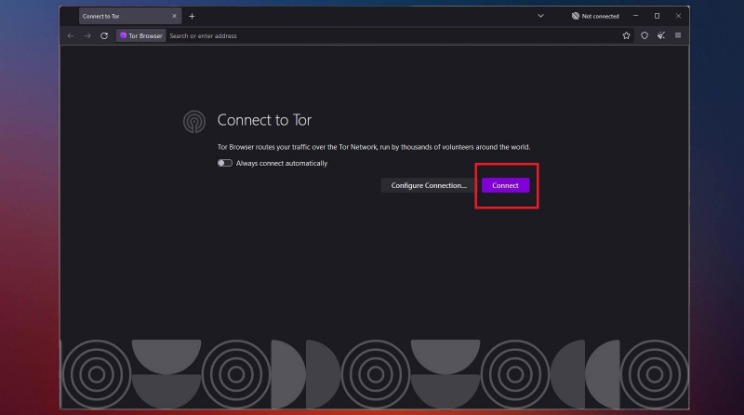
Run the setup file and then simply follow the on-screen instructions. Keeping your VPN and Tor Browser updated ensures you benefit from the latest security patches. Outdated software can have vulnerabilities that may put you at risk. Files on the dark web may contain malware, and it’s best to avoid downloading from unknown sources. Since .onion URLs can be complex and random, consider bookmarking reliable sites in Tor for easier access. With your VPN active and Tor installed, you’re now ready to connect.
Can I Use A Free VPN To Safely Access The Dark Web?
Both methods improve your online security and anonymity compared to not using a VPN. The only challenge is that your speed is slowed because of the limited bandwidth caused by the many nodes your traffic passes through. The VPN provides data encryption and routes your data through remote servers to help mask your IP address and location. Thus, it successfully prevents anyone from snooping during your activity. The Silk Road was a marketplace on the dark web that launched in 2011, where you could purchase all sorts of illegal goods.
Dark Web Monitoring And Identity Theft Protection At Your Fingertips
Another feature that makes it reliable is Onion over VPN, allowing you to use the deep web anonymously. A VPN service helps you remain secure and anonymous by encrypting your data and masking your network address. This prevents cyber criminals prowling the dark web from snooping on your activity. Therefore, to access the deep web, you need passwords to those databases. However, it is filled with malicious actors, so maintaining your privacy is challenging unless you know what to do. Here are all the quick security tips to securely get on the dark web.
How To Access The Deep Web Using Tor
All Surfshark servers are RAM-only and support the WireGuard, IKEv2, and OpenVPN protocols. The company operates a strict no-logs policy and protects internet traffic using AES-256-GCM encryption together with a SHA512 authentication hash and 2048-bit DHE-RSA key exchange. While NordVPN is undoubtedly a great service, it’s not without fault. In 2018, someone gained access to a third-party data center in Finland. NordVPN responded aggressively by upgrading its entire infrastructure to RAM-only servers and ending its reliance on rented servers. It also introduced a bug bounty program, hired a cybersecurity consulting firm to test its infrastructure, and then carried out a third-party security audit.
- The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network.
- The Tor Browser does have its flaws, which we’ll go into a bit later.
- The quickest way to access the dark web is to download and install Tor Browser, which will route your traffic through the Tor network and let you access the dark web.
- The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users.
- Some sites are safe to use, especially those where you don’t need to provide sensitive information to use.
Use A Dark Web Search Engine
If you are curious about accessing the deep web, you are likely already using it daily through pending website redesigns, blog posts under review, and pages accessed during online banking. These pages are hidden for various reasons and do not threaten your computer or safety. The internet is an extensive network of millions of servers, databases, and web pages that run continuously.
How Does The Tor Browser Work?
- Some of these cybercriminals are known to track and blackmail pedophiles.
- Therefore, while accessing dark web links, it is crucial to exercise immense caution.
- What’s more, law enforcement agencies monitor dark web activities.
- You are not required to provide your personal information to create an account.
- You should never trust websites and forums on the dark web with your personal information.
- Many dark internet users favor Tor which uses a network architecture originally developed by the U.S.
It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. Unlike Tor, however, it cannot be used to access the public internet.
onion URL Structure
Malicious actors and government agencies can run Tor nodes, compromising privacy and security. In fact, there have been instances where attackers controlled hundreds of Tor nodes. Many people use it for privacy-focused communication, whistleblowing, or accessing restricted information in censorship-heavy regions. Platforms like SecureDrop even allow journalists to receive tips anonymously. Accessing the Dark Web, a part of the web that isn’t indexed by standard search engines, is not illegal in most countries. People use it for various legitimate reasons, such as bypassing censorship in restrictive countries.
The site offers downloads for macOS, Windows, Linux, and Android. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. Make sure that when you download the Tor file, it’s from their official website. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users.
According to the Into the Web of Profit report, the following services or tools may pose a data compromise or network breach threat. A virtual machine is a file that behaves like your computer while virtually borrowing a dedicated amount of CPU storage and memory from it. It runs in a different environment and is partitioned from the rest of the host system. Therefore, activities within the virtual machine in no way impact your computer. If you get a malware attack, it will remain on the virtual machine and won’t harm your whole device.

Use the tips below to patch common blind spots and avoid easy-to-make mistakes. Don’t log into any real accounts, reuse usernames, or enter any personal details. Treat every site as untrusted unless you’ve verified it from multiple sources. This hides your Tor usage from local networks, masks direct Tor connections, protects against network-level surveillance, and reduces the risk of being flagged for accessing privacy tools. To be on the safe side, we recommend combining the Tor or onion browser with a secure VPN, such as NordVPN.

Freenet is still an experiment designed to resist denial-of-service attacks and censorship. When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity.

Because dark web pages generally aren’t indexed, you can’t find them using traditional search engines, but some search engines like DuckDuckGo may help you navigate the dark web more easily. The Hidden Wiki is a directory hosted on the clear net (also called the “surface web”) that contains a list of .onion links for many of the best dark web websites. To do so, enter a .onion URL and you’ll be taken to the dark web page being served at that address.