like Authy for an additional layer of security.

How Online Black Markets Work
- Play the audiograph on the table in the apartment to get the passcode for the shop’s back door.
- Climb through that balcony’s window and walk down the stairs to exit the building, which will leave you on the other side of the locked gate entrance.
- Getting inside to rob the place requires a passcode — and getting the code to the door is a little complicated.
- While many visitors manage to browse hidden services without incident, staying safe requires constant vigilance.
So in the end, hackers will think they’ve got your email, but they will get fooled and you will stay anonymous and safe. VeePN guarantees that your data is secured by the most reliable encryption standard. If a hacker intercepts your traffic, they will see only gibberish instead of distinctive text and won’t be able to decode it. Weak passwords like the date of your birth, “password 123”, and other easy-breezy ones are a criminal’s dream. Make sure you create strong unique passwords for every online account. If you are wondering how to get to the black market, this article is definitely for you.
Rumor: 2025’s Fortnitemares Event Will Be Bigger Than Last Year’s
So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation. Darknet markets — also known as cryptomarkets — provide a largely anonymous platform for trading in a range of illicit goods and services.

How To Get On The Dark Web In 2025: A Step-by-Step Guide
The best thing about those markets is that you don’t have to purchase the supplies sold in them. You can instead rob them all by finding and opening back entrances. This is how you can rob all the black markets in Dishonored 2 to help yourself to their loot. The rewards of getting involved in the black market include higher profits, access to illegal goods and services, and excitement and thrill.
Gameplay Guides
Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. When both buyers and sellers are anonymous, the credibility of any ratings system is dubious. Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s.
Which Darknet Market Is Safe
Before you embark on your journey into the Dark Web, it’s crucial to establish a secure foundation. While the Tor network is designed to provide anonymity, it alone cannot guarantee your privacy or safety. This section will guide you through the essential preparatory steps and tools to ensure that you remain as protected as possible while exploring hidden services and tor onion domains. Darknet Markets are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity by TOR. The products that are most commonly listed for sale include drugs, fake documents, fraud-related items, and hacking services and tools.
Steps To Navigate The Black Market
Players have the chance to exchange items of varying rarity and negotiate prices. Negotiation plays a critical role as each vendor comes with their own terms. Black markets are free markets since there is no government involvement due to their illegal nature. Therefore, there is complete flexibility and freedom between the buyers and sellers within the black market.

Just don’t expect the shopkeepers to take your intrusion very kindly. The Black Market is near the start of the mission, but getting inside to rob them is tricky. To rob the Black Market in Mission 2, you’ll need the backroom key. The path to the back room is behind the vendor storefront, in an alleyway. Ultimately, while the black market may seem alluring to some, the potential consequences outweigh the benefits. Consider exploring legitimate options instead, and remember to prioritize your safety and well-being above all.
The choice of location can significantly impact your browsing experience. Forest VPN provides a plethora of options, allowing users to bypass geo-restrictions and access content from different parts of the world. This flexibility is not just about entertainment; it’s about accessing a global treasure trove of information. Getting involved in the black market comes with both risks and rewards.

WANT TO TRY THE TOP VPN RISK FREE?
First, let me explain that this article is intended for users who want to use the dark web for legal and needed purposes, such as finding censored news, blocked websites, and other much-needed services. Rum-running, or bootlegging, is the illegal business of transporting (smuggling) alcoholic beverages where such transportation is forbidden by law. Smuggling is usually done to circumvent taxation or prohibition laws. The term rum-running is more commonly applied to smuggling over water; bootlegging is applied to smuggling over land. Rum’s cheapness made it a low-profit item for the rumrunners, and they moved on to smuggling Canadian whisky, French champagne, and English gin to major cities like New York City and Boston, where prices ran high.
Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. Be warned that this may cause some websites to not work properly. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post. Now that you’ve completed the download, it’s time to install the Tor browser on your device.